analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
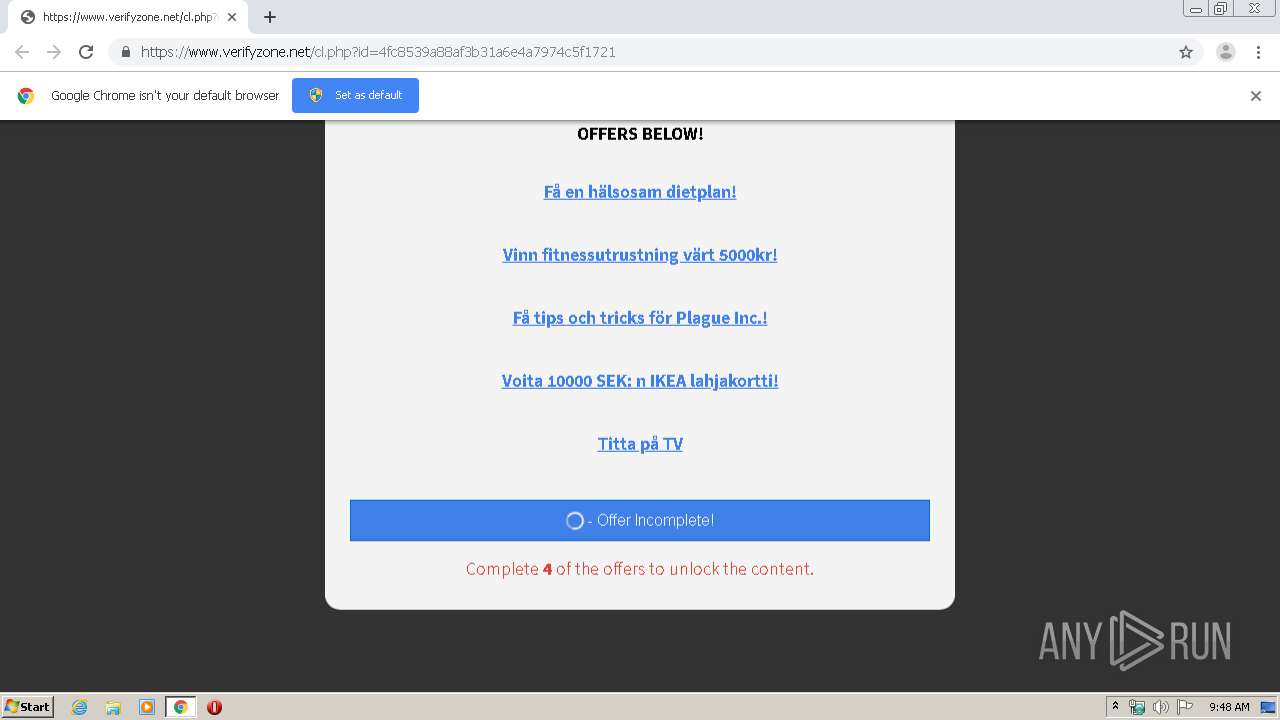
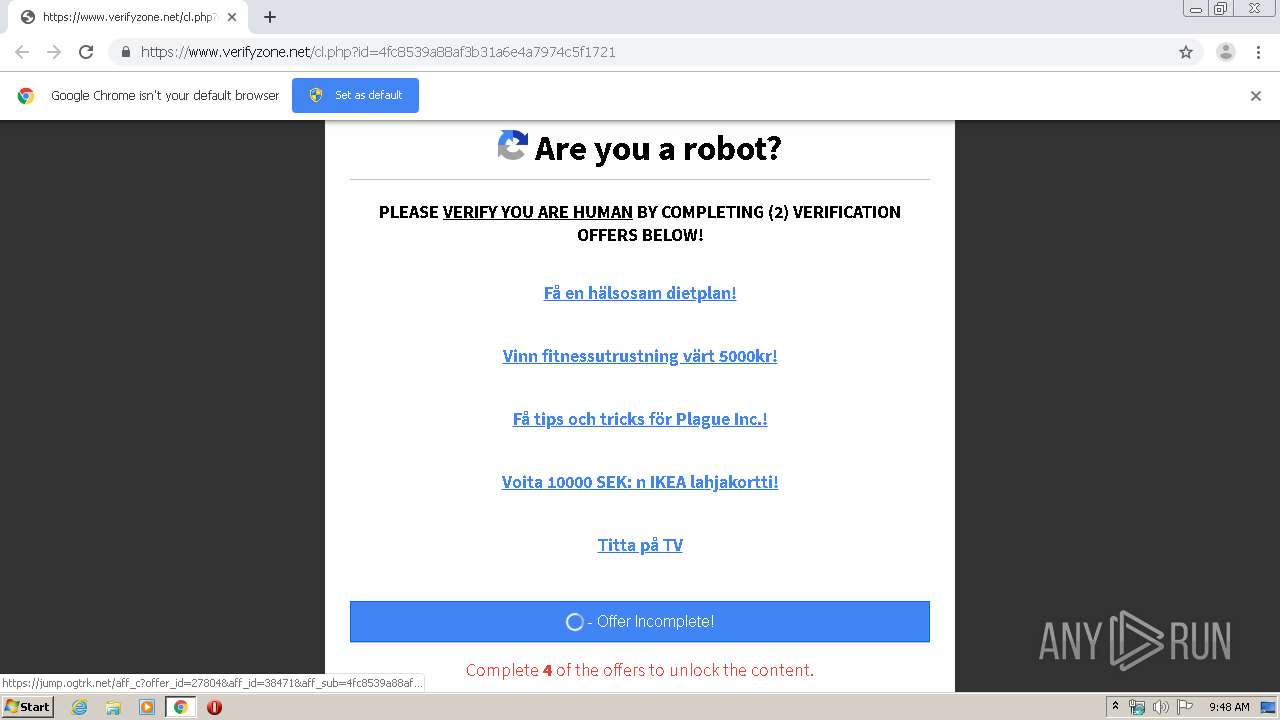
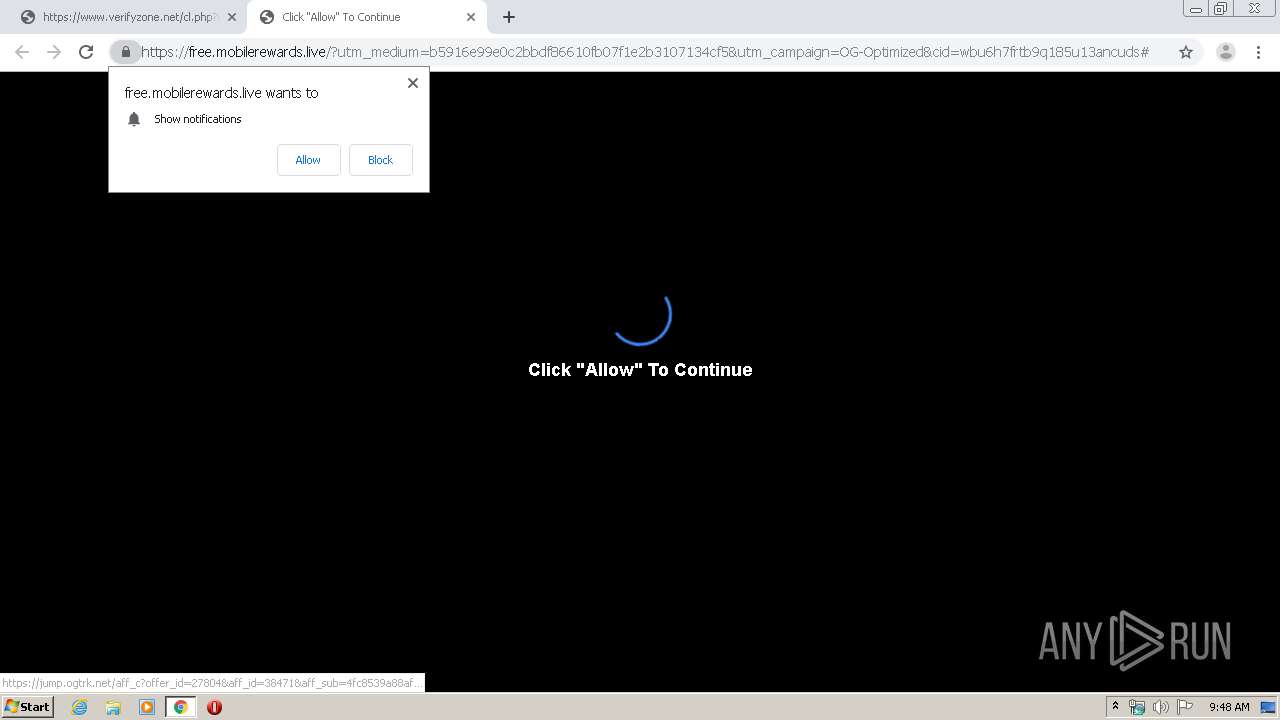
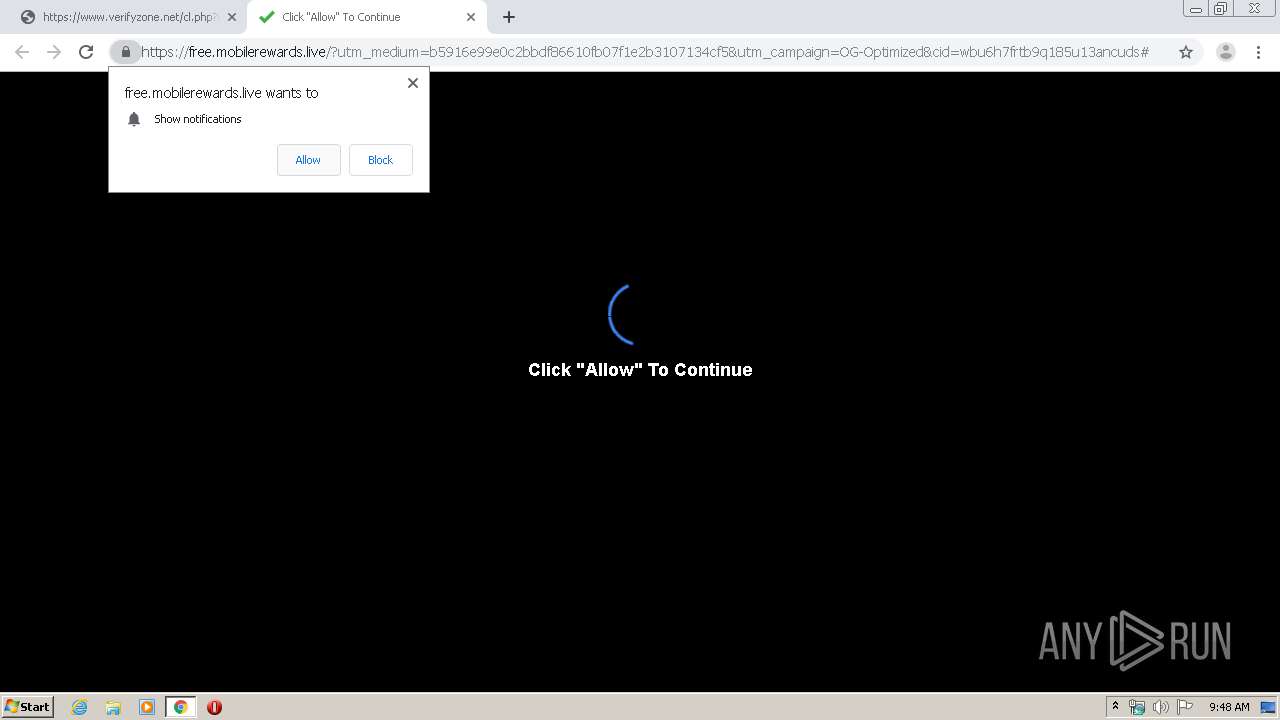
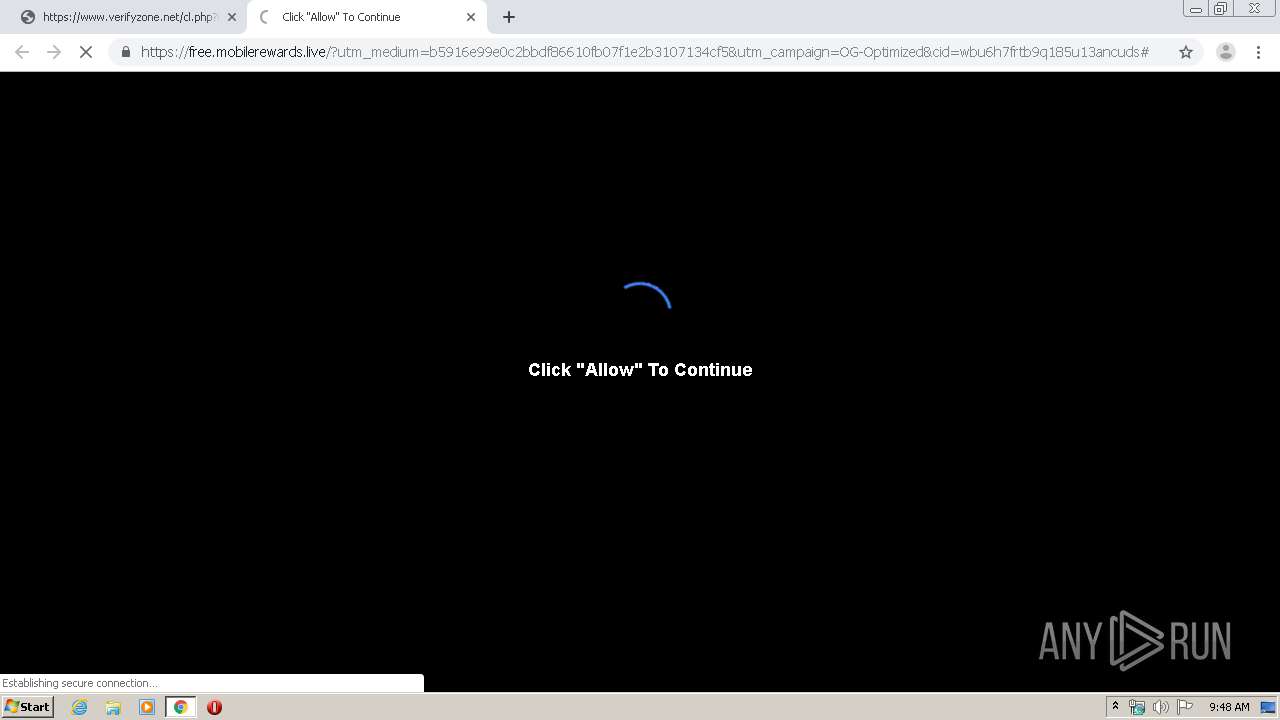
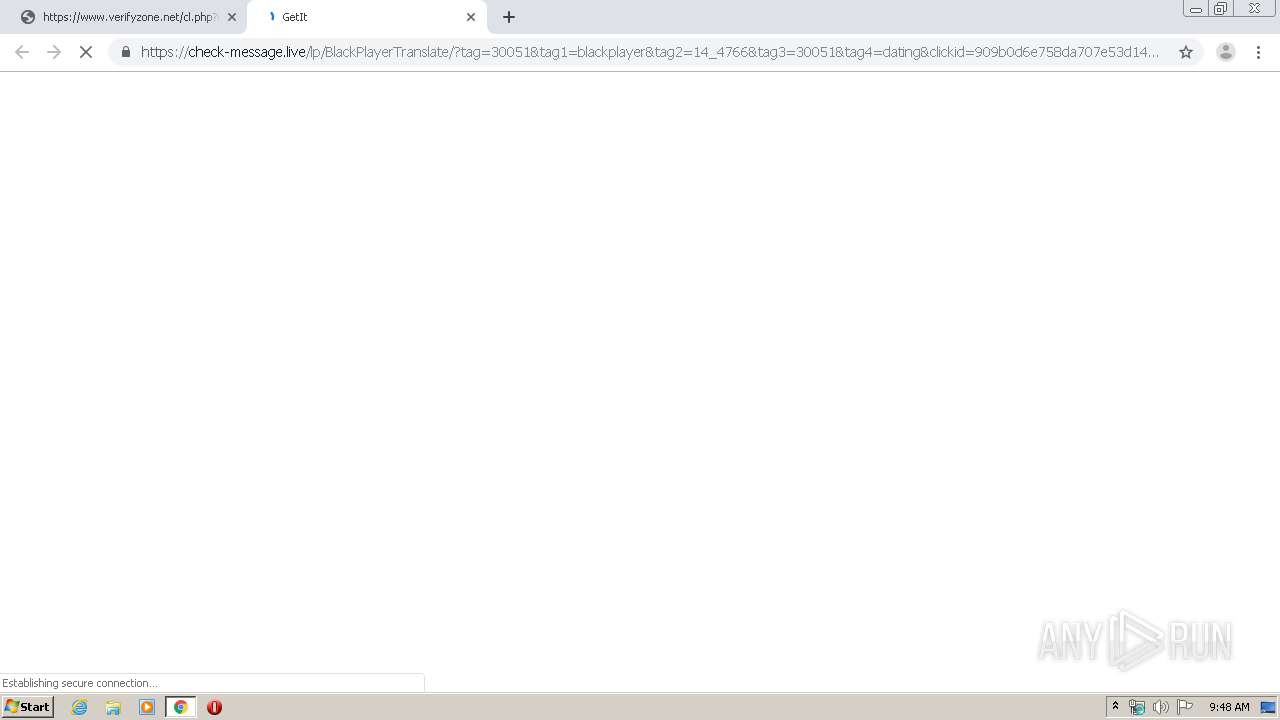
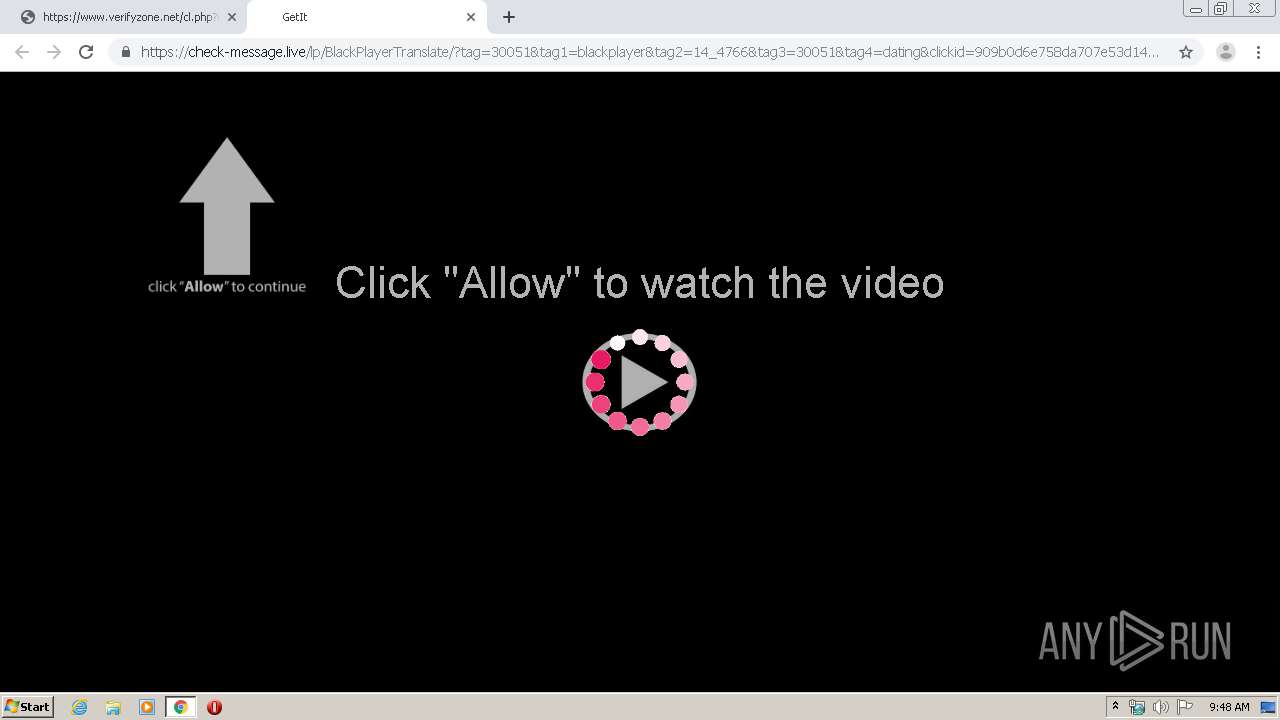
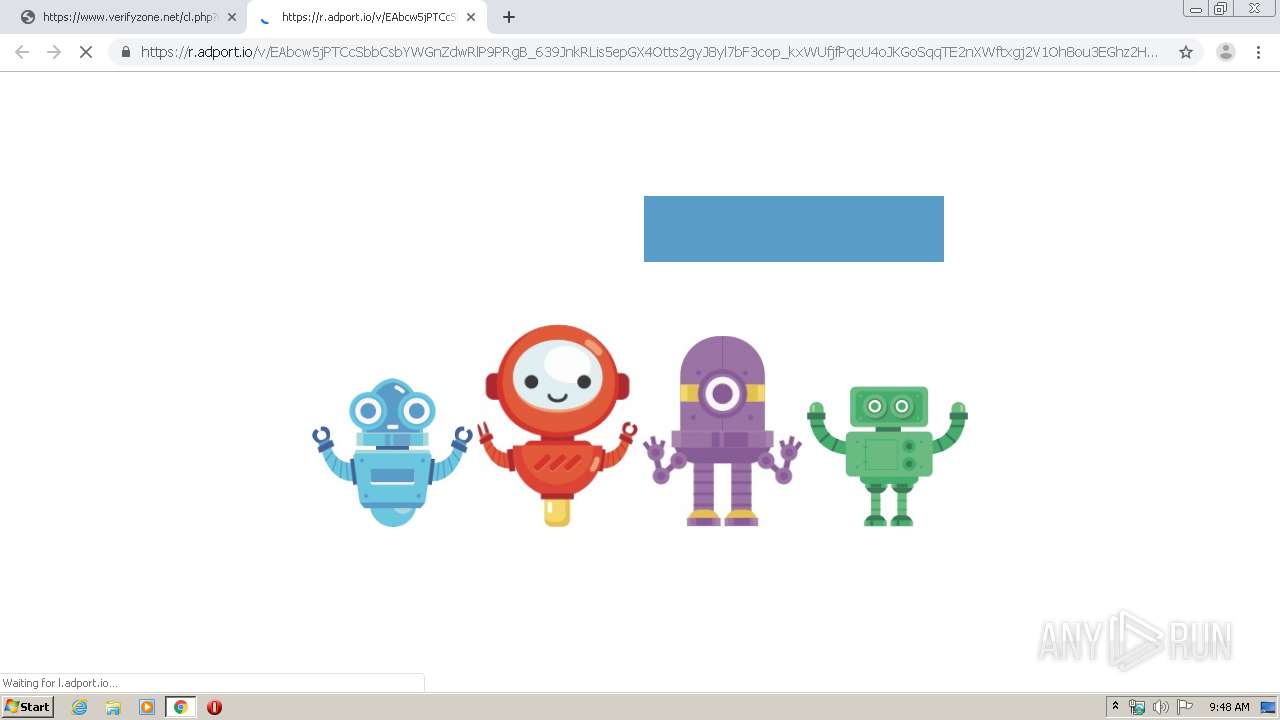
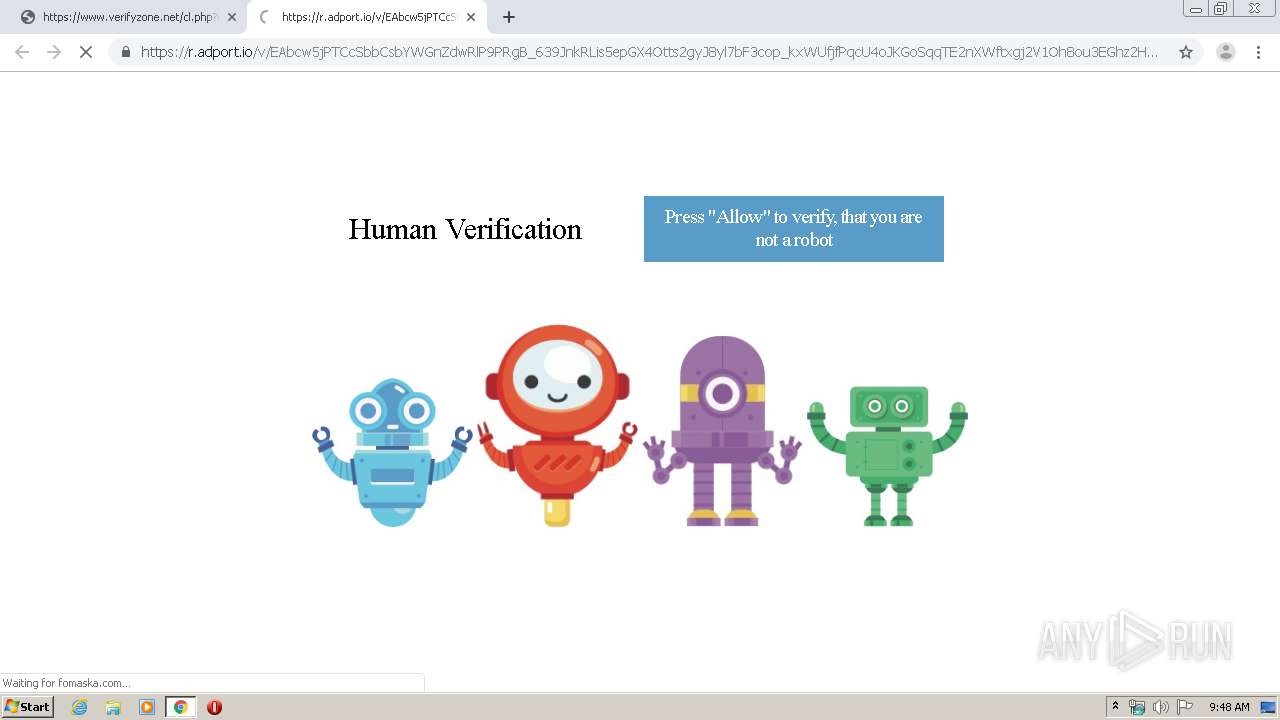
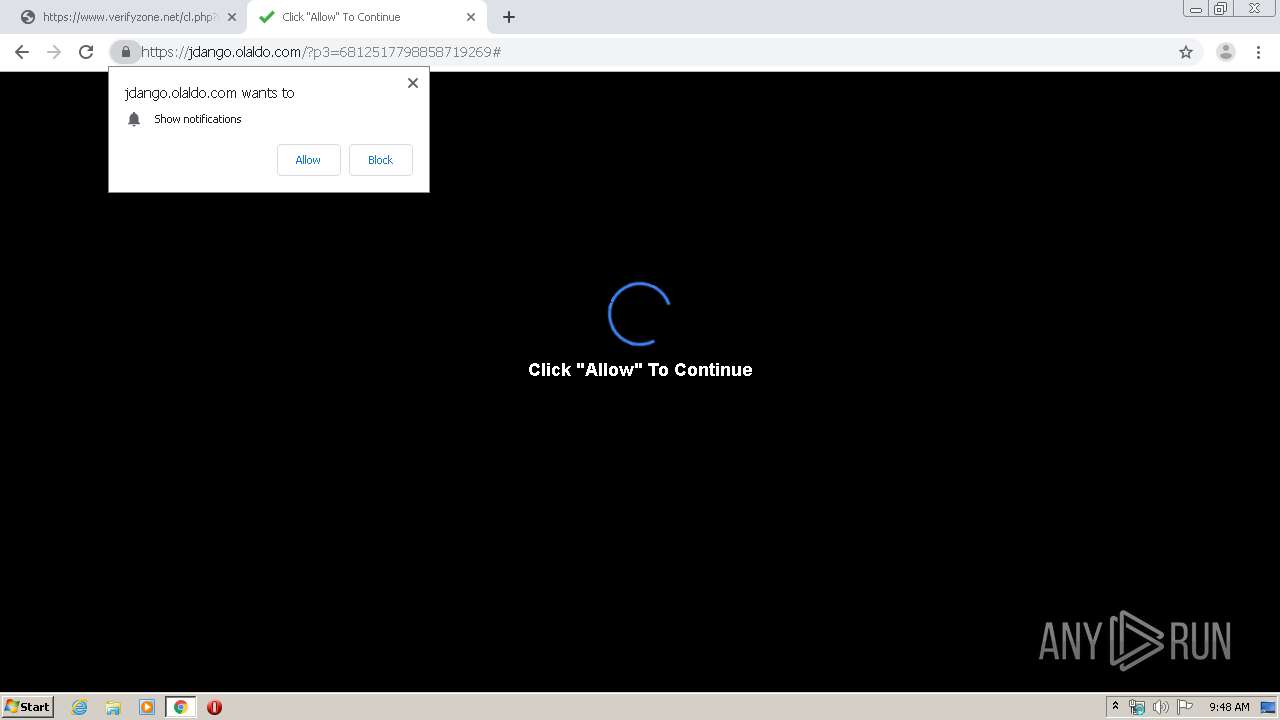
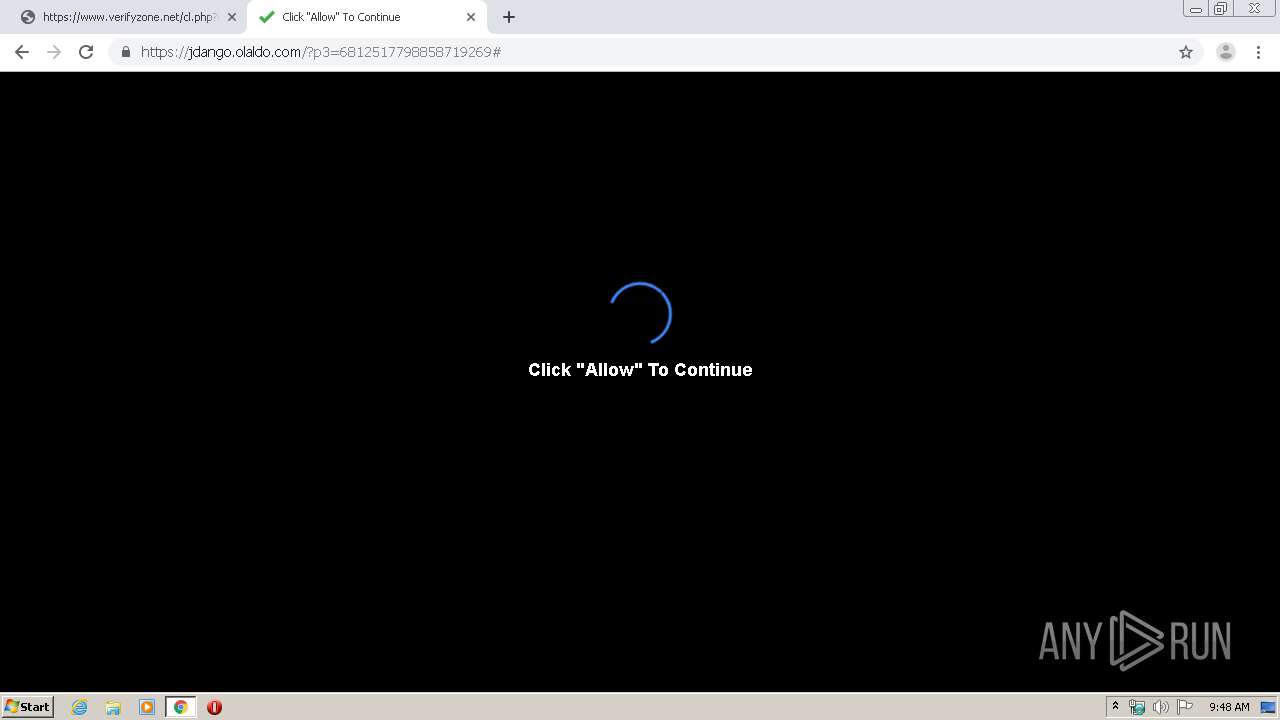
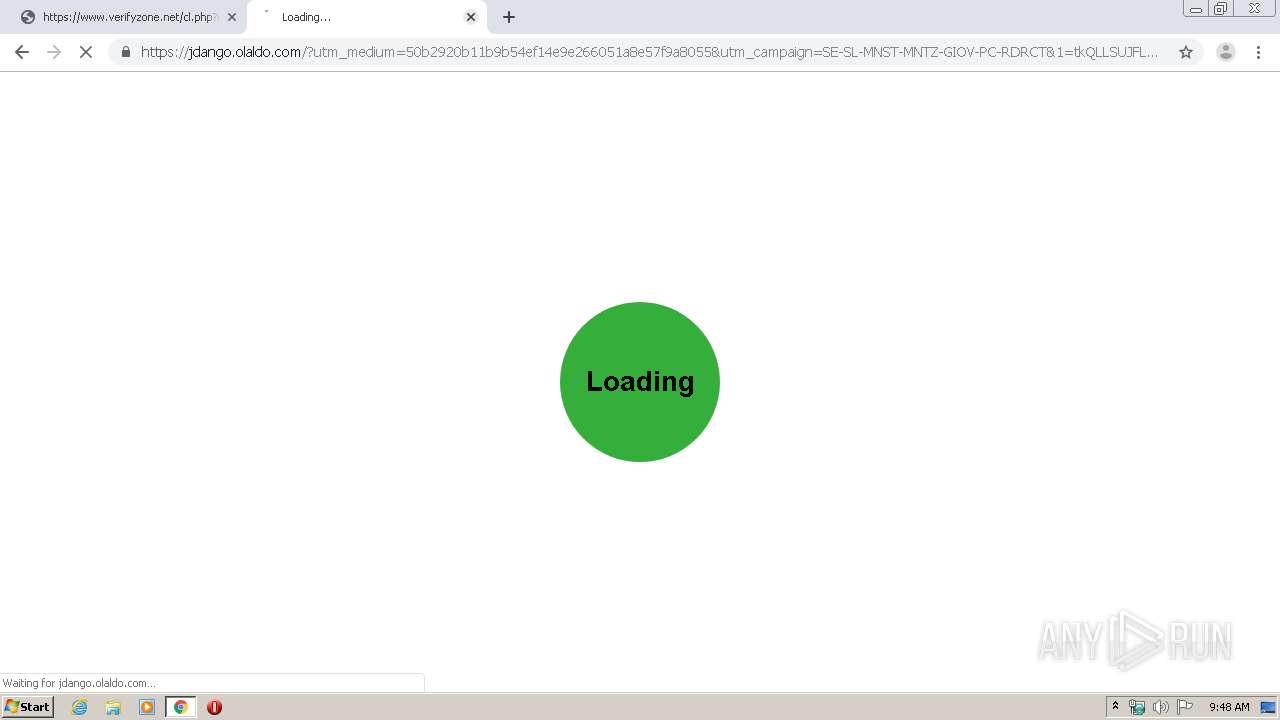
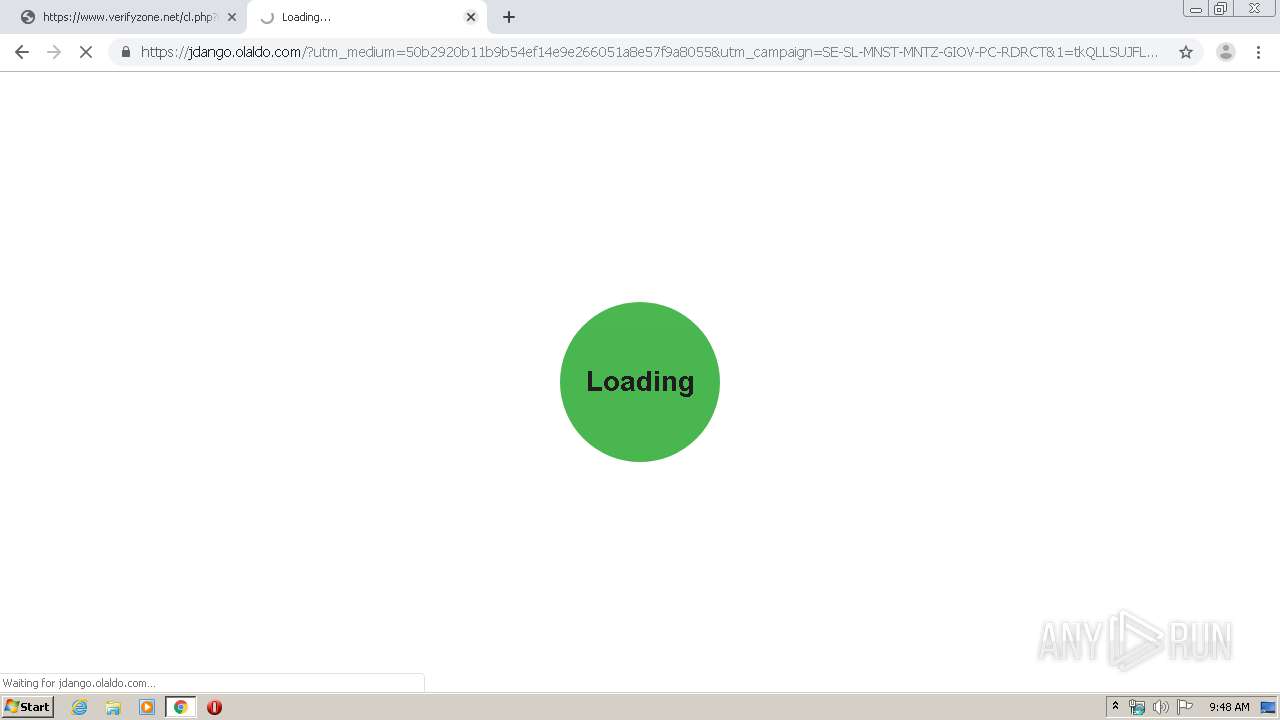
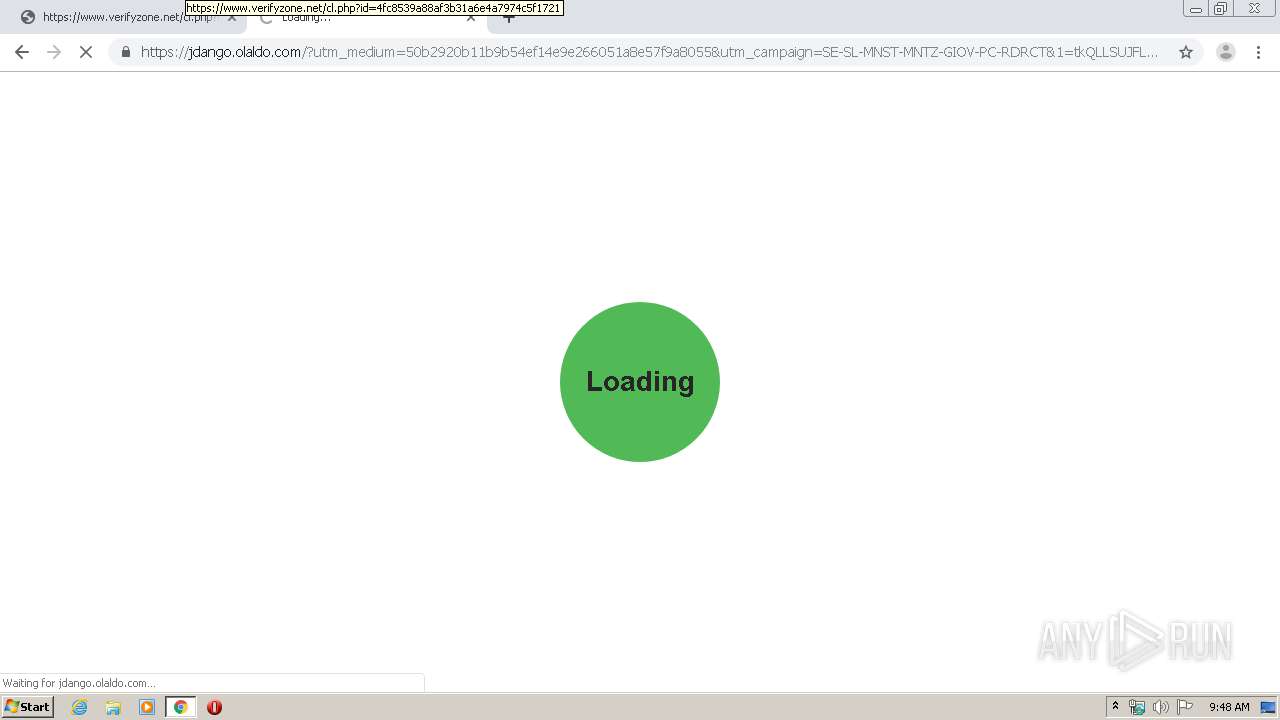
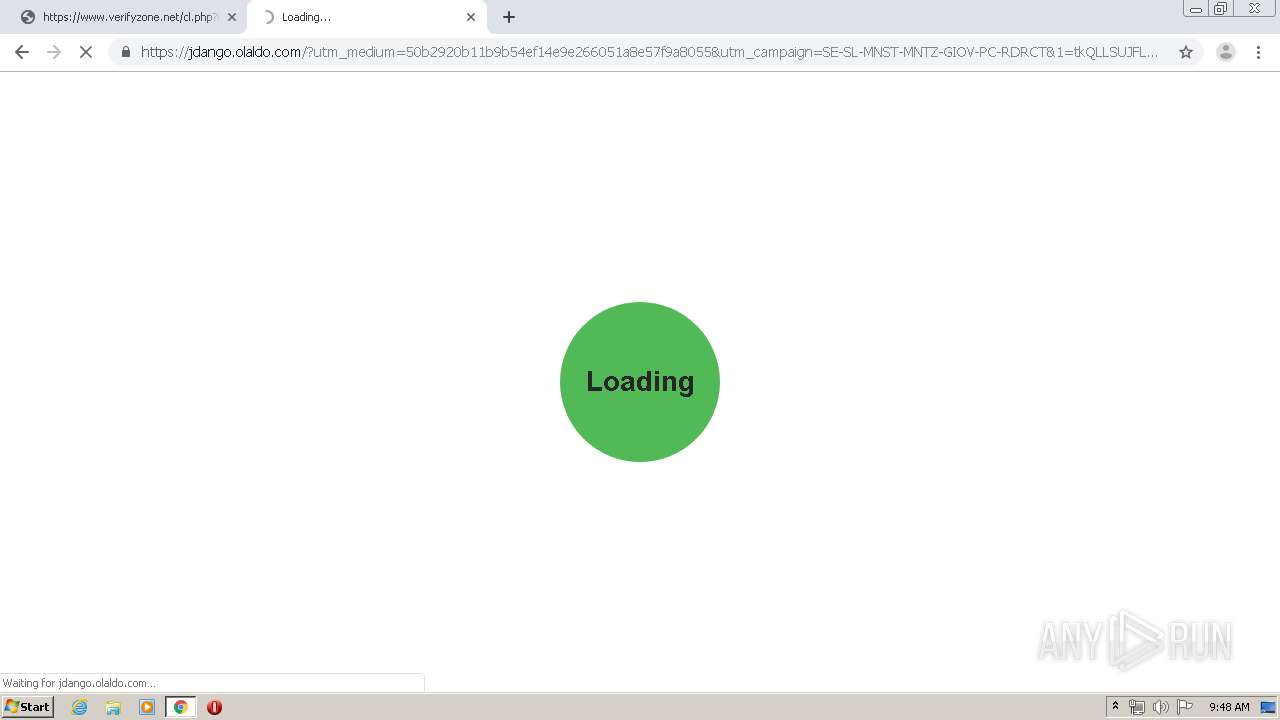
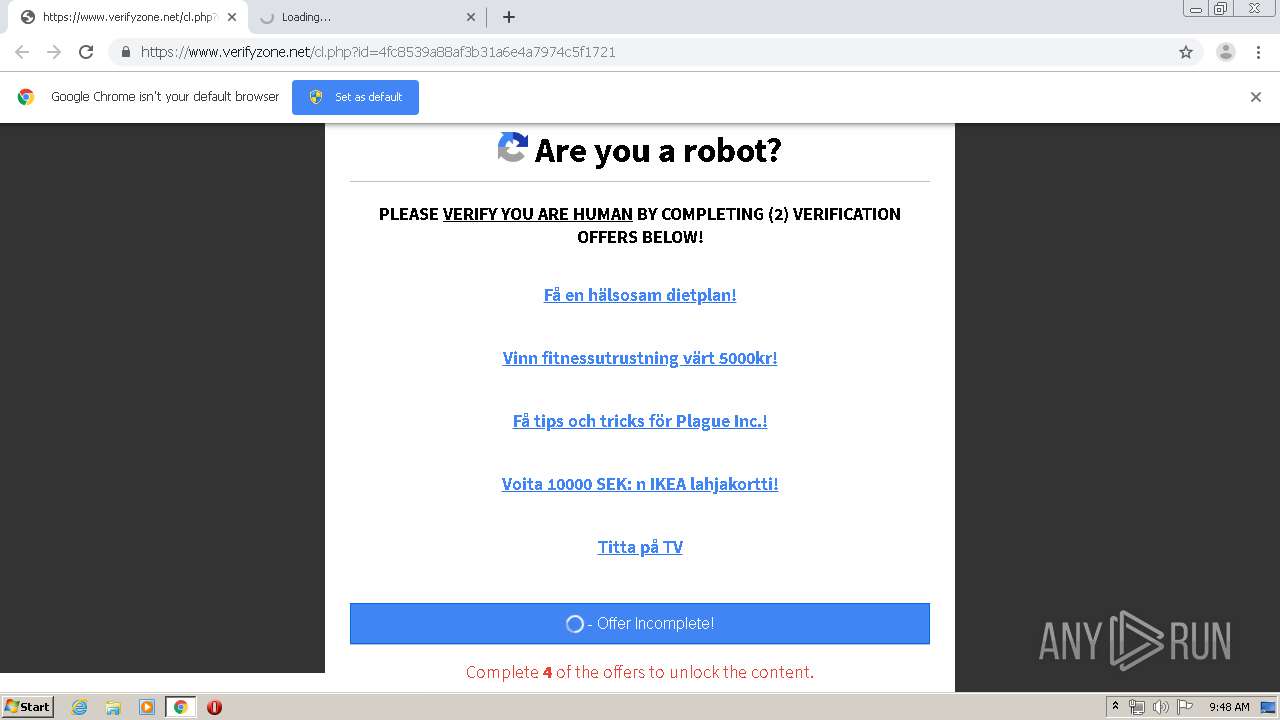
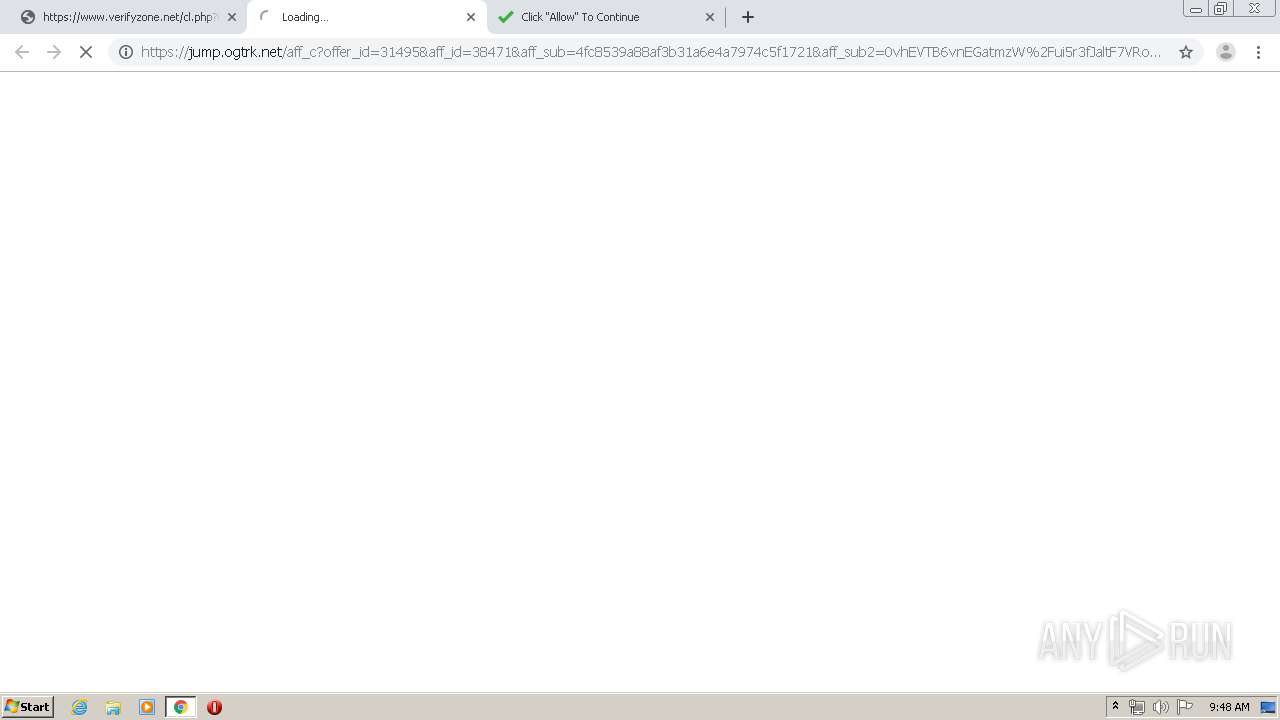
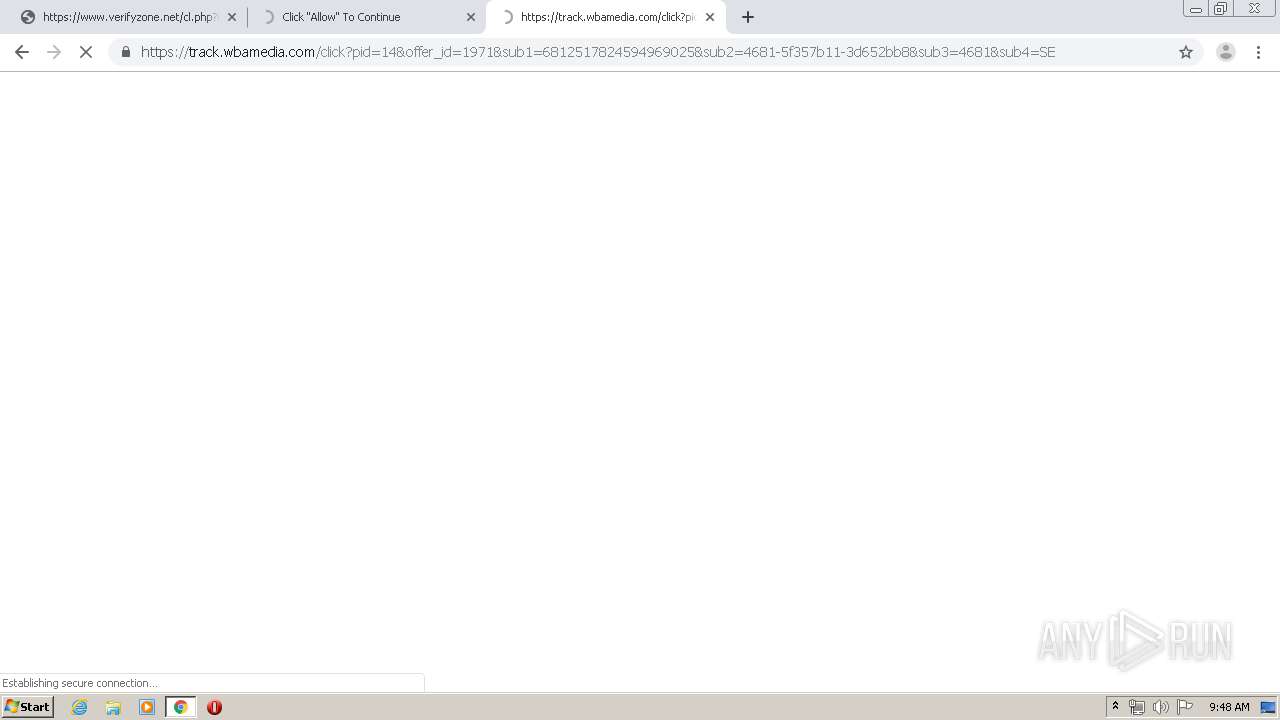
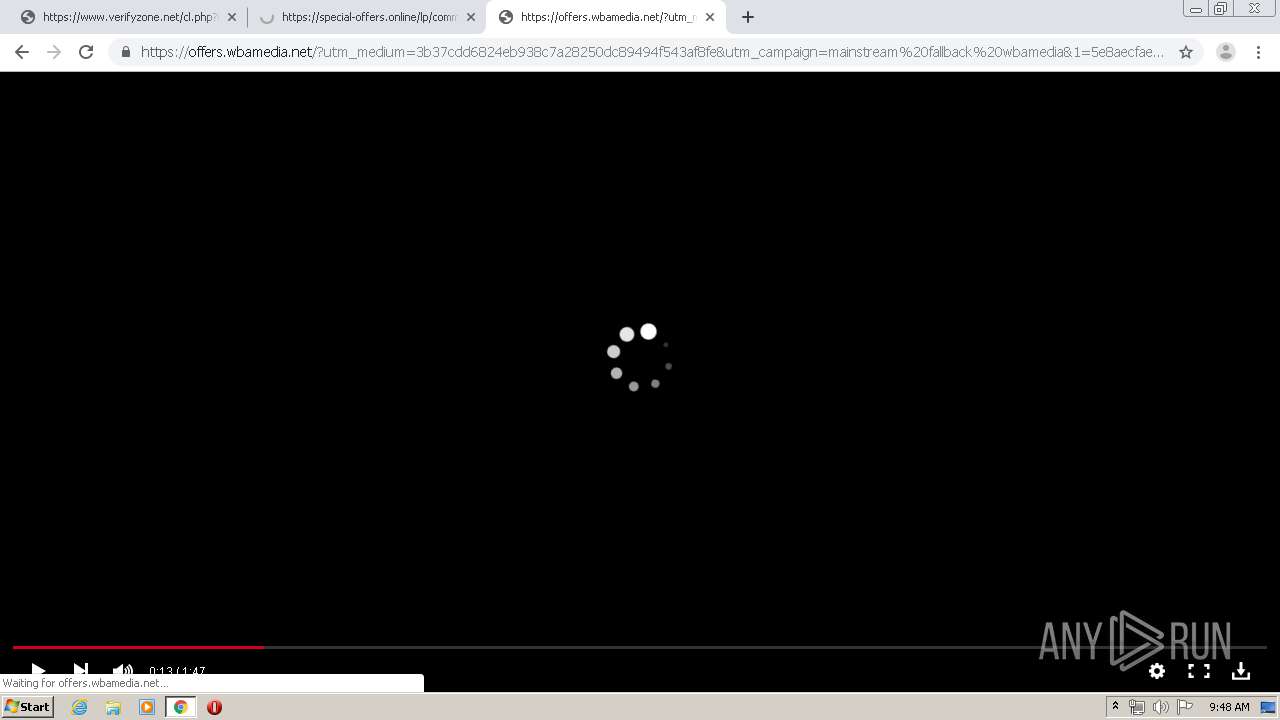
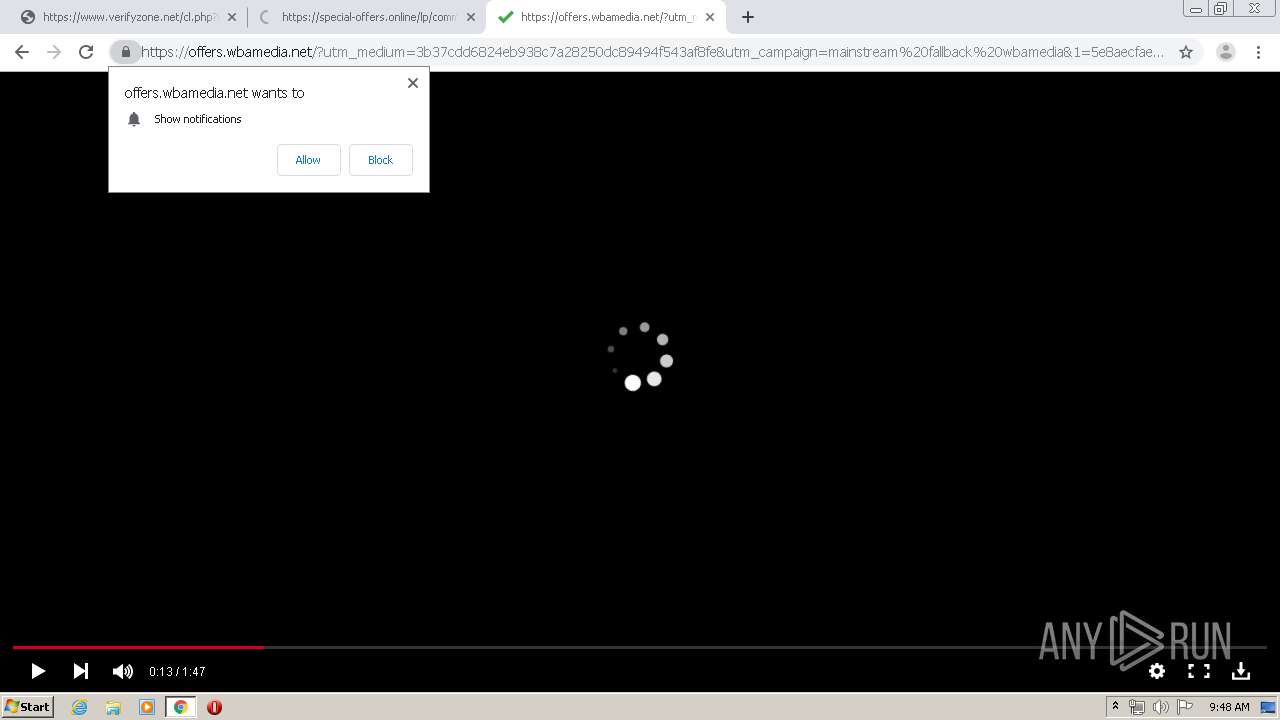
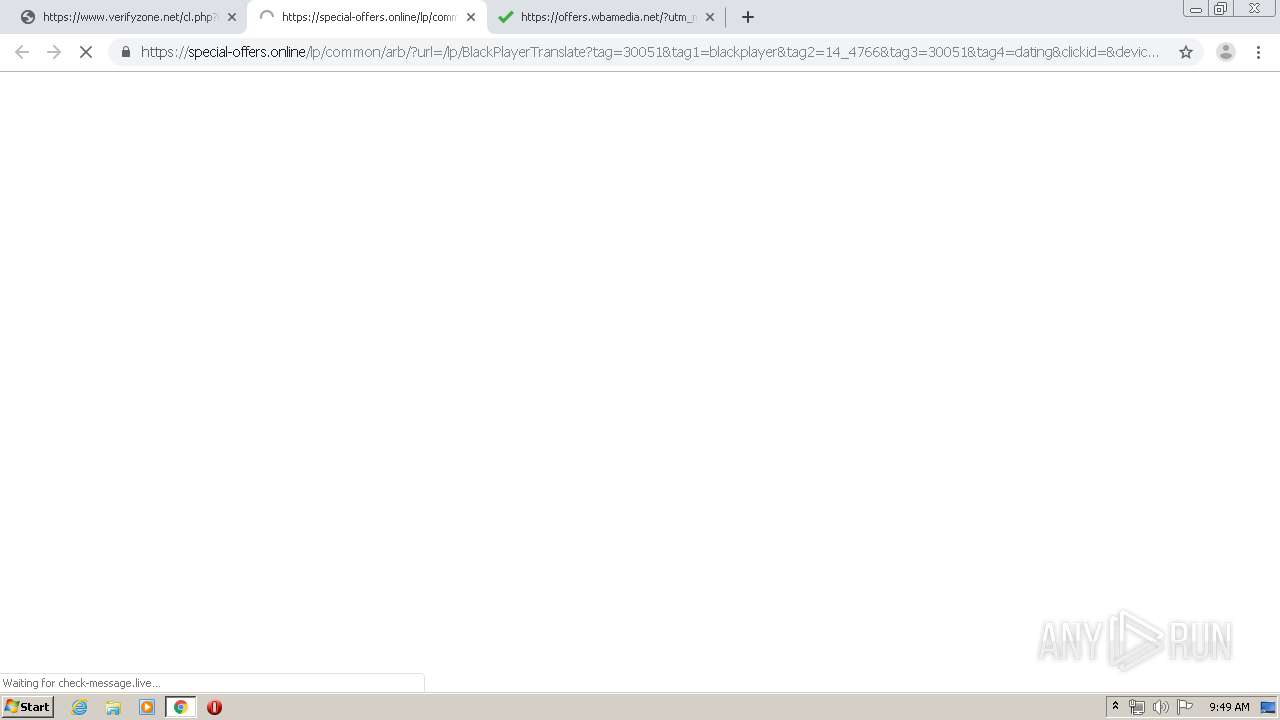
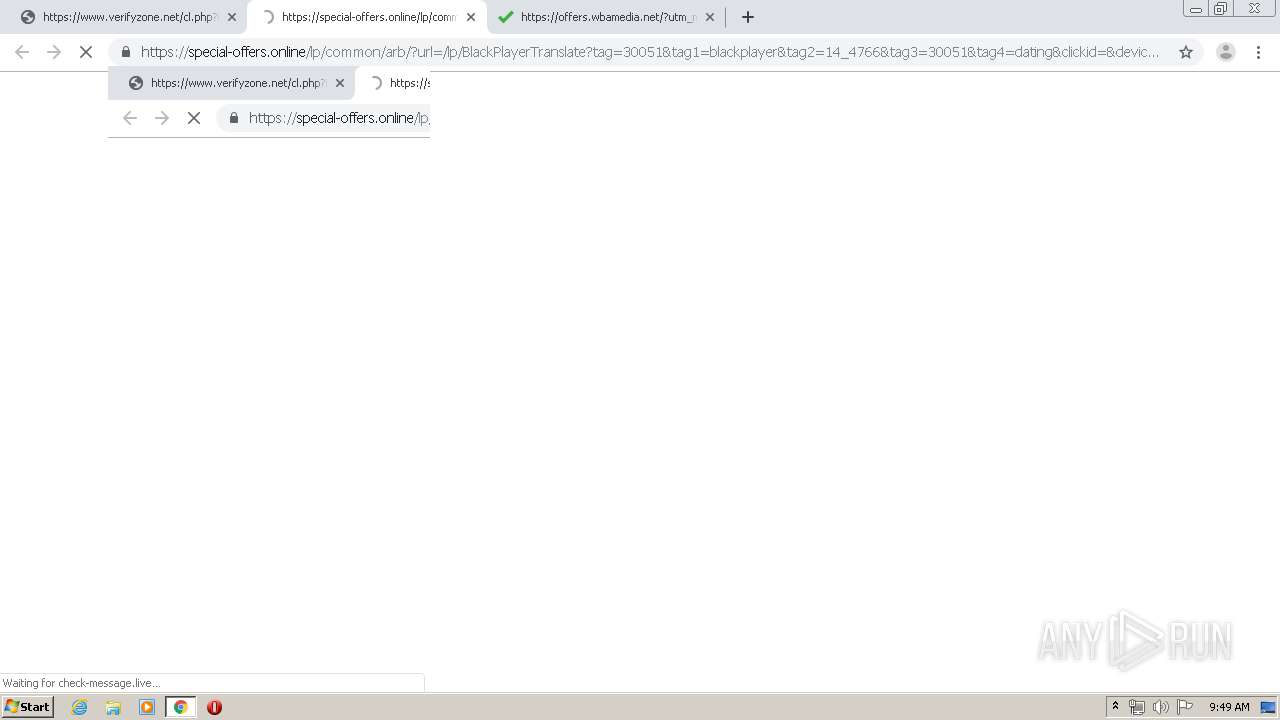
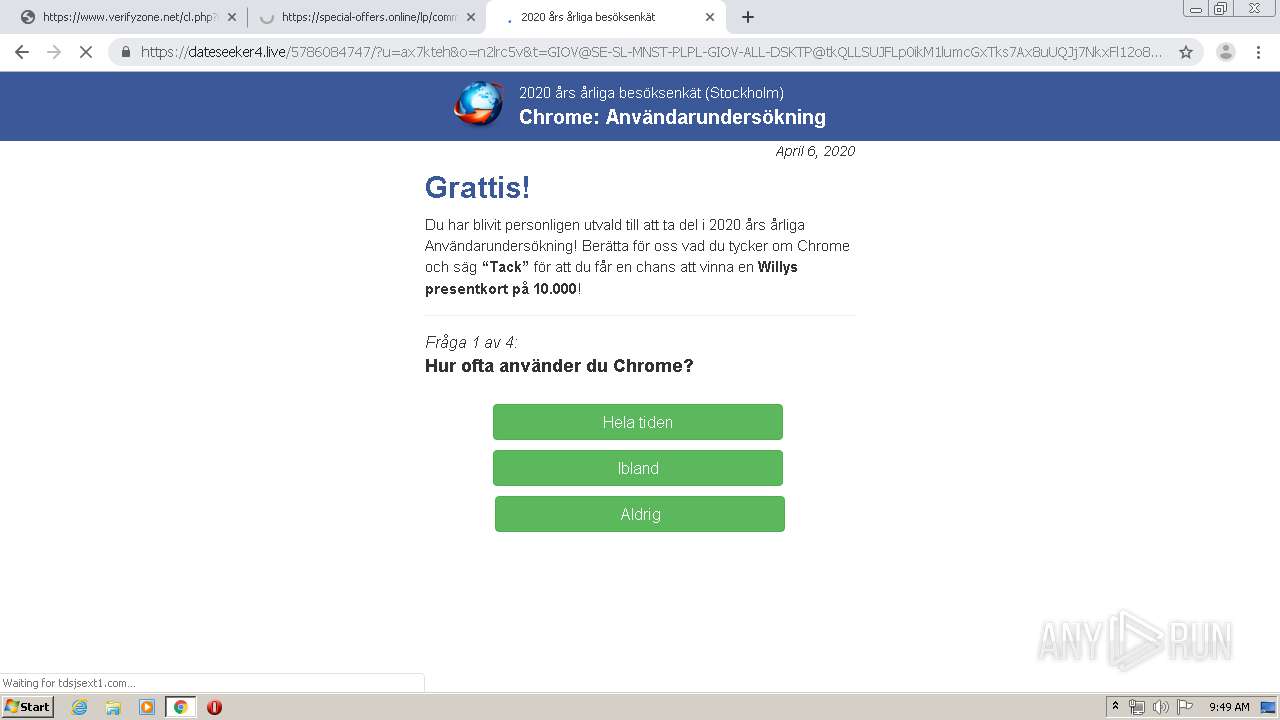
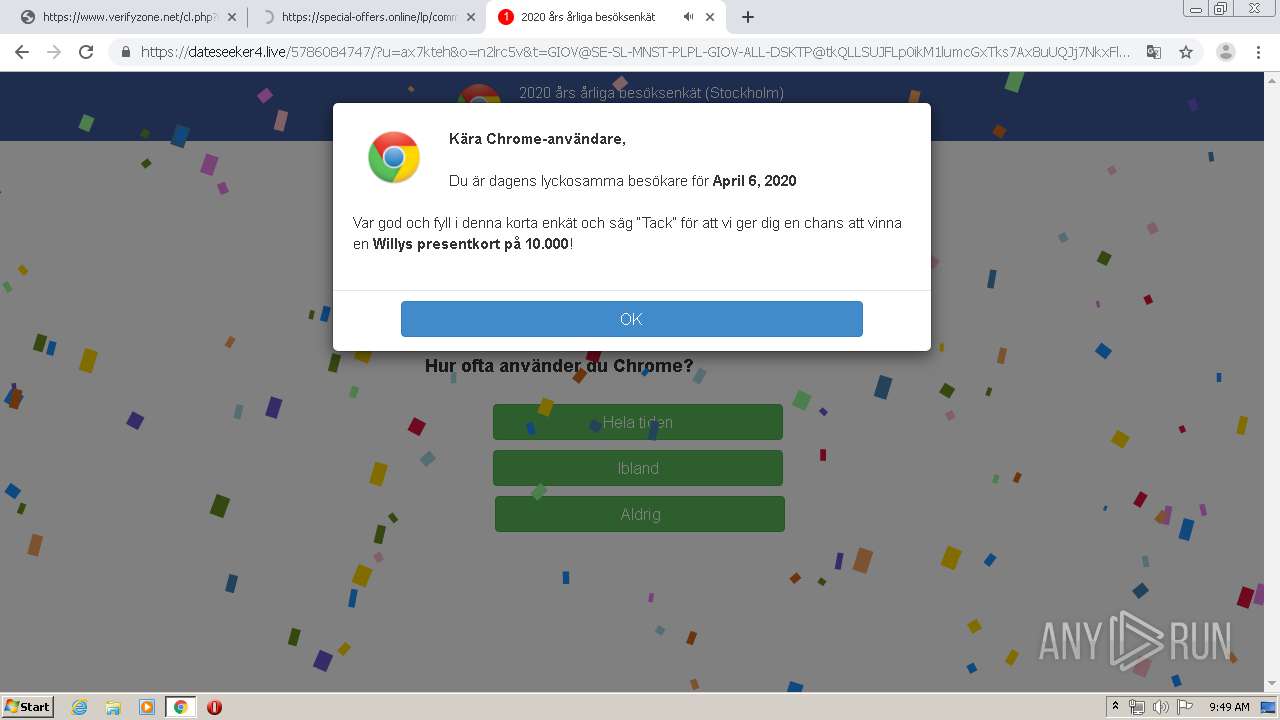
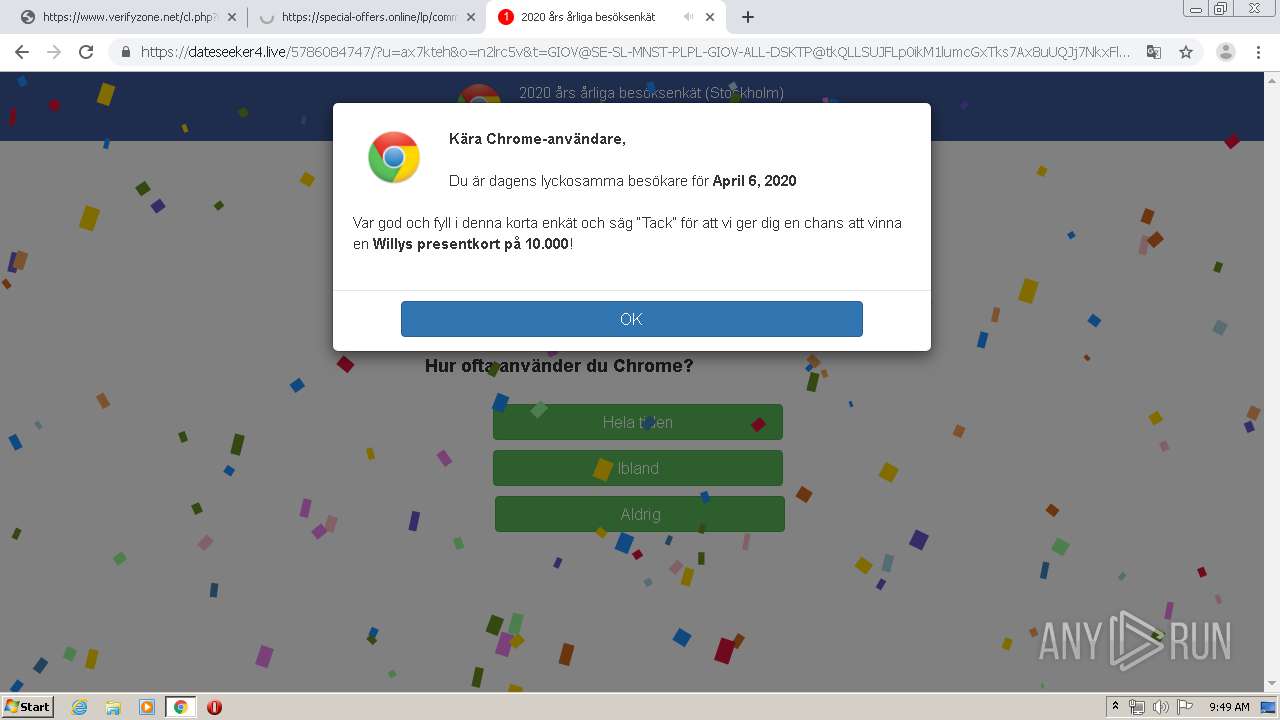
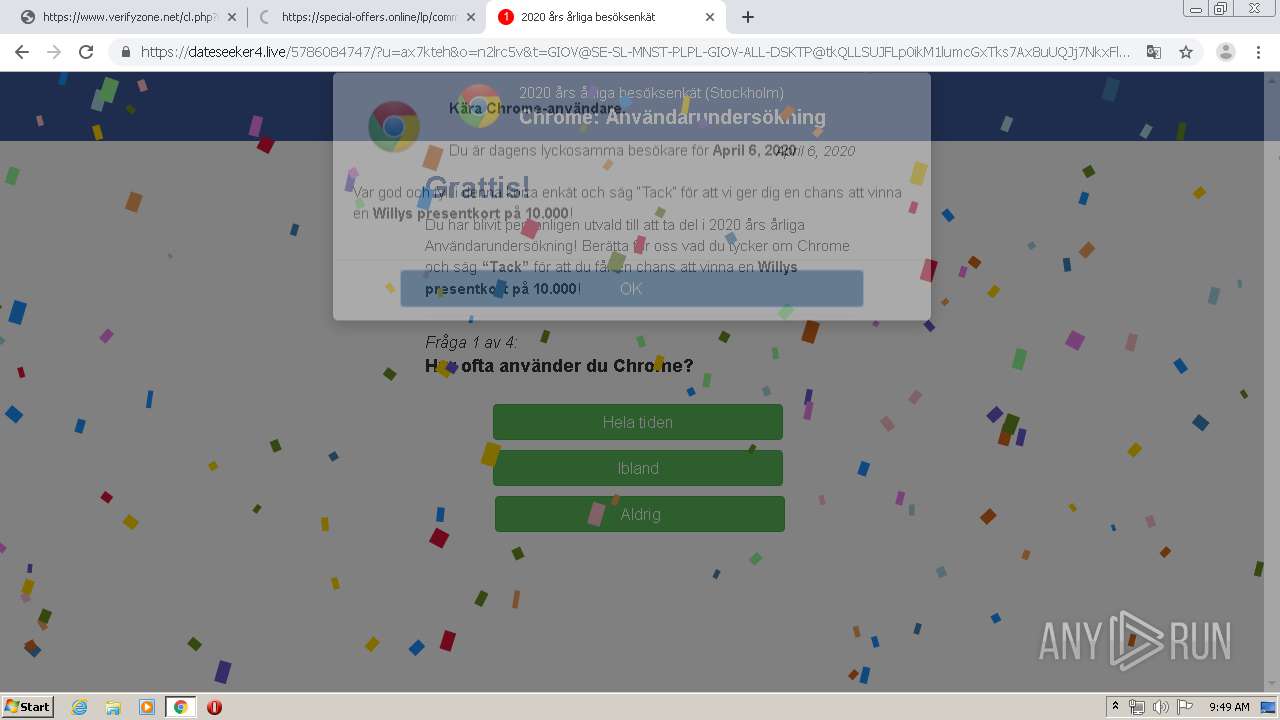
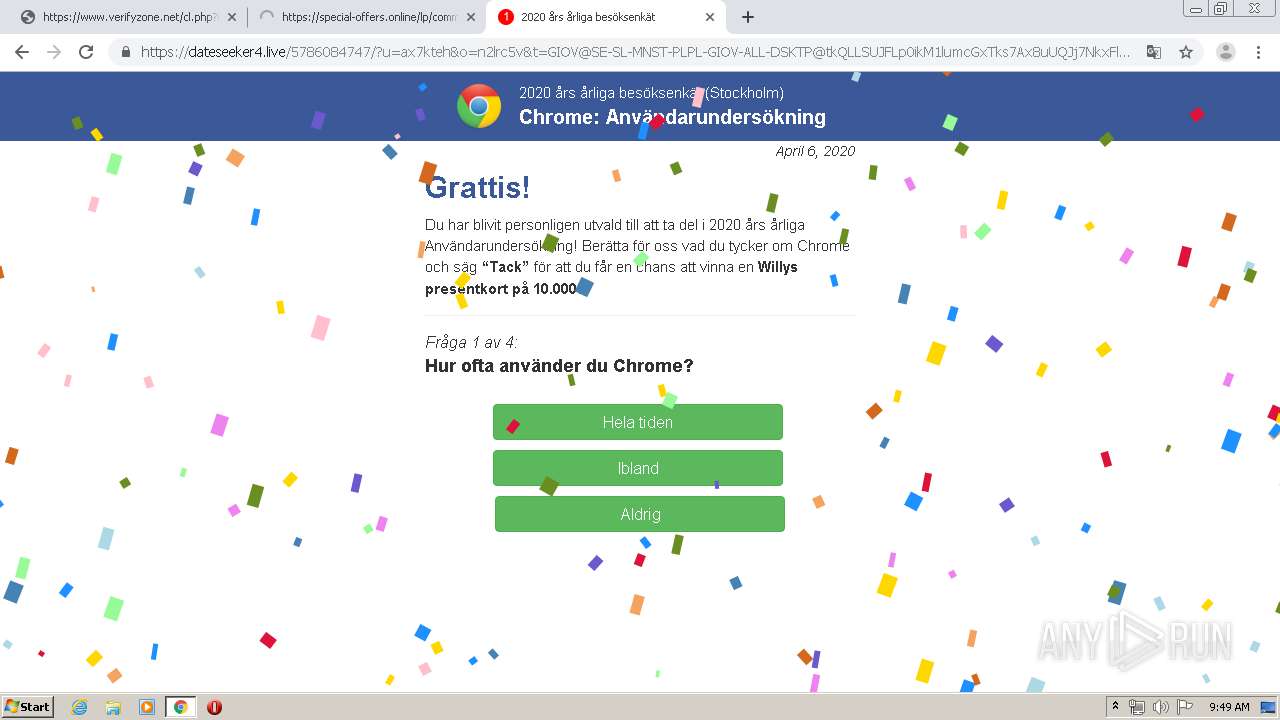
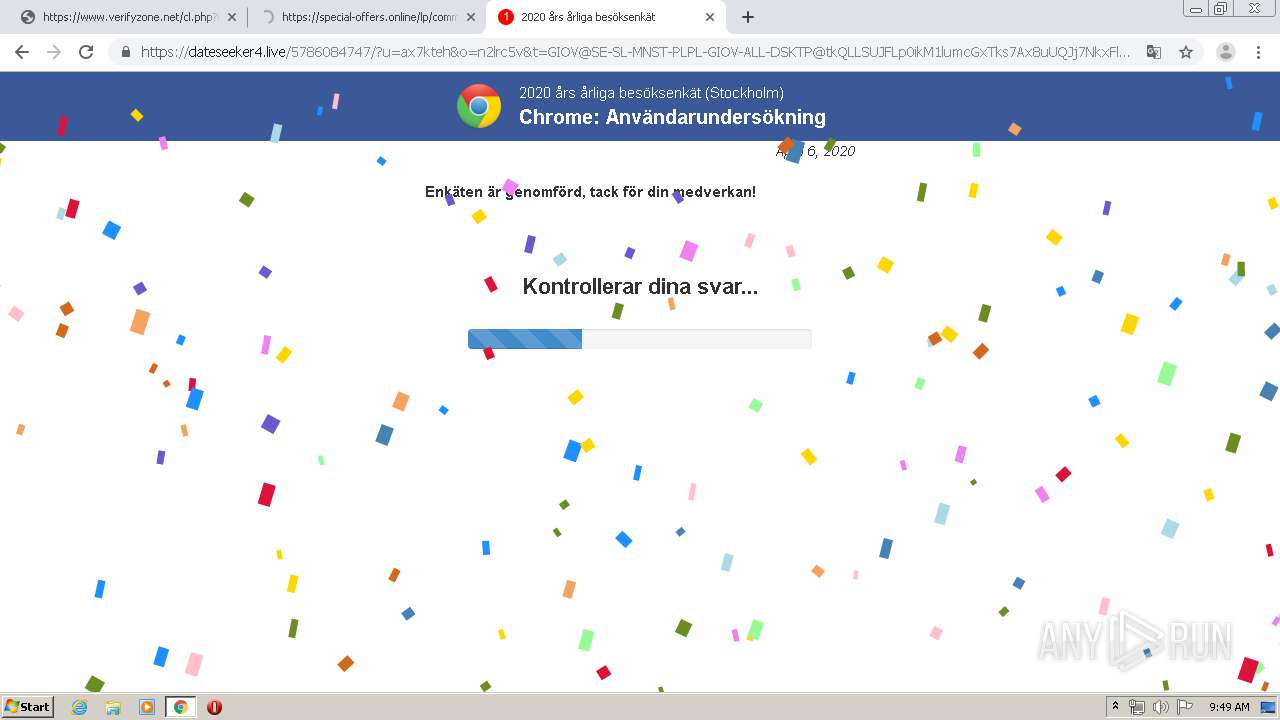
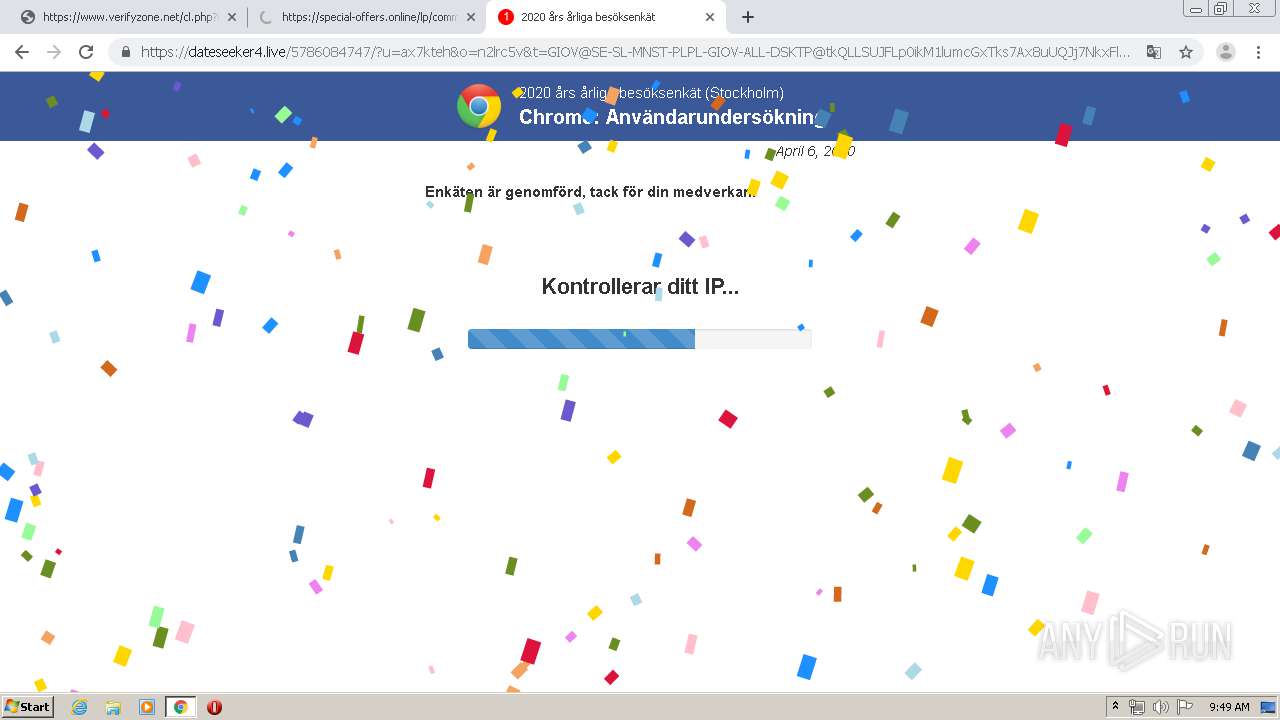
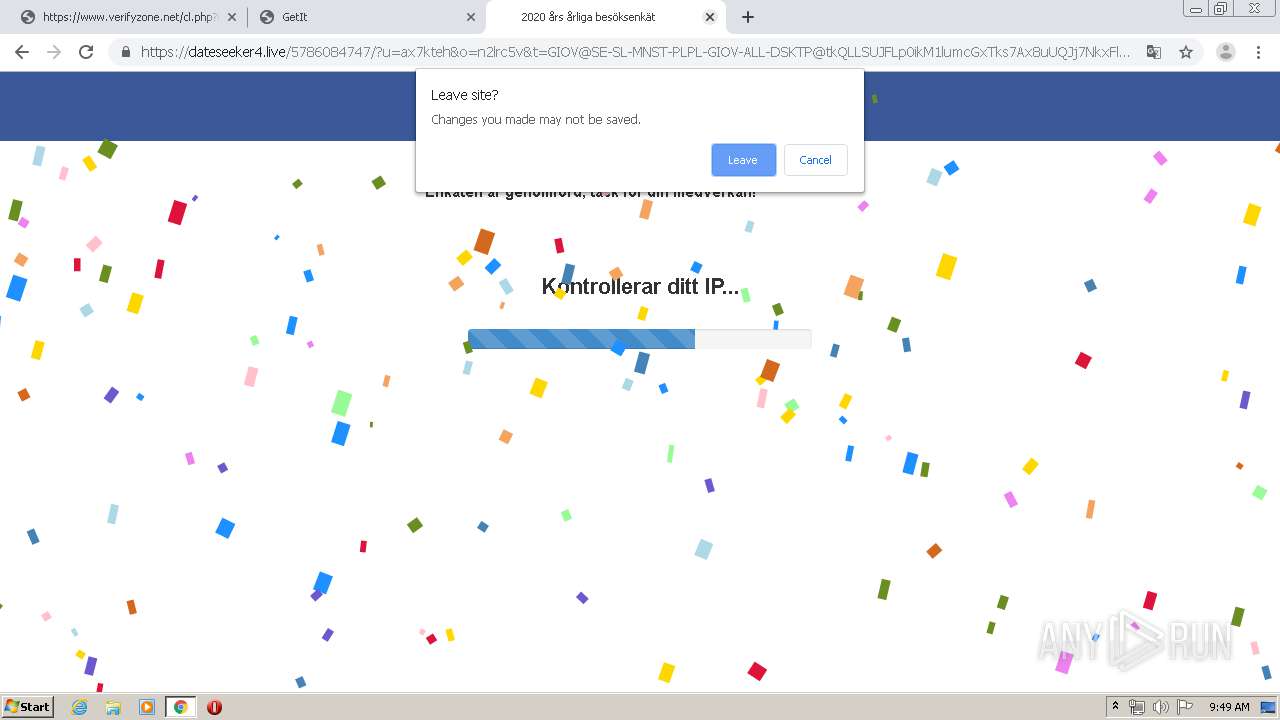
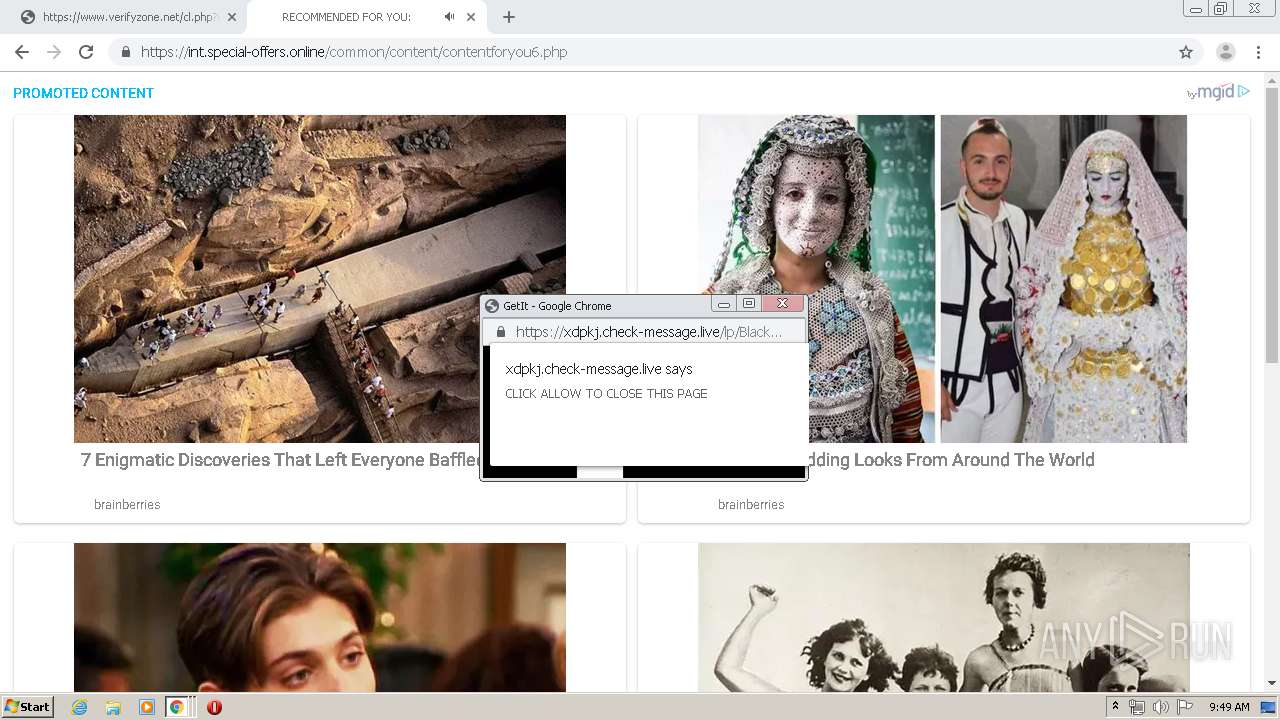
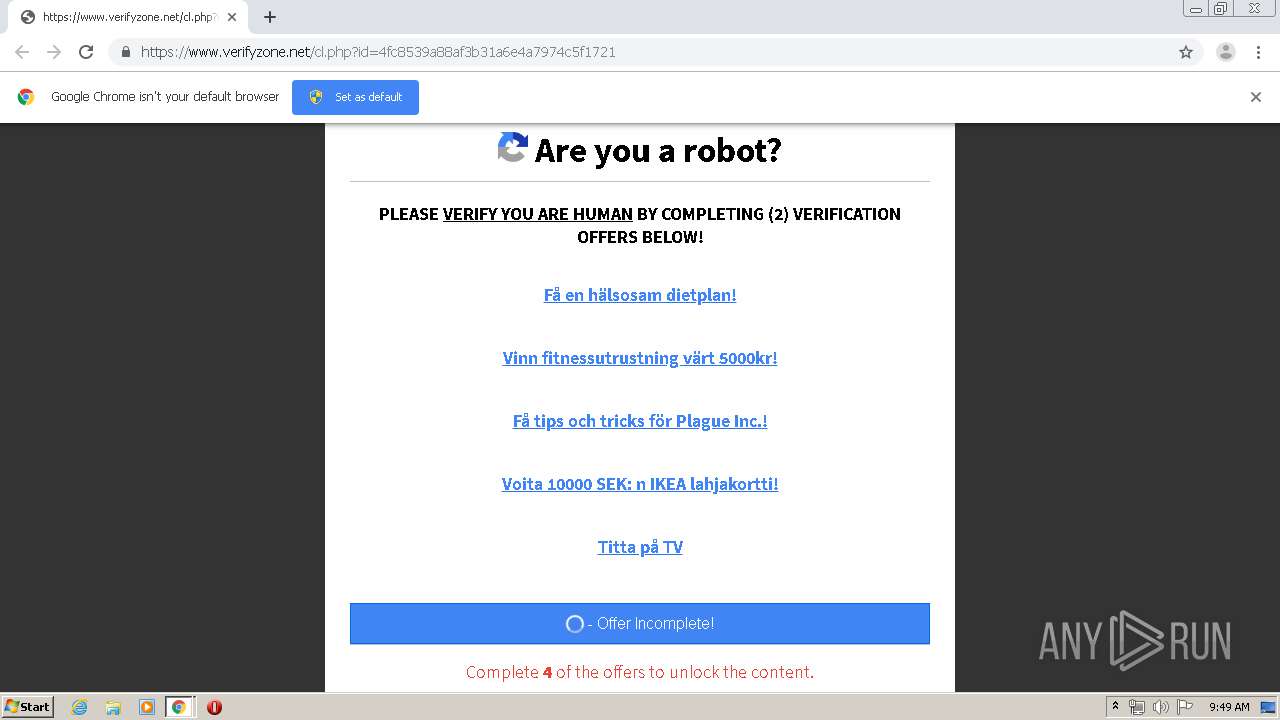
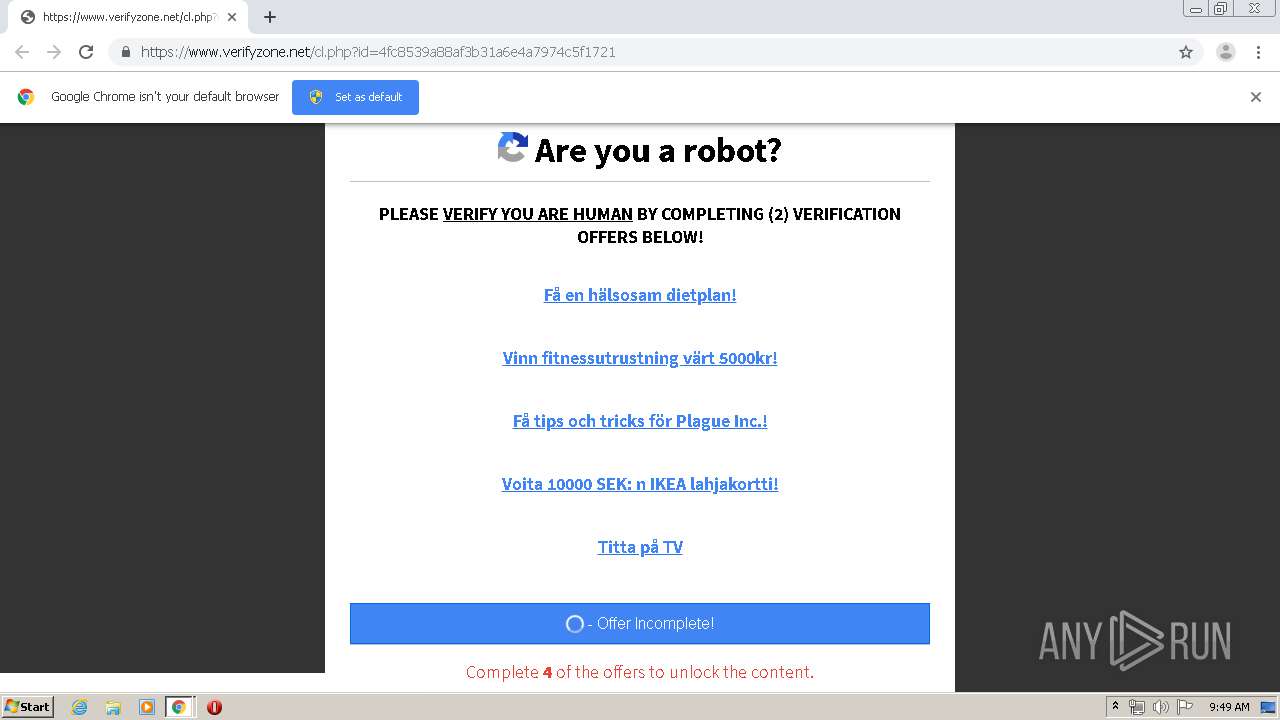
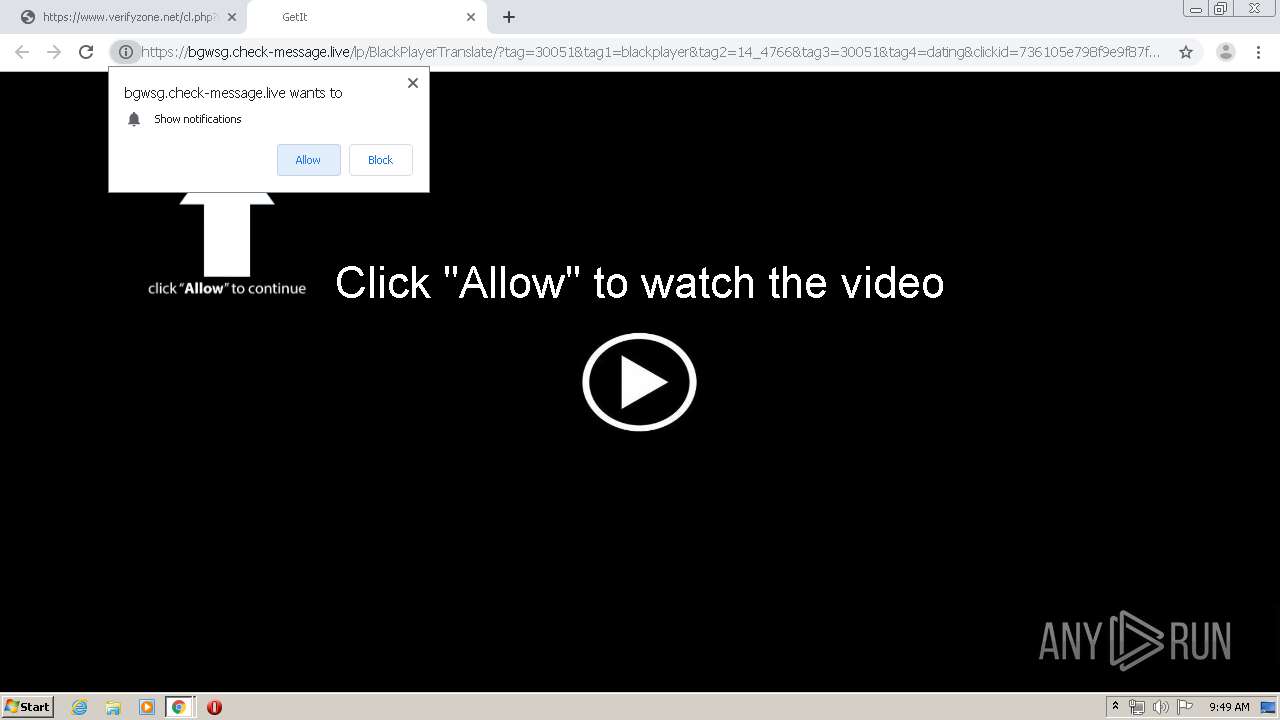
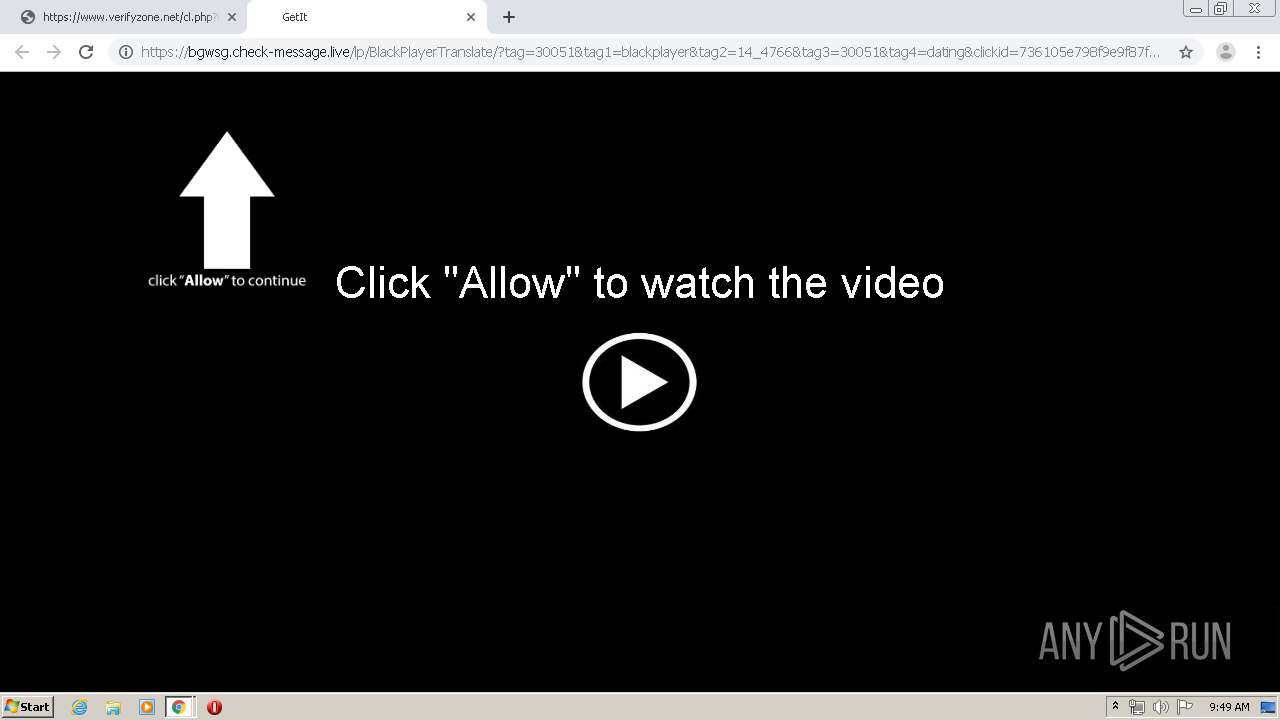
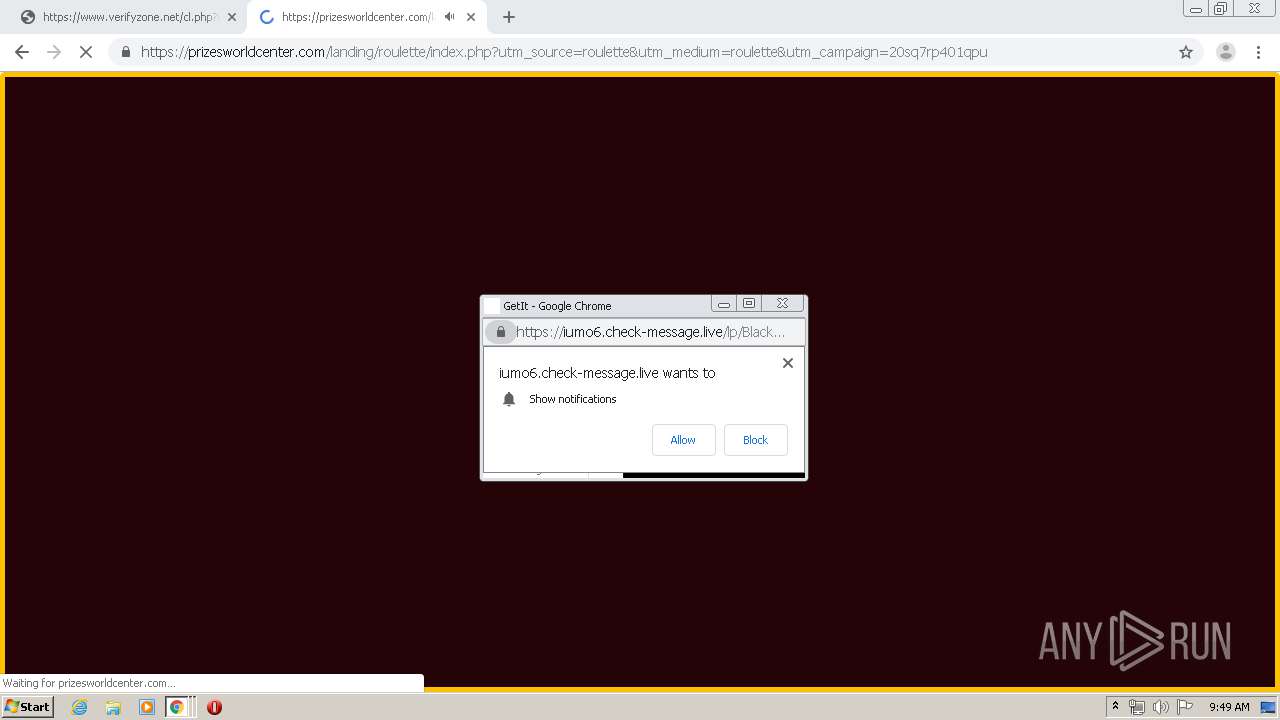
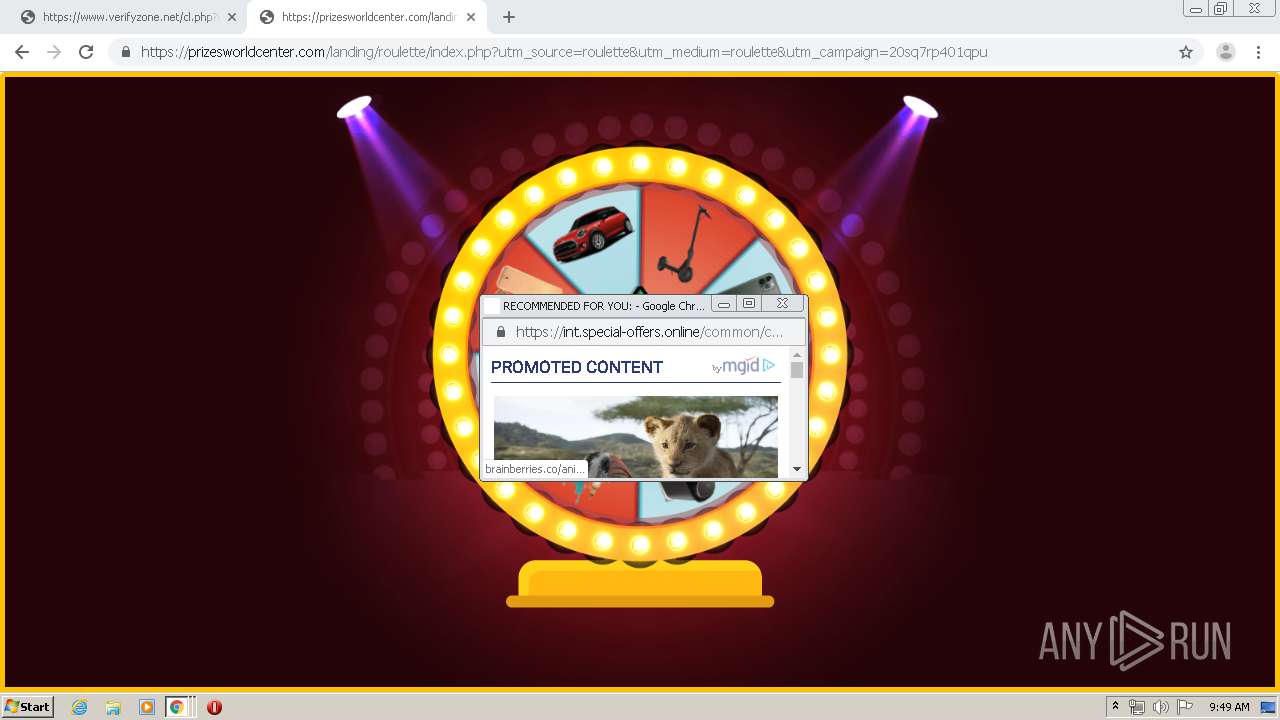
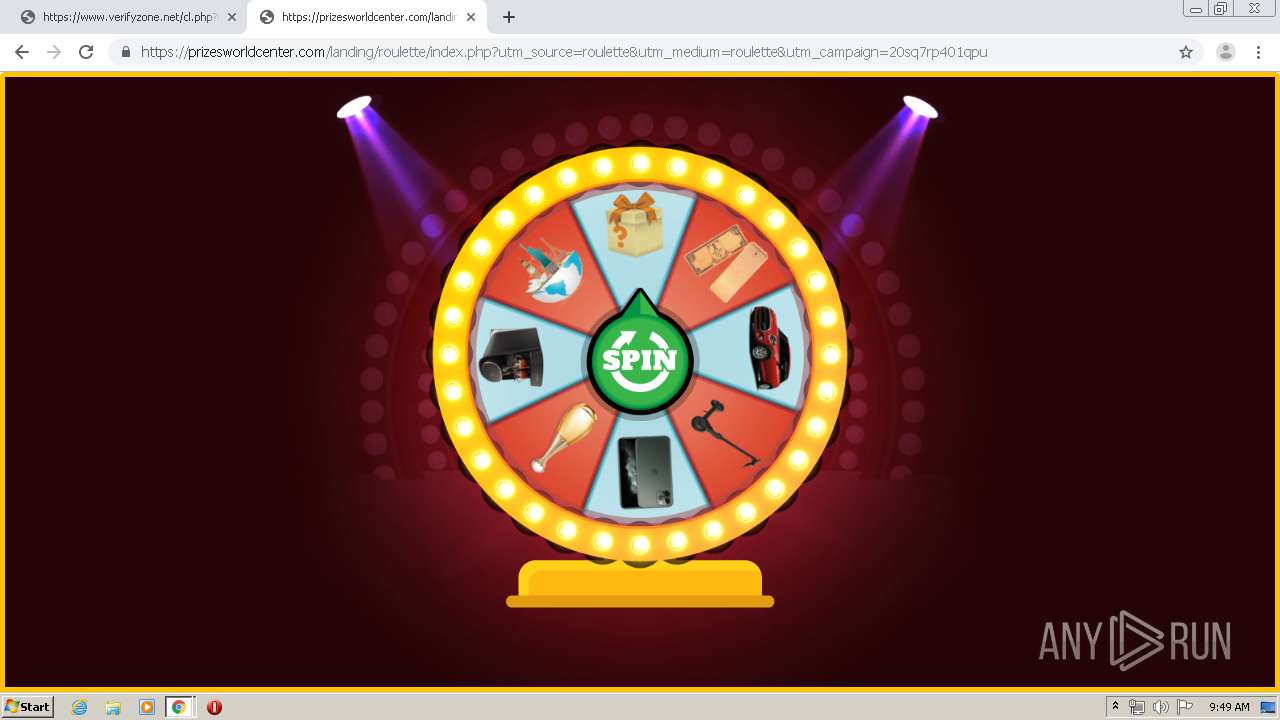
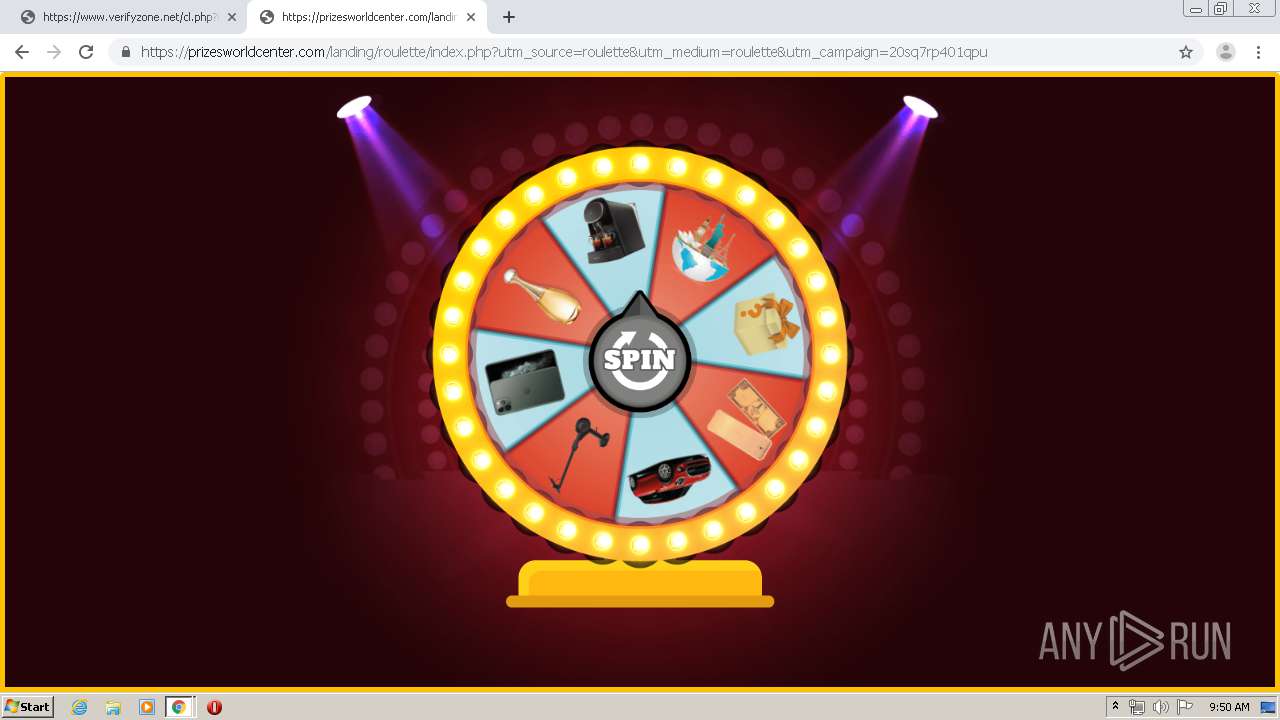
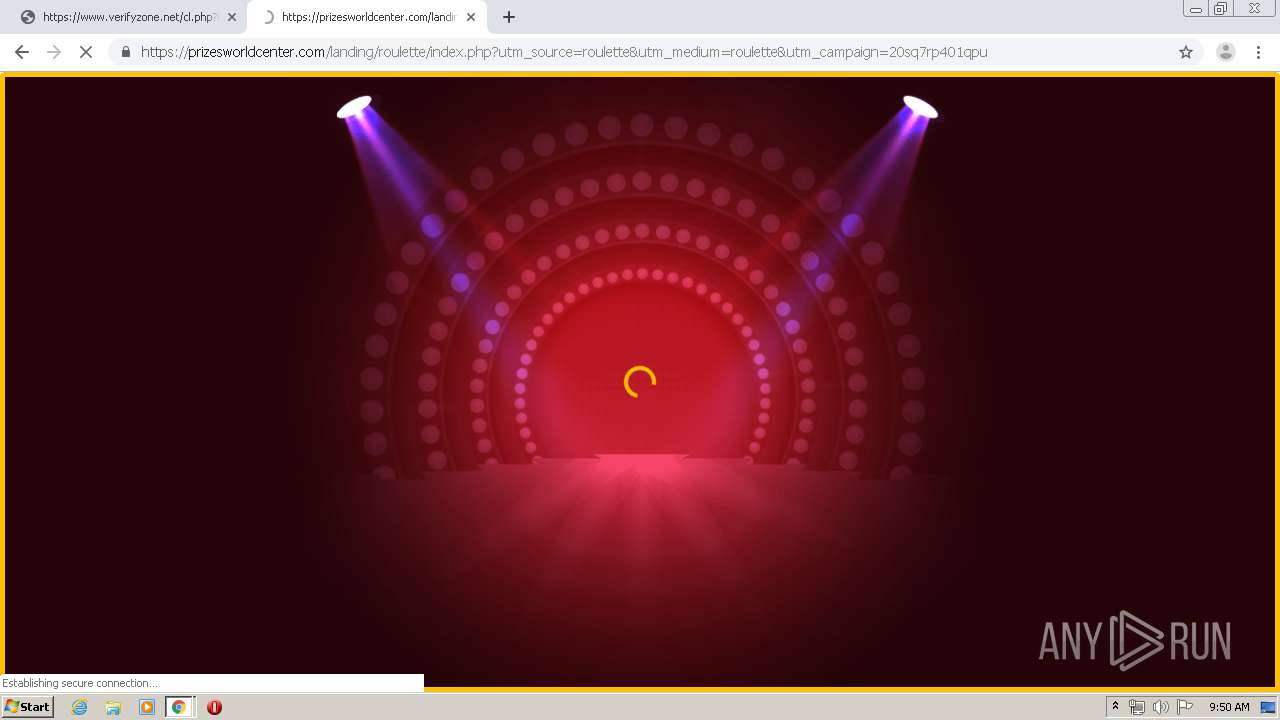
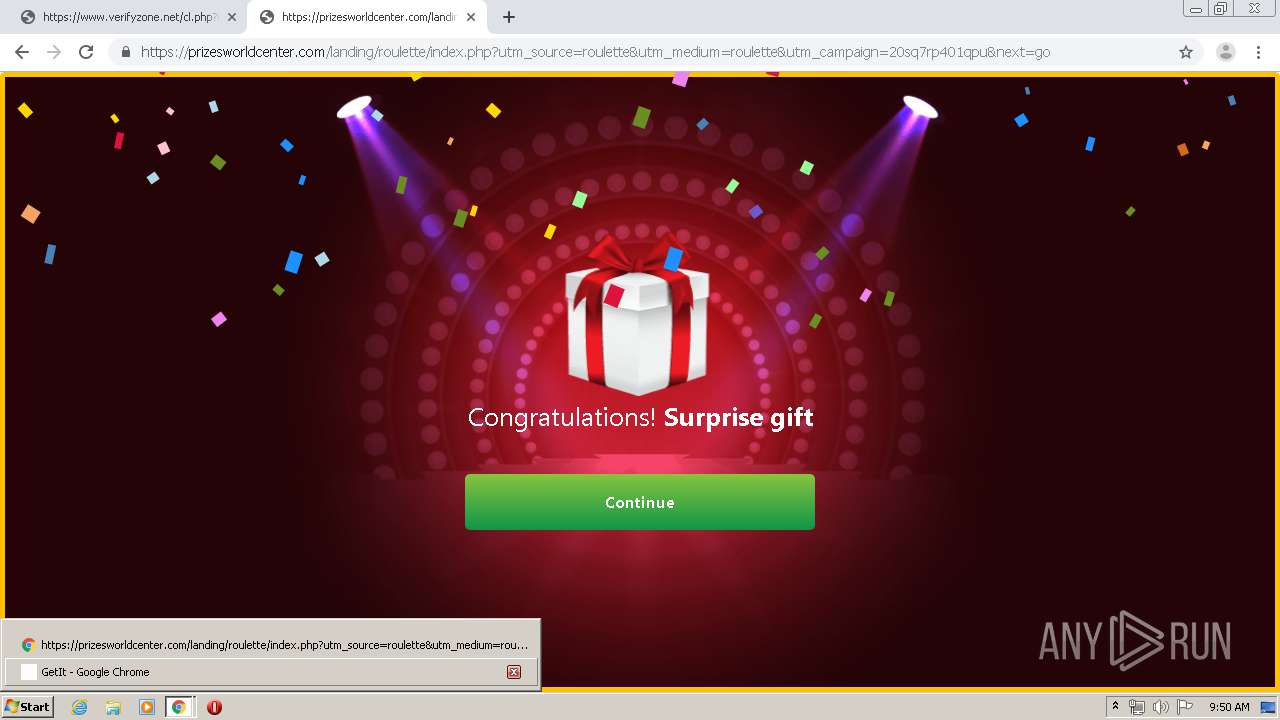
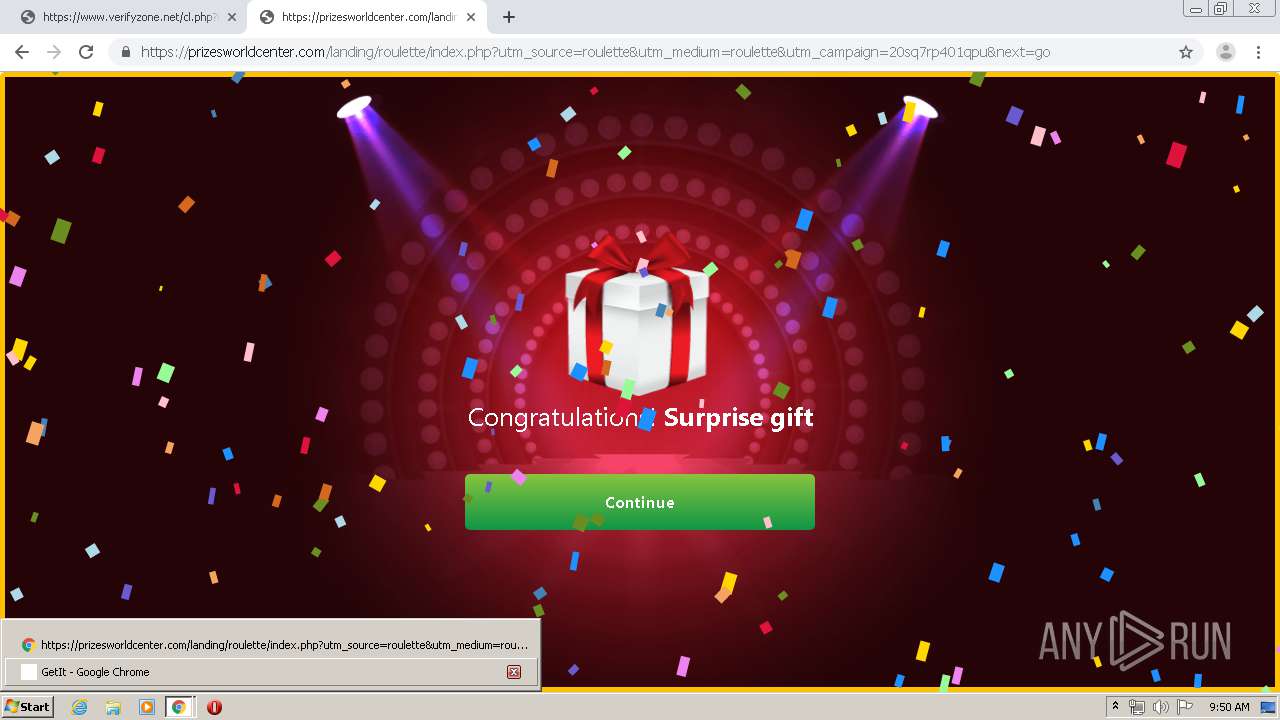
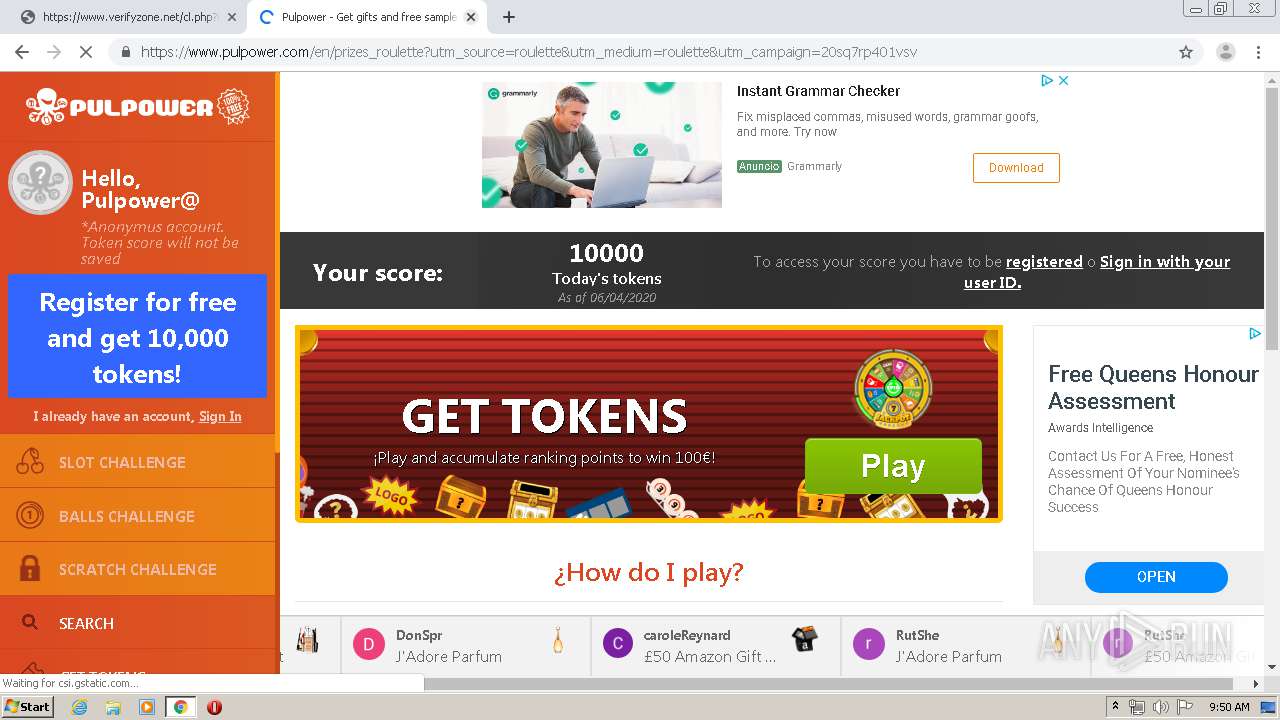
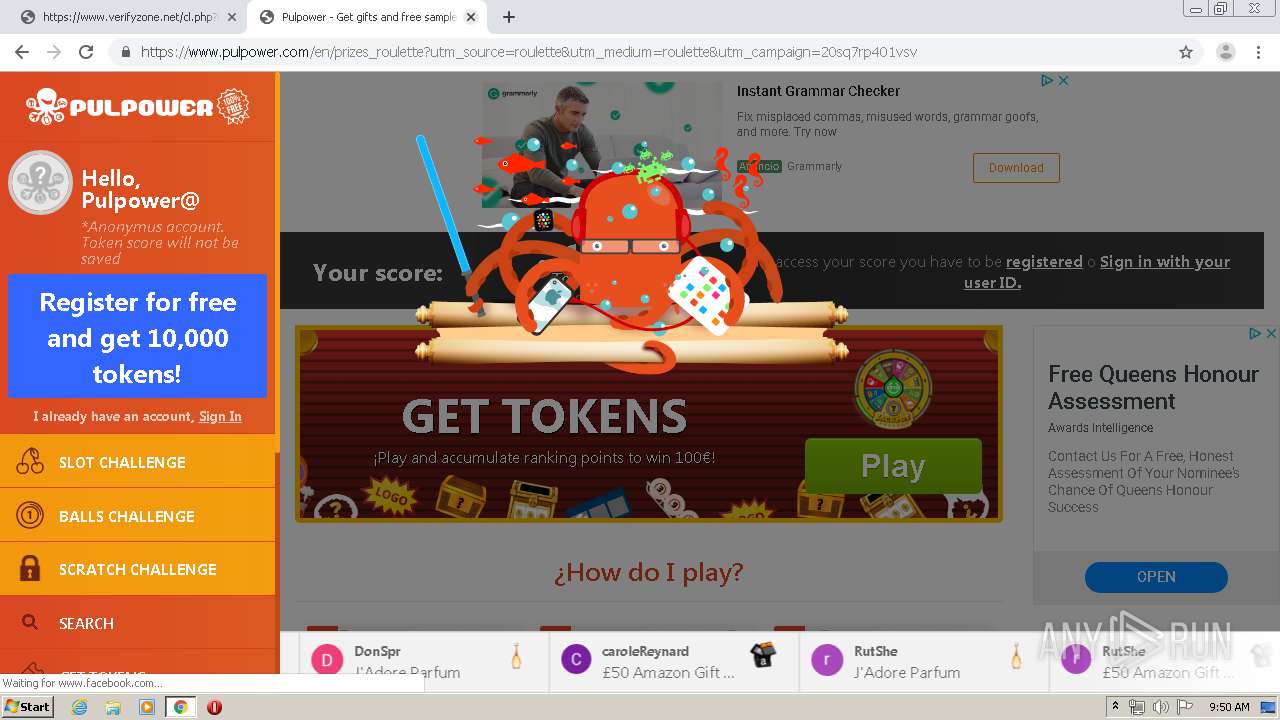
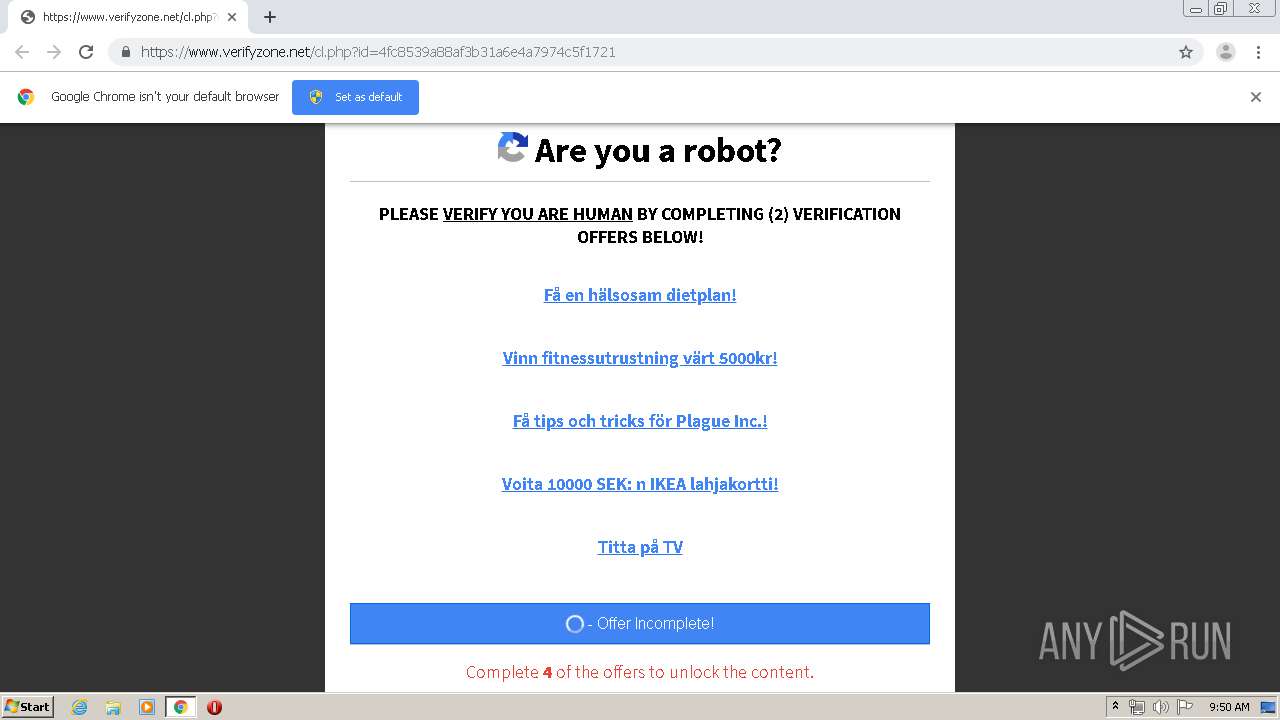
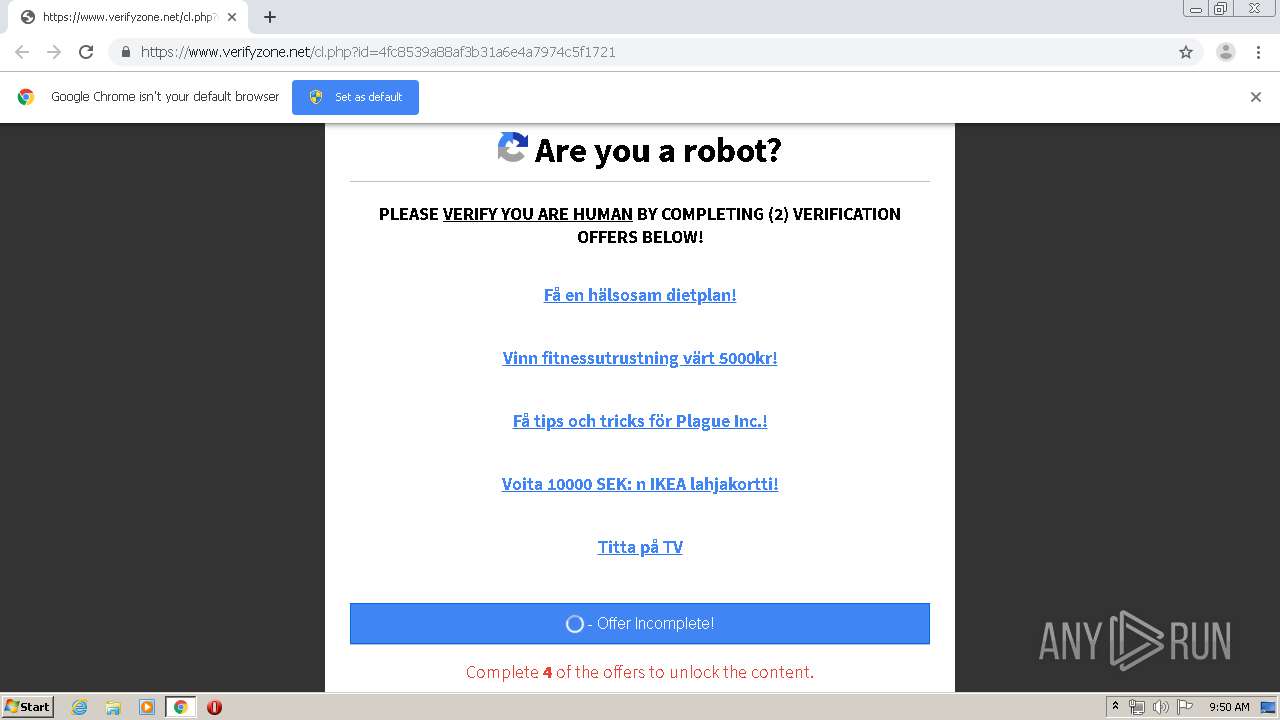
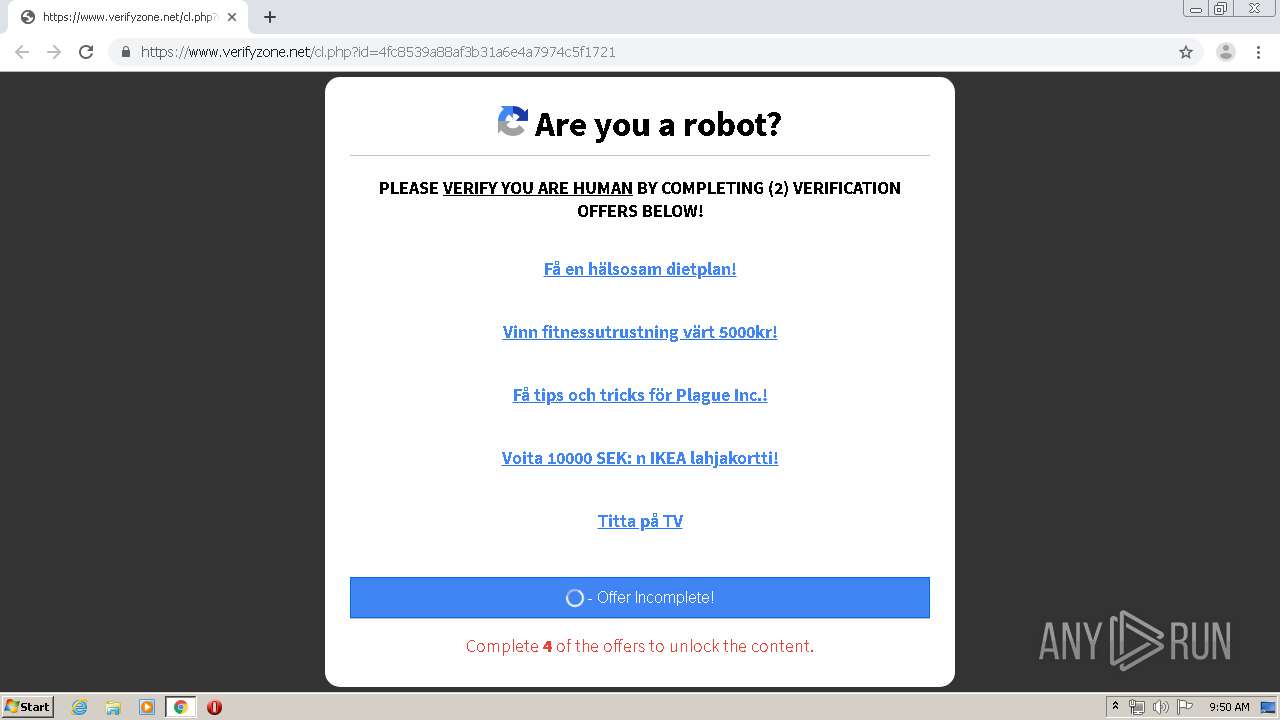
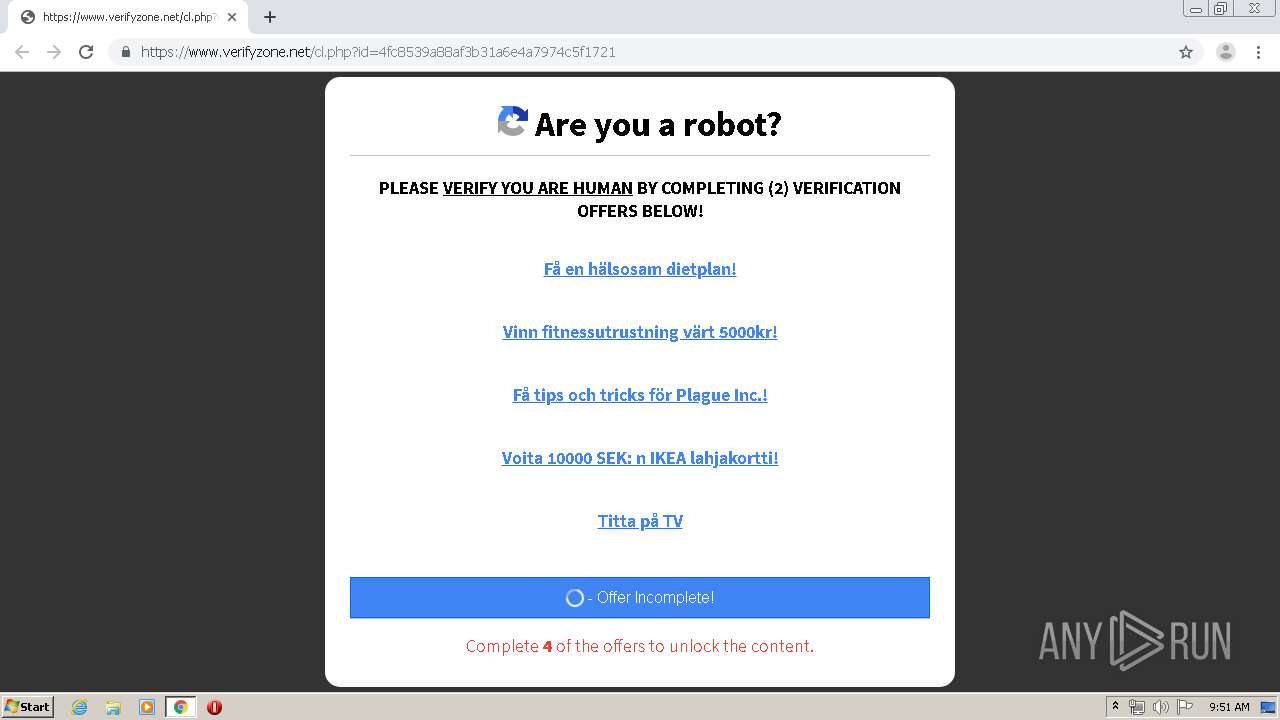
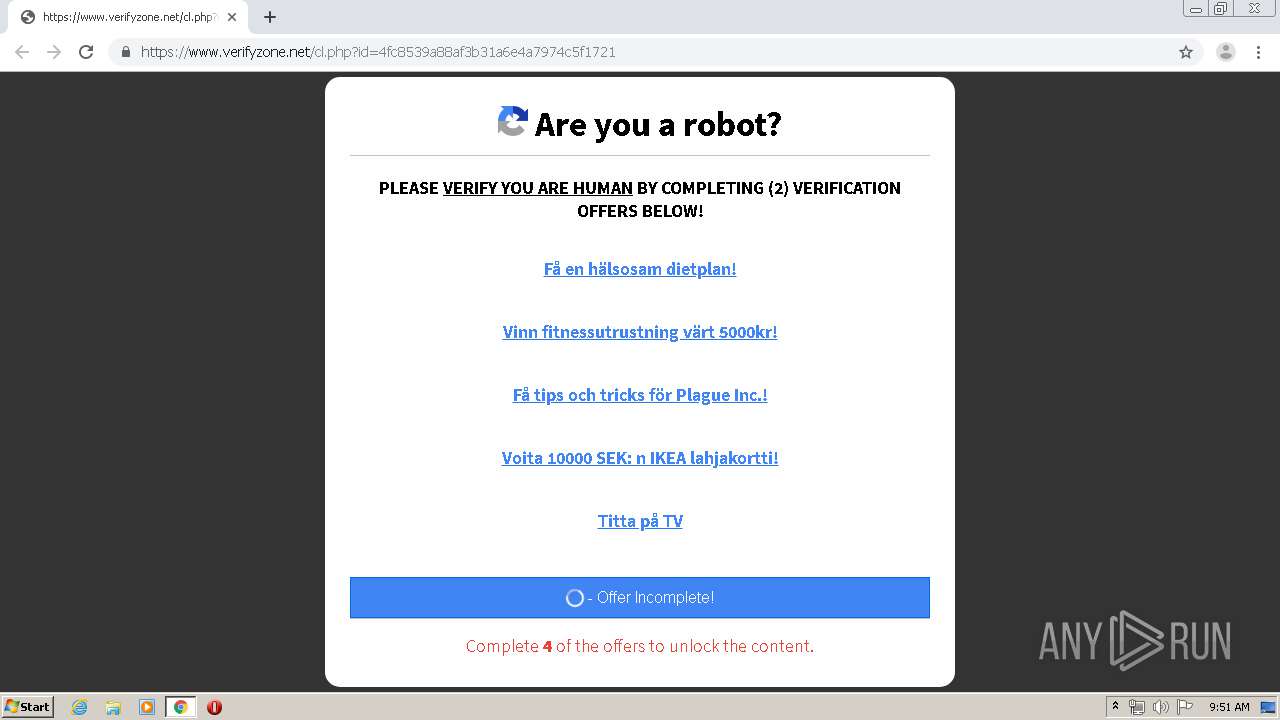
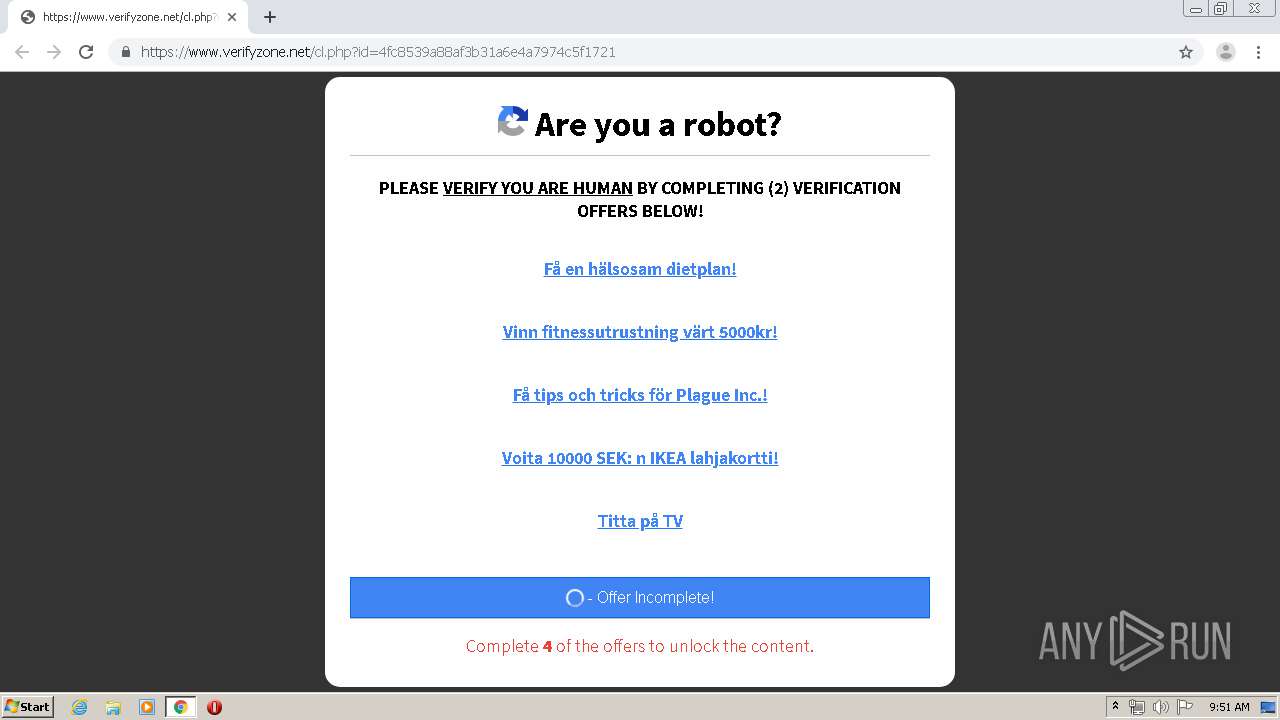
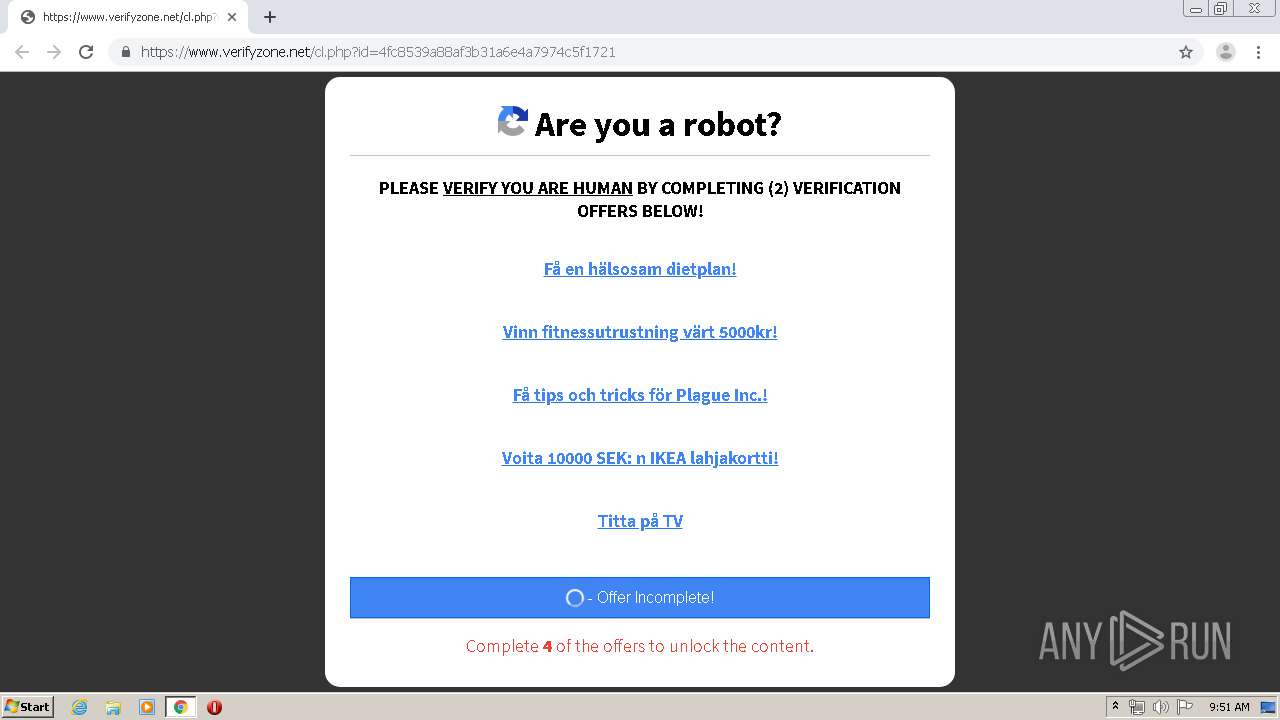
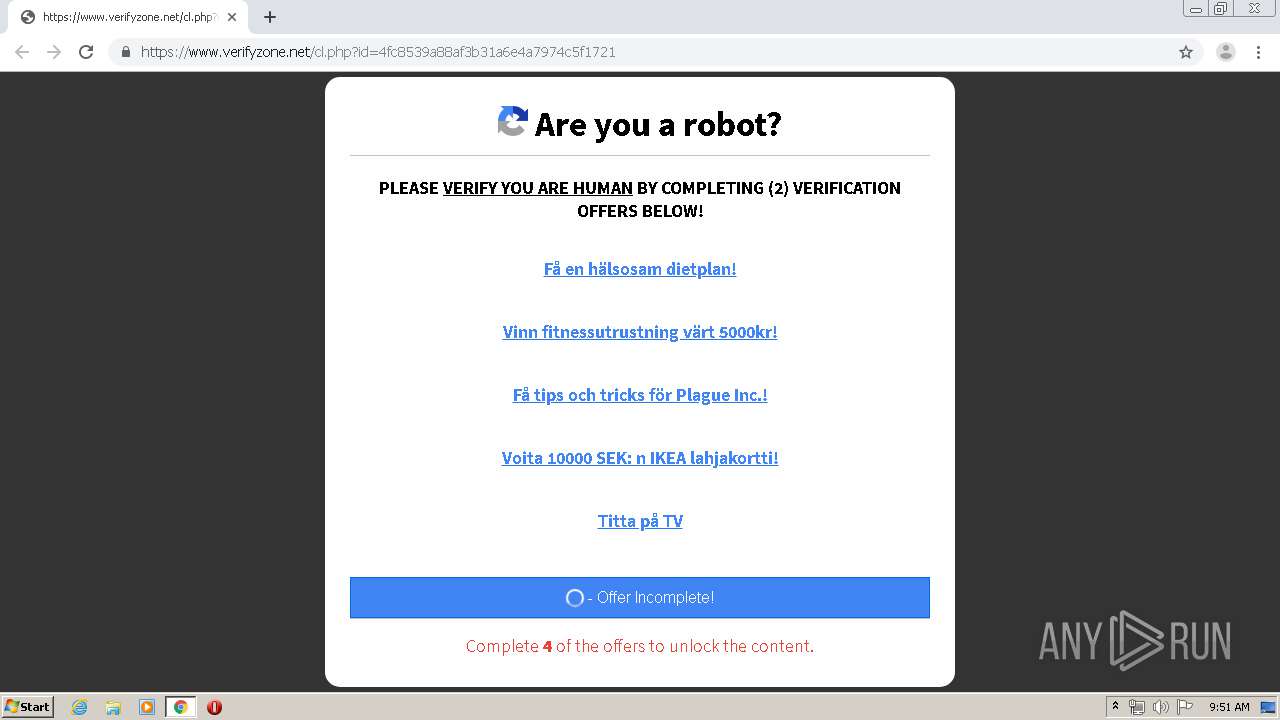
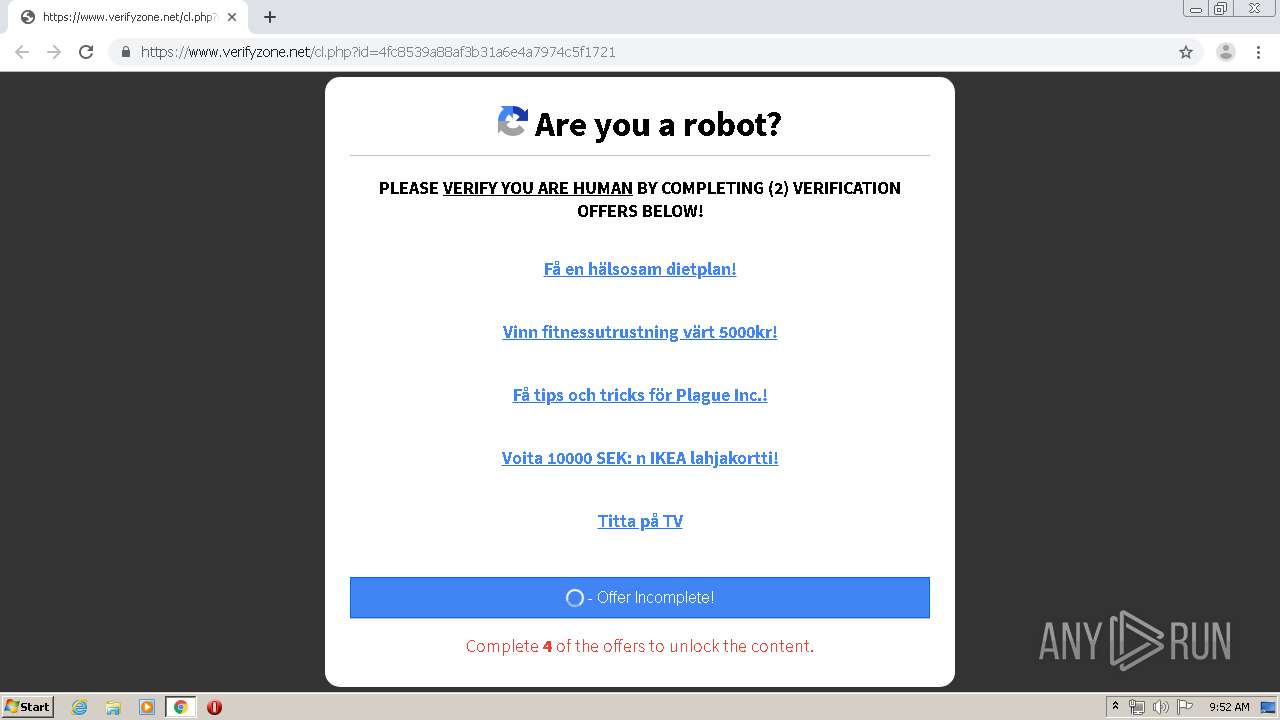
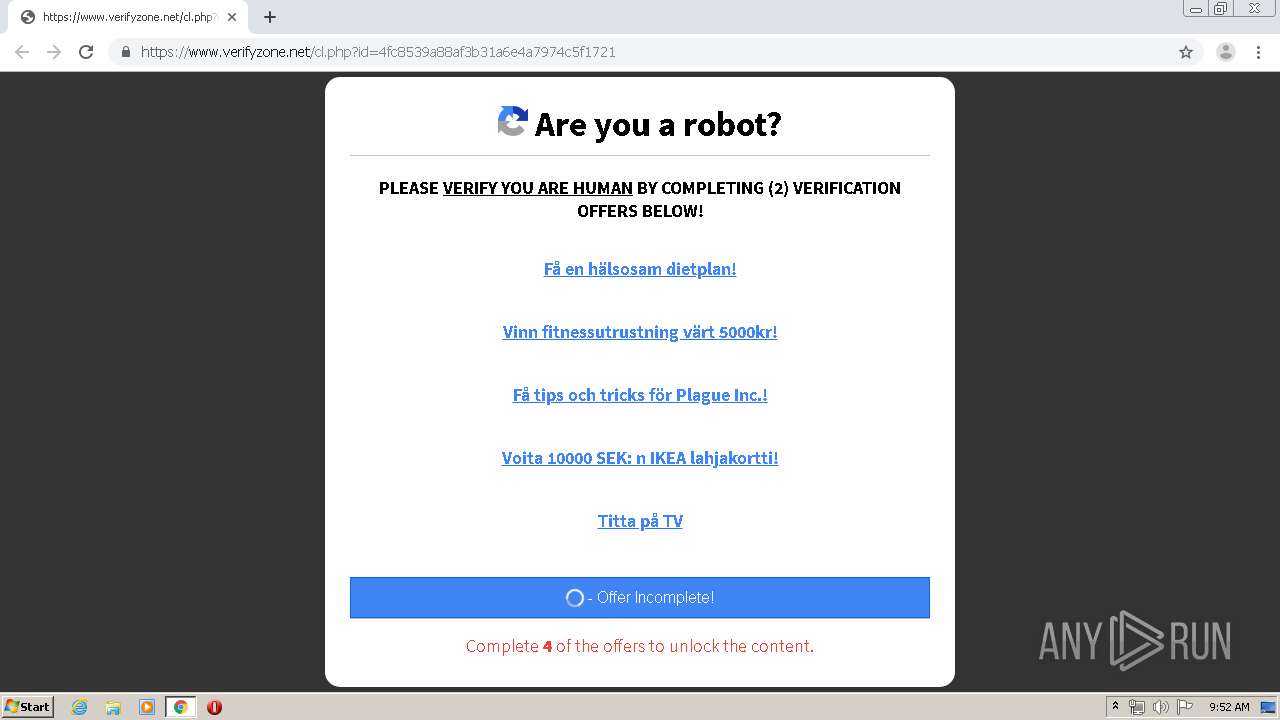
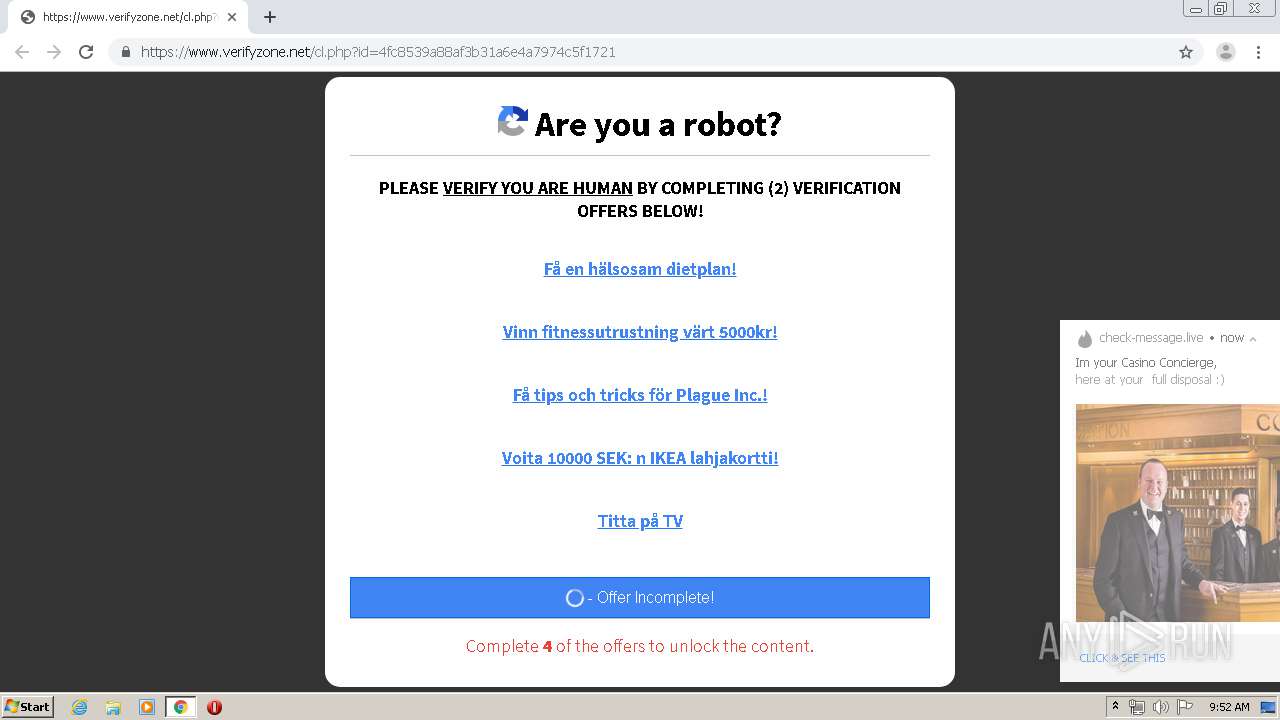
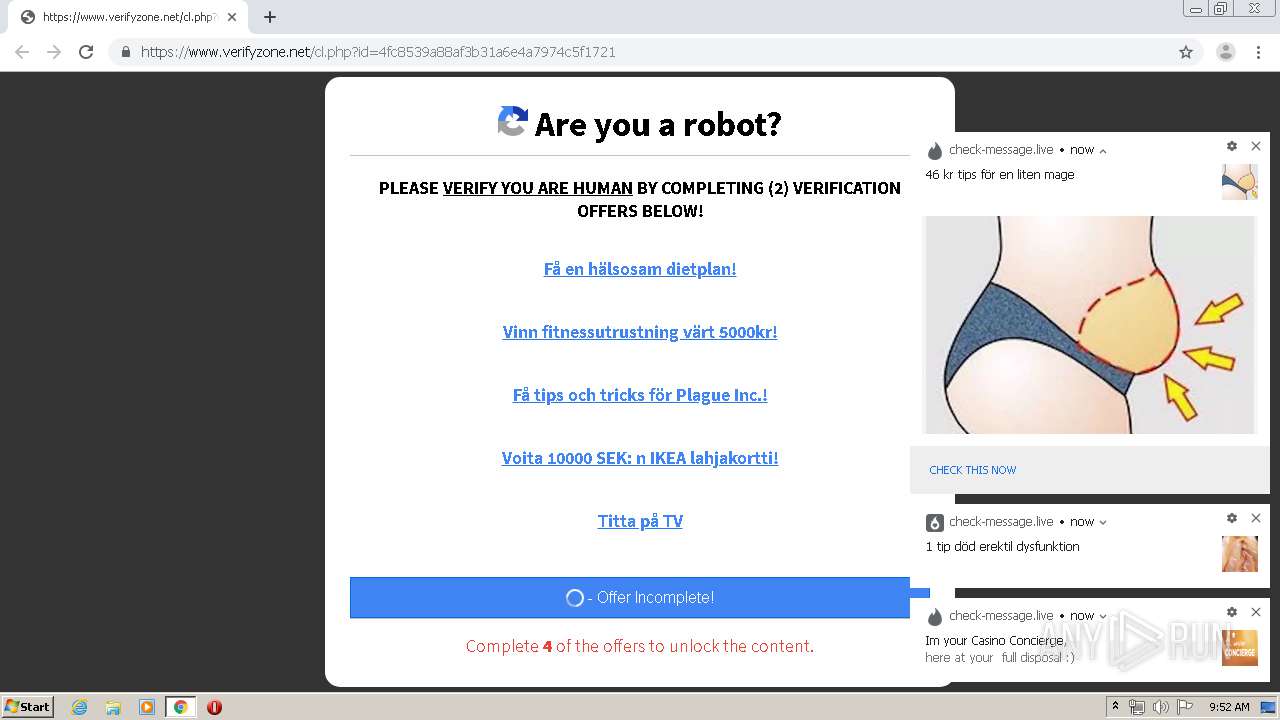
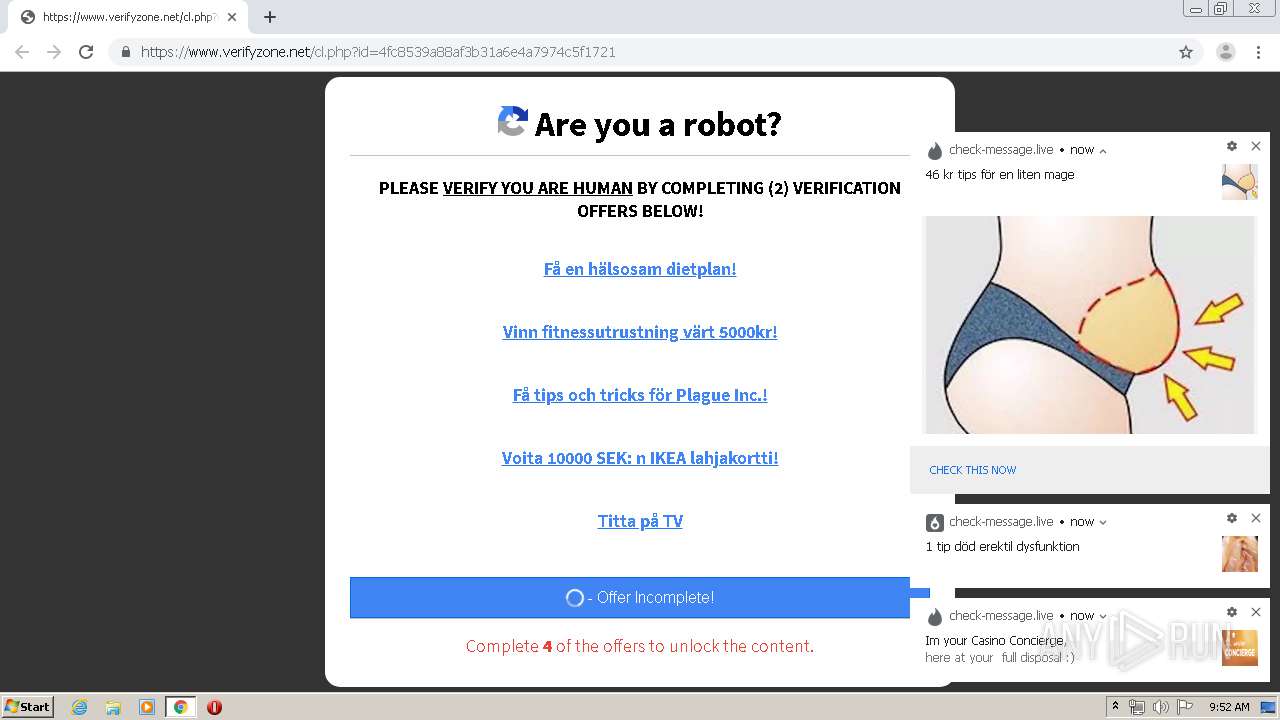
| URL: | https://www.verifyzone.net/cl.php?id=4fc8539a88af3b31a6e4a7974c5f1721 |
| Full analysis: | https://app.any.run/tasks/b57888b8-6935-4788-b668-1a8e5cde5a1c |
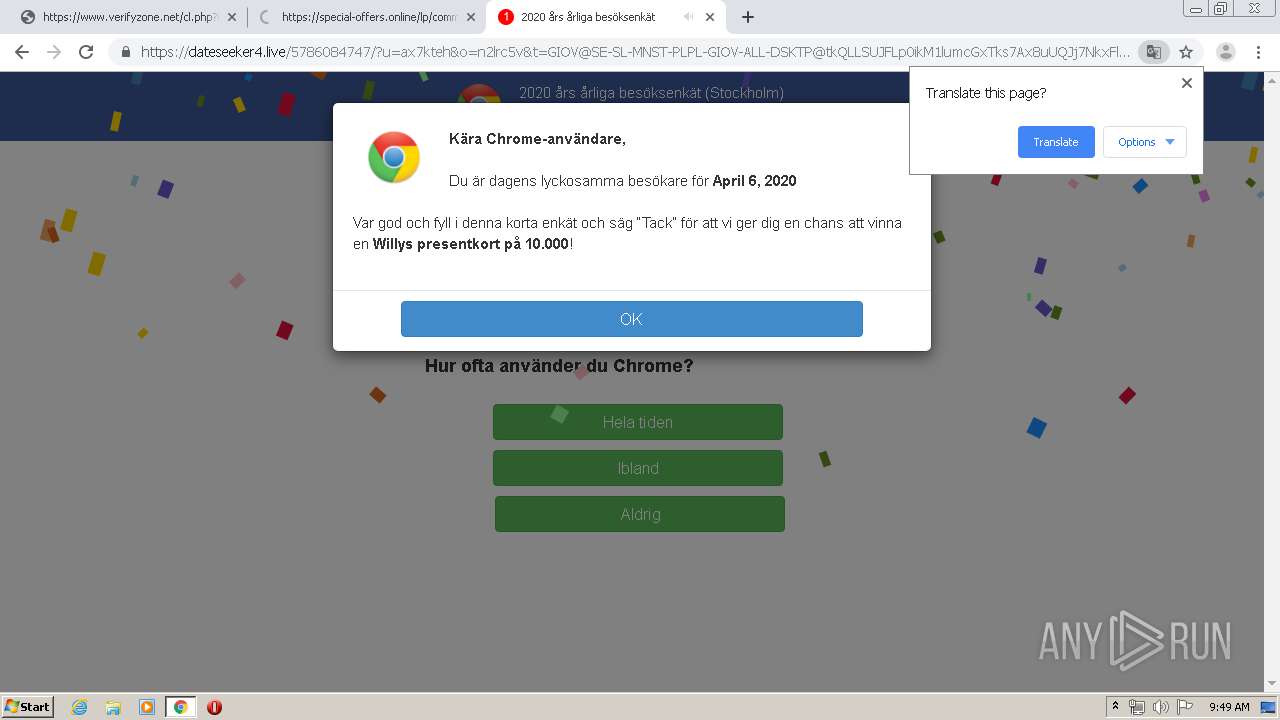
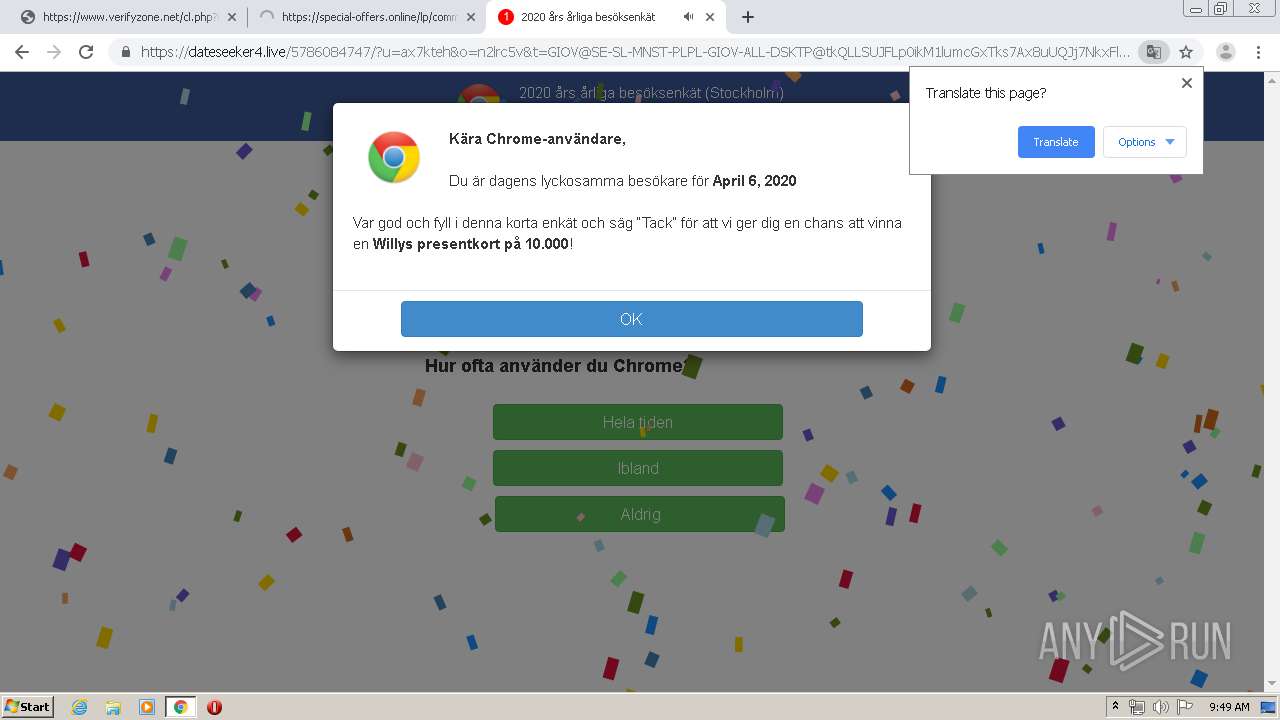
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2020, 08:47:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9220B35AF69188EFF78A67B77565C0B0 |
| SHA1: | 49923B1E1720CAA6E3155C9C252C658289E0E1D2 |
| SHA256: | B7180C8C74D5B4E7BCCC926E860697F4F12154128AFC601F9339E8CE85B0DE25 |
| SSDEEP: | 3:N8DSLMXMDcfhOLn5eGcEsK2mxtM:2OLMPfhObbWnf |
MALICIOUS
No malicious indicators.SUSPICIOUS
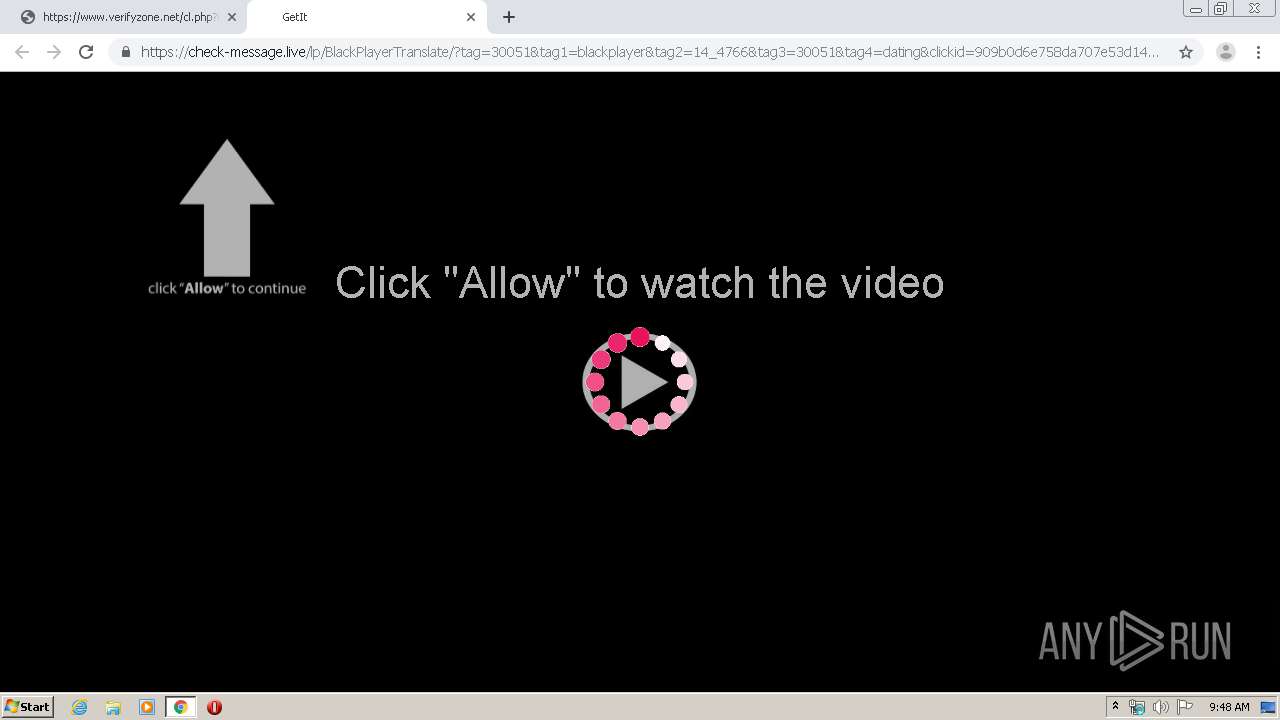
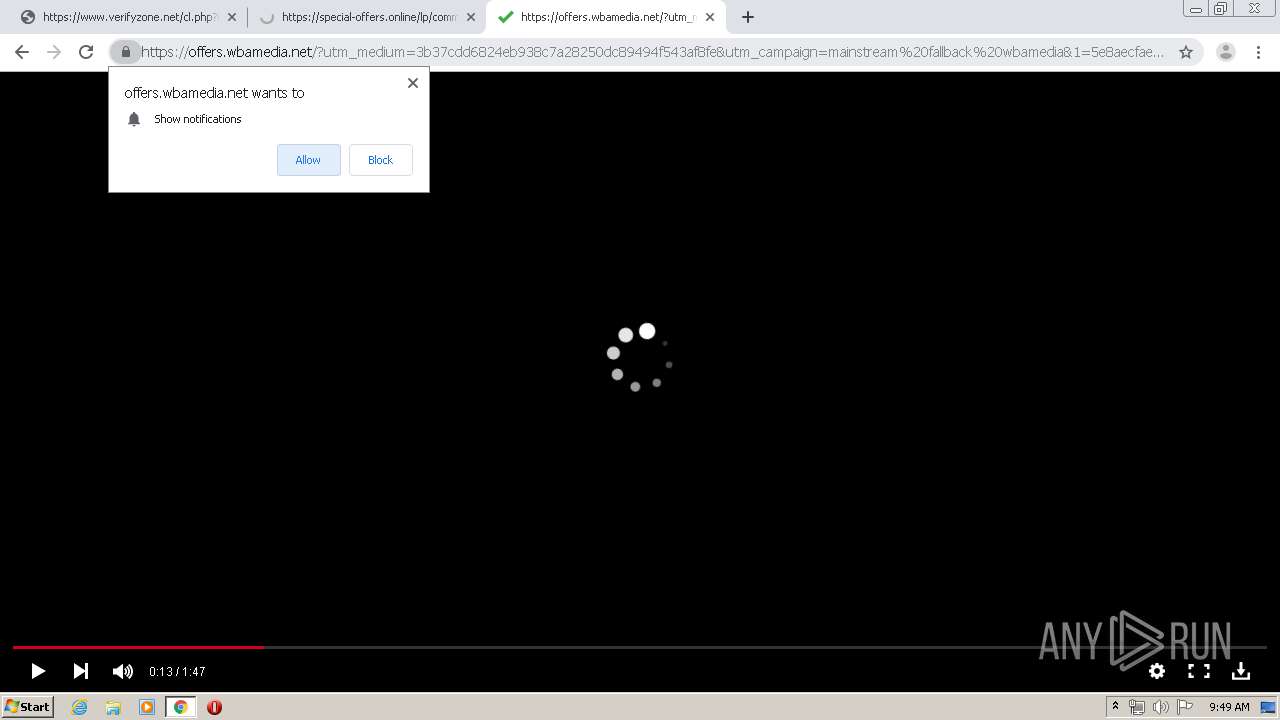
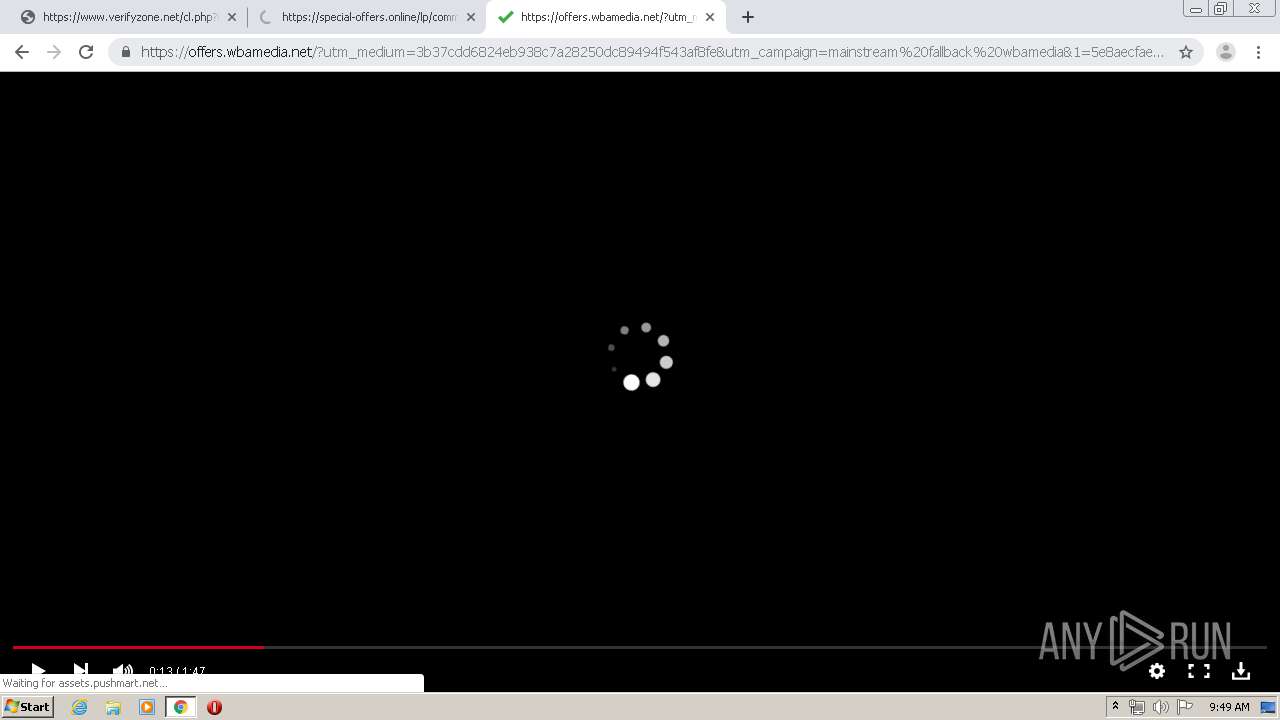
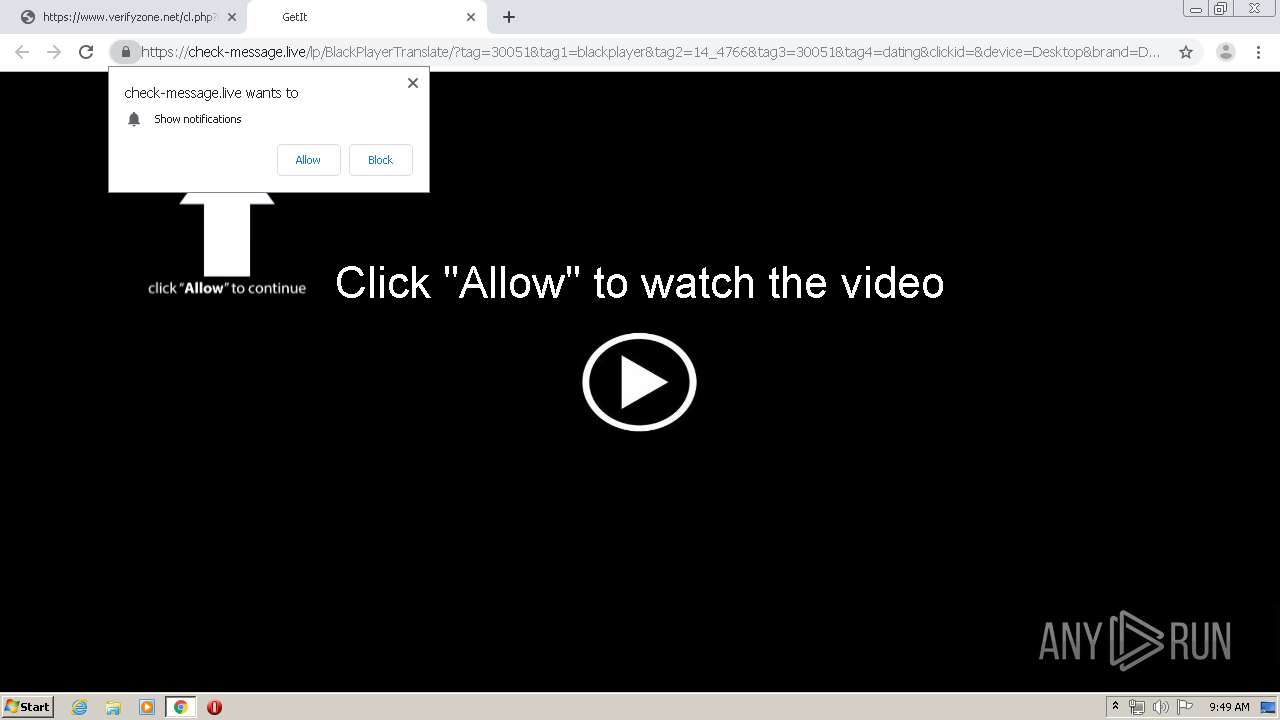
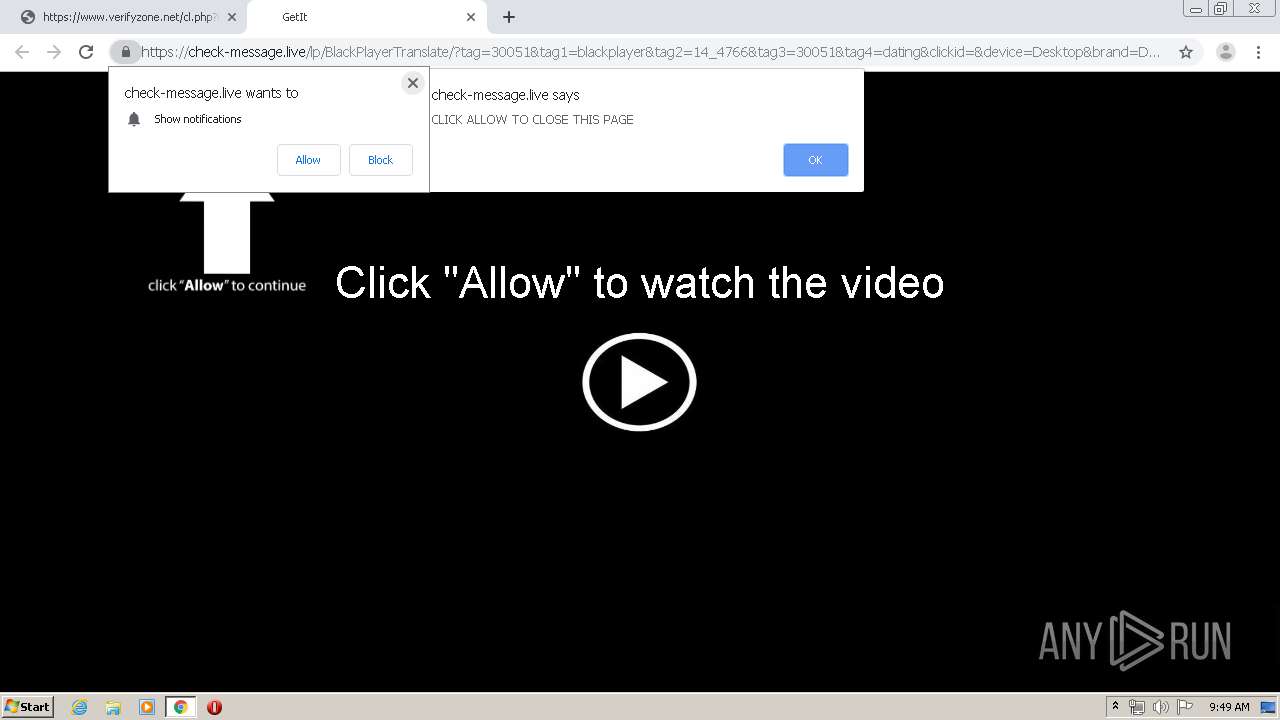
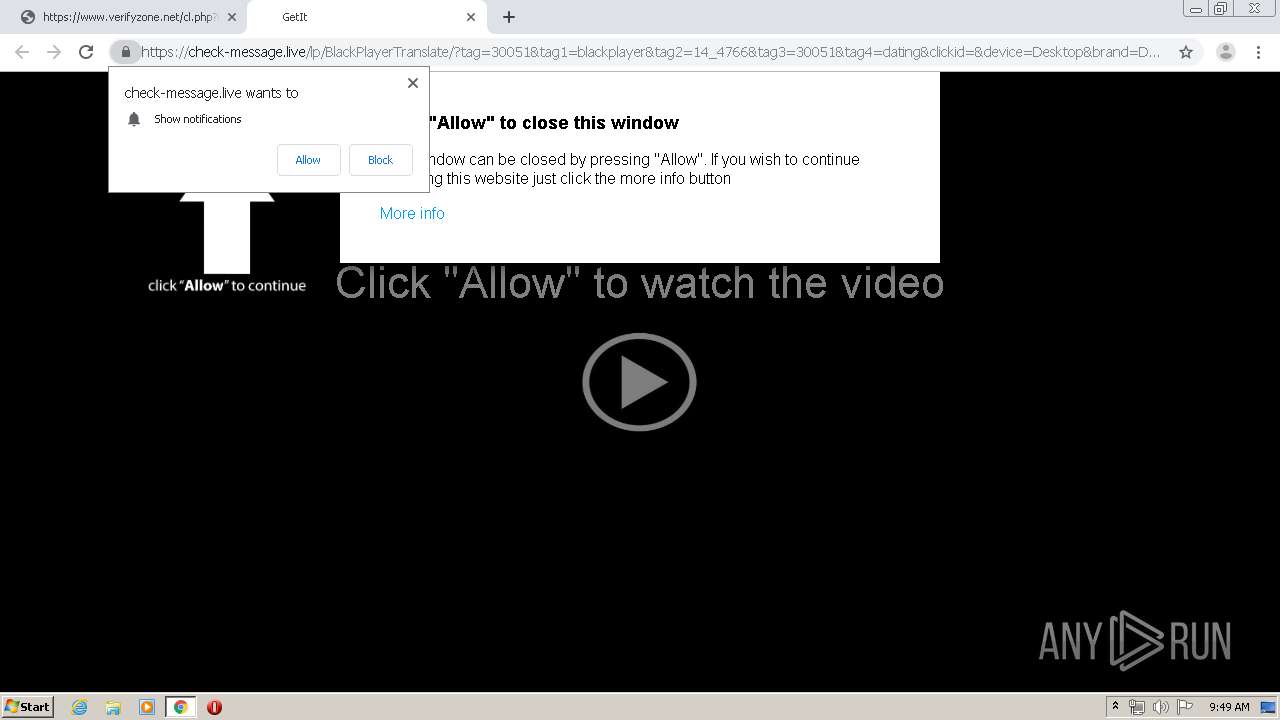
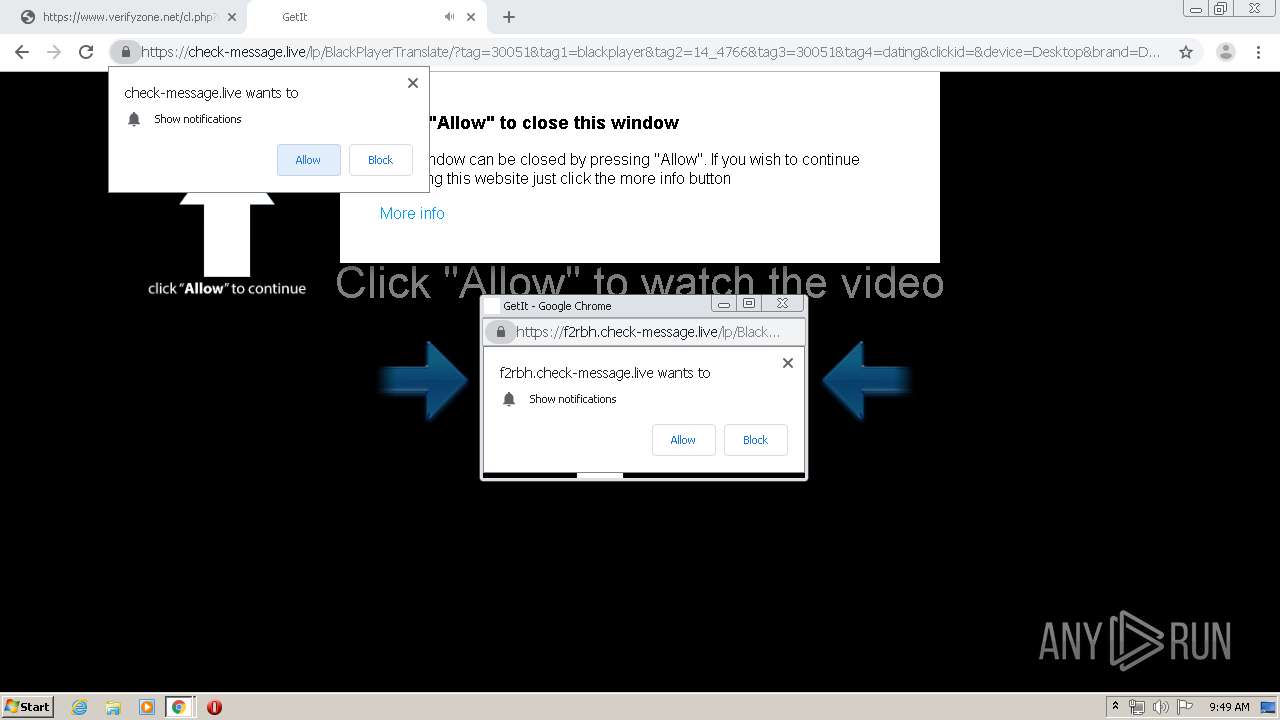
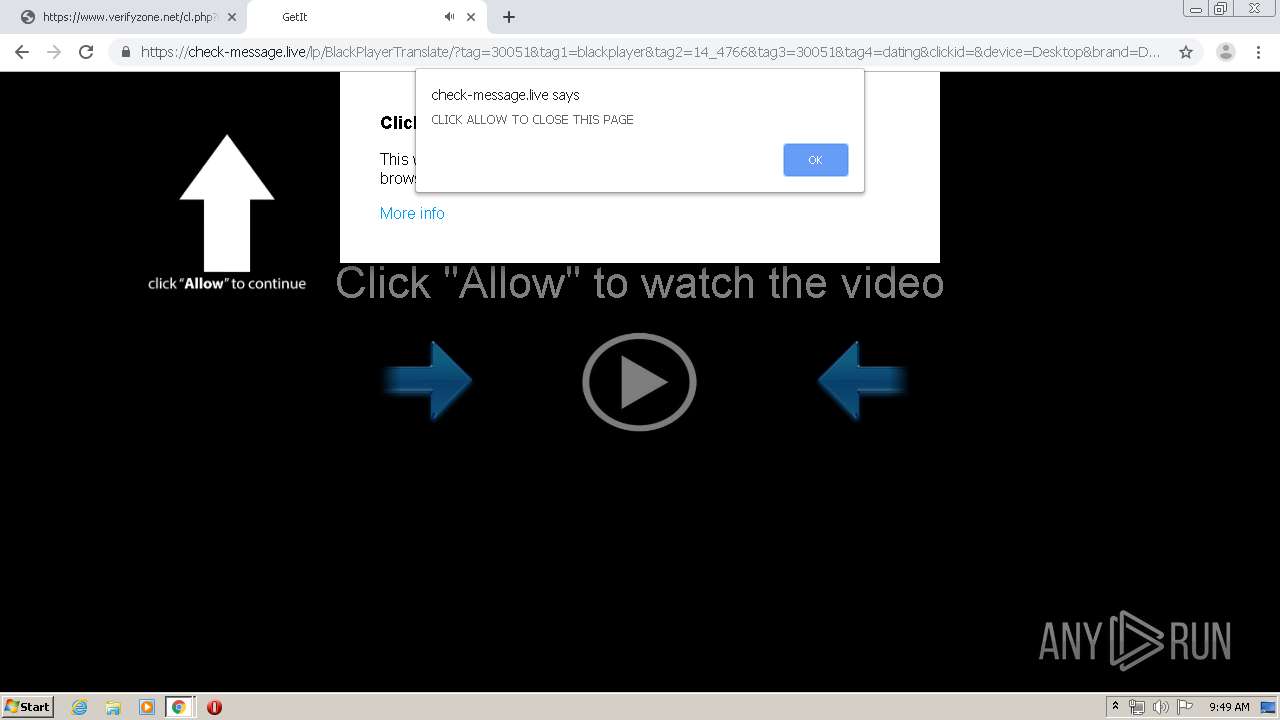
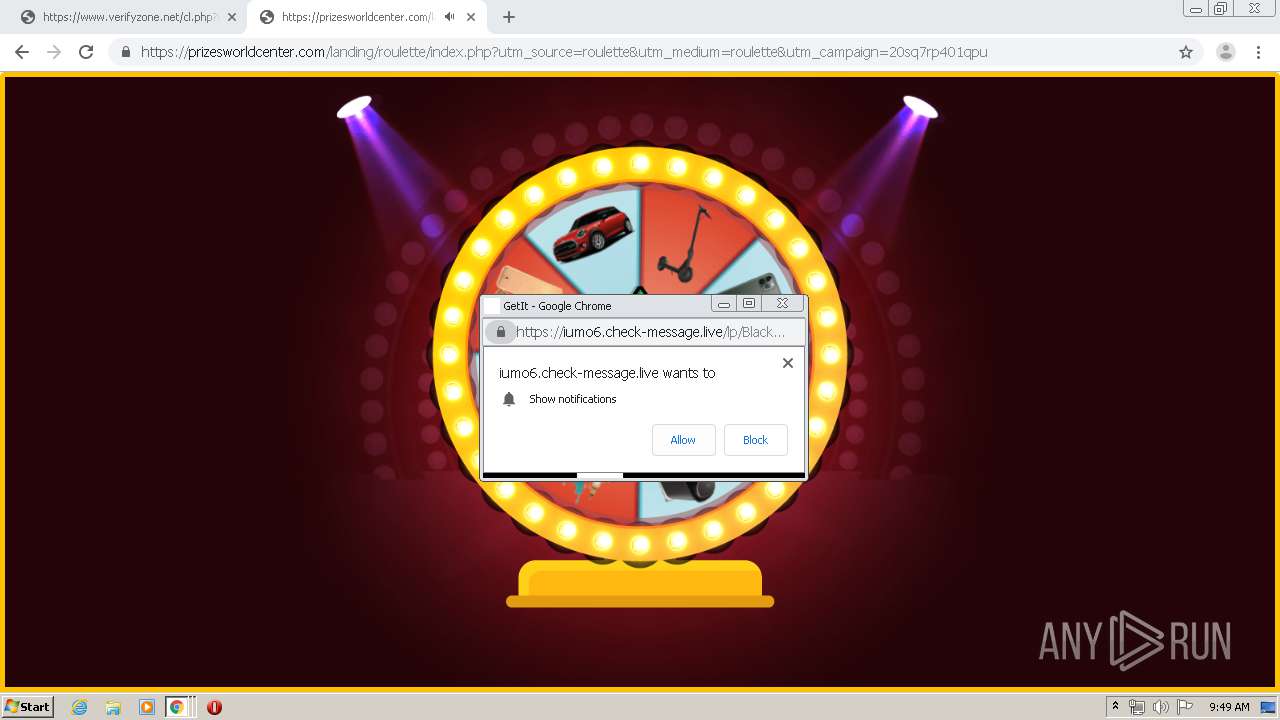
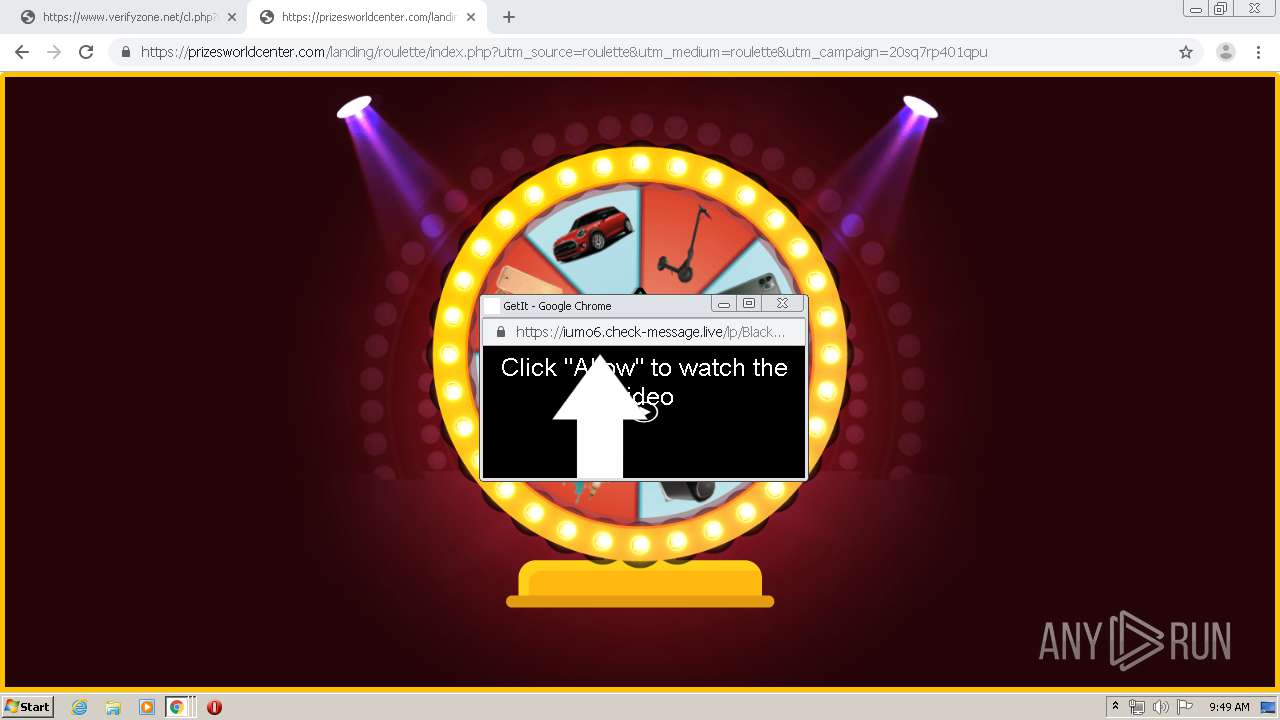
Modifies files in Chrome extension folder
- chrome.exe (PID: 3356)
INFO
Modifies the open verb of a shell class
- chrome.exe (PID: 3356)
Reads the hosts file
- chrome.exe (PID: 3356)
- chrome.exe (PID: 3772)
Creates files in the user directory
- chrome.exe (PID: 3356)
Connects to unusual port
- chrome.exe (PID: 3772)
Application launched itself
- chrome.exe (PID: 3356)
Reads settings of System Certificates
- chrome.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
70
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.verifyzone.net/cl.php?id=4fc8539a88af3b31a6e4a7974c5f1721" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1800 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,9181852089995852554,16459951289571102074,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2808577629392689994 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9181852089995852554,16459951289571102074,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5803274555229981944 --mojo-platform-channel-handle=1644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9181852089995852554,16459951289571102074,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2360167112929230751 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9181852089995852554,16459951289571102074,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1780900075246972876 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9181852089995852554,16459951289571102074,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14462748242630877314 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9181852089995852554,16459951289571102074,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3471698980110348095 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9181852089995852554,16459951289571102074,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9744522937697234961 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
1 102
Read events
923
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
177
Text files
357
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E8AECC1-D1C.pma | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\aa0d73a7-f448-4997-8b9c-48402a7e39c7.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:FC9FFE77348619CC285333DFF5E1D5D1 | SHA256:7CB9B3575330B3D776A21EB7A7407E34F013A0975B7418DA11B5C85DEC91D1F3 | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6e596.TMP | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e596.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 3356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa6e5c4.TMP | text | |
MD5:AC43135B8C9FED46A92448C4E711F45C | SHA256:D840BA7CEBACF86DDBAD75BFB61A53449AA7AE3DE6B8ADC97FE45624626A6F09 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
259
DNS requests
142
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
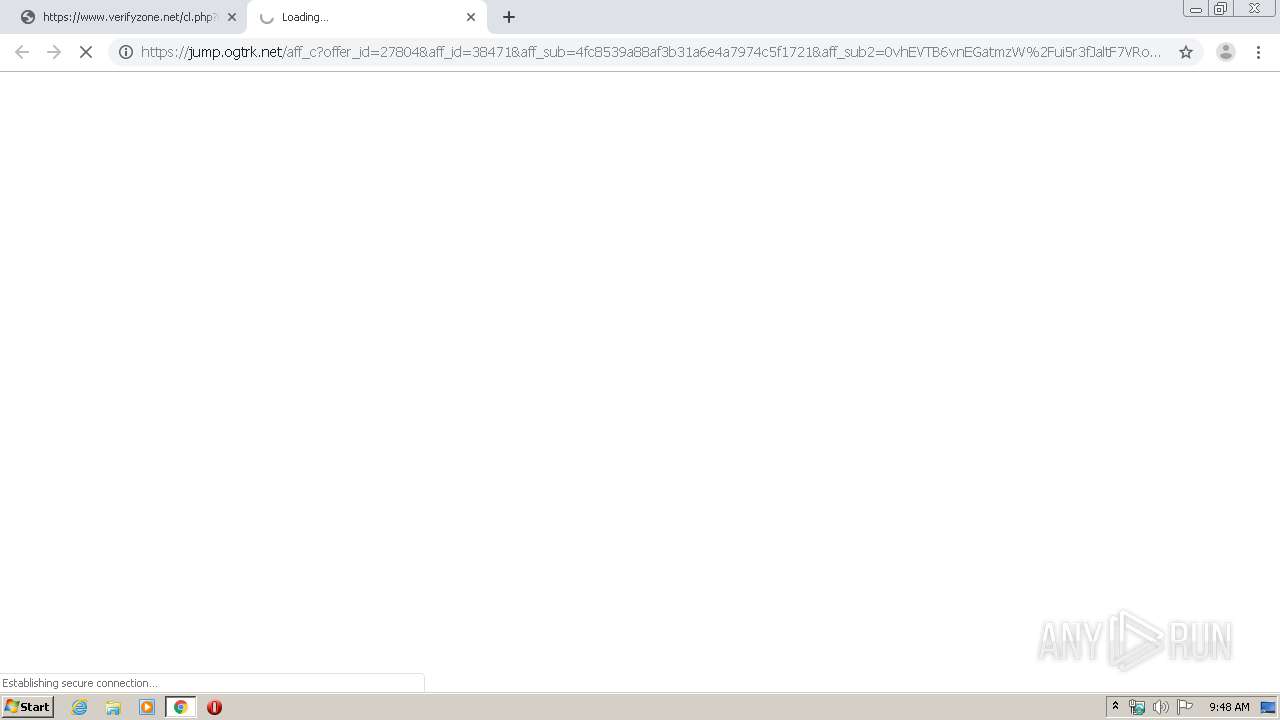
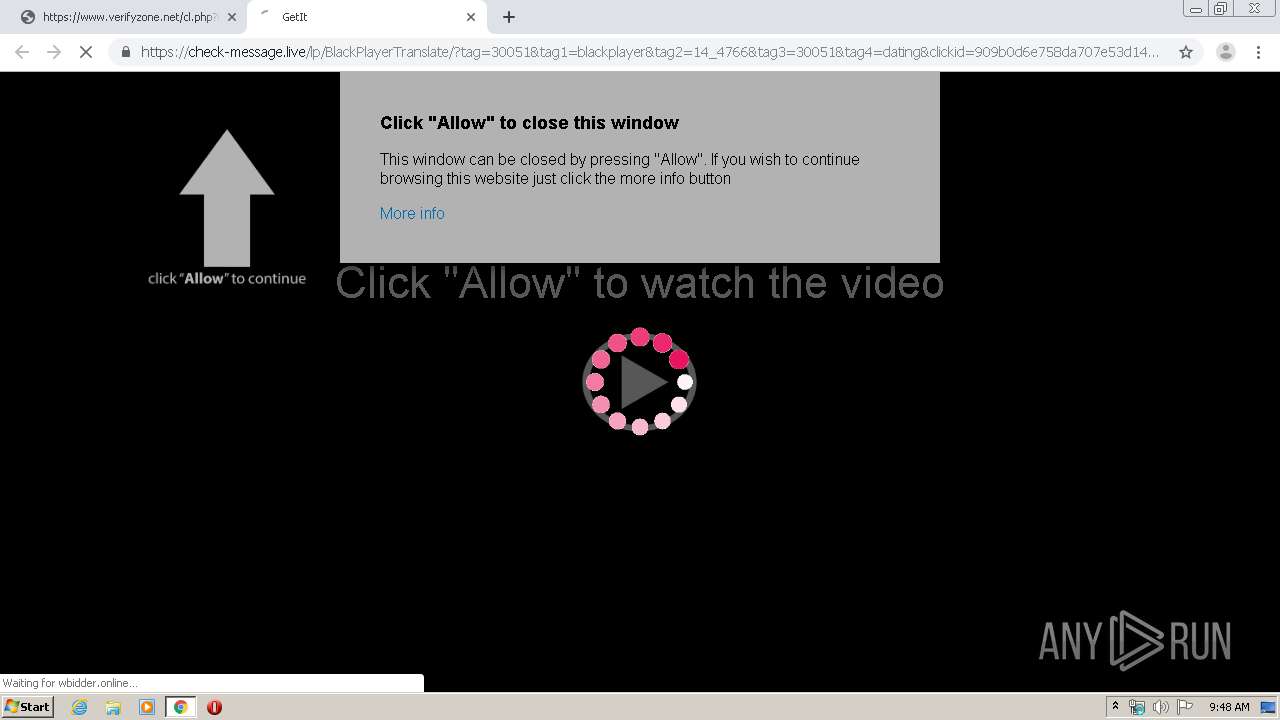
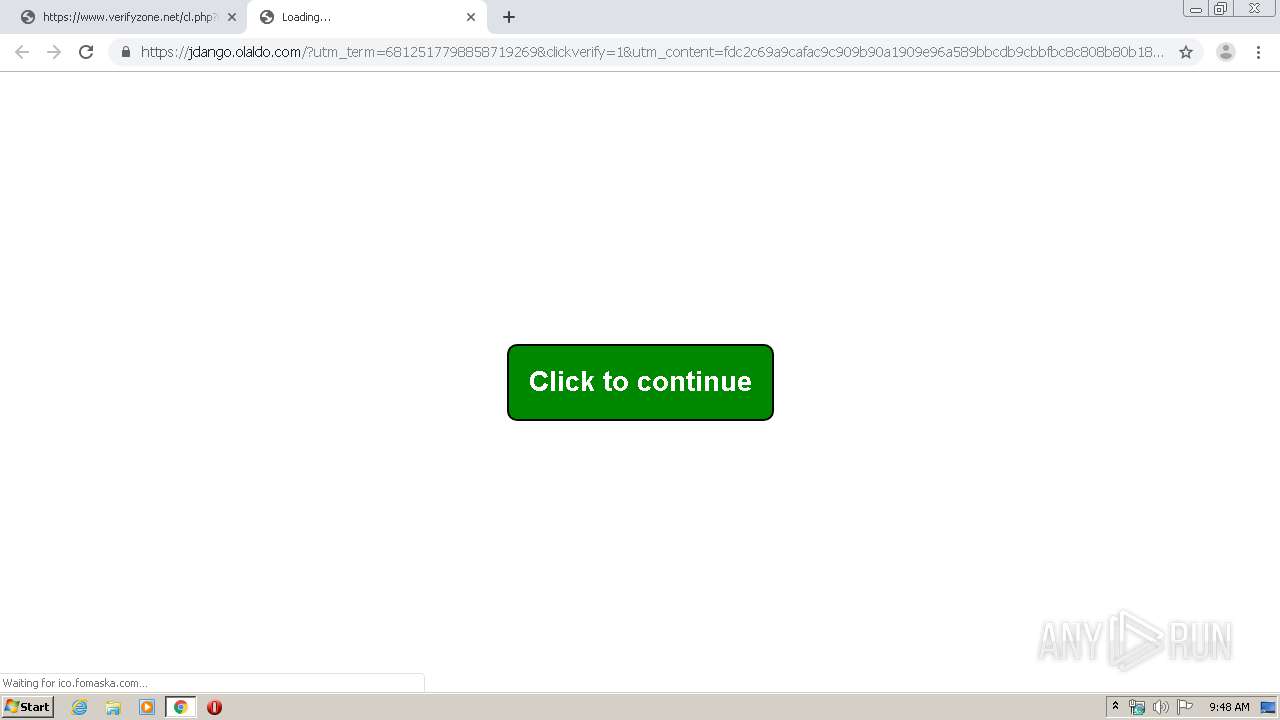
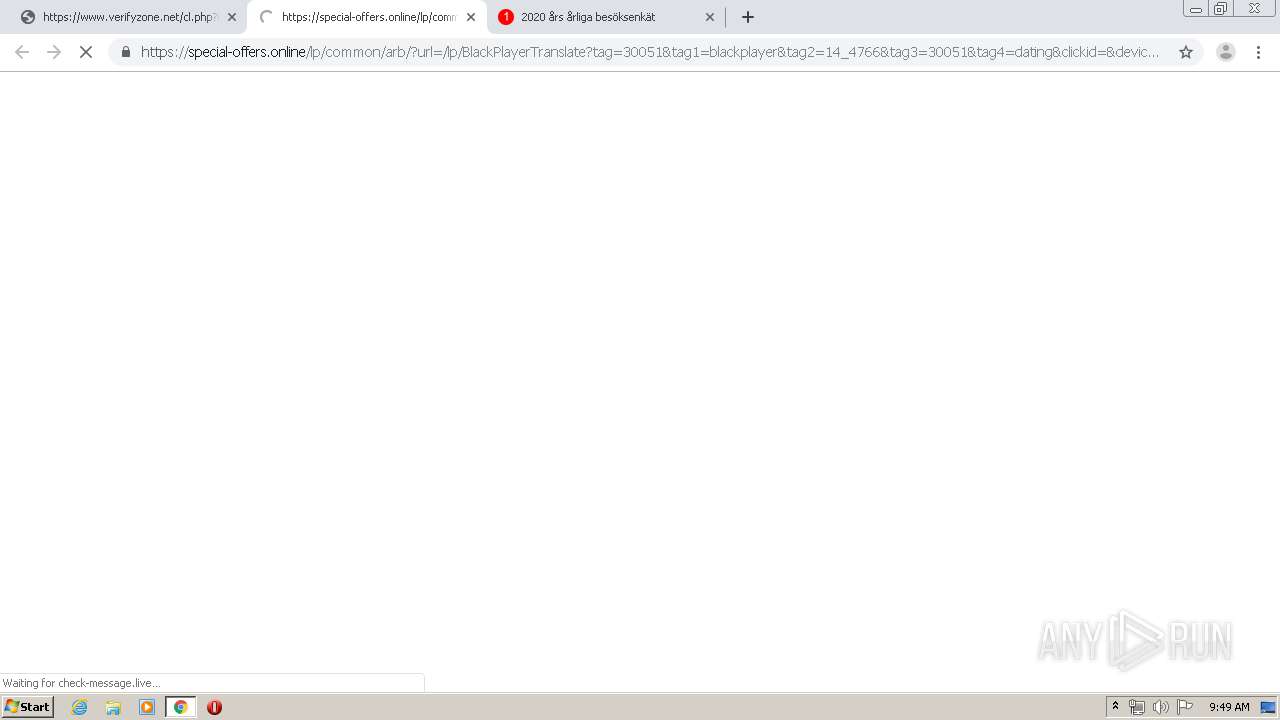
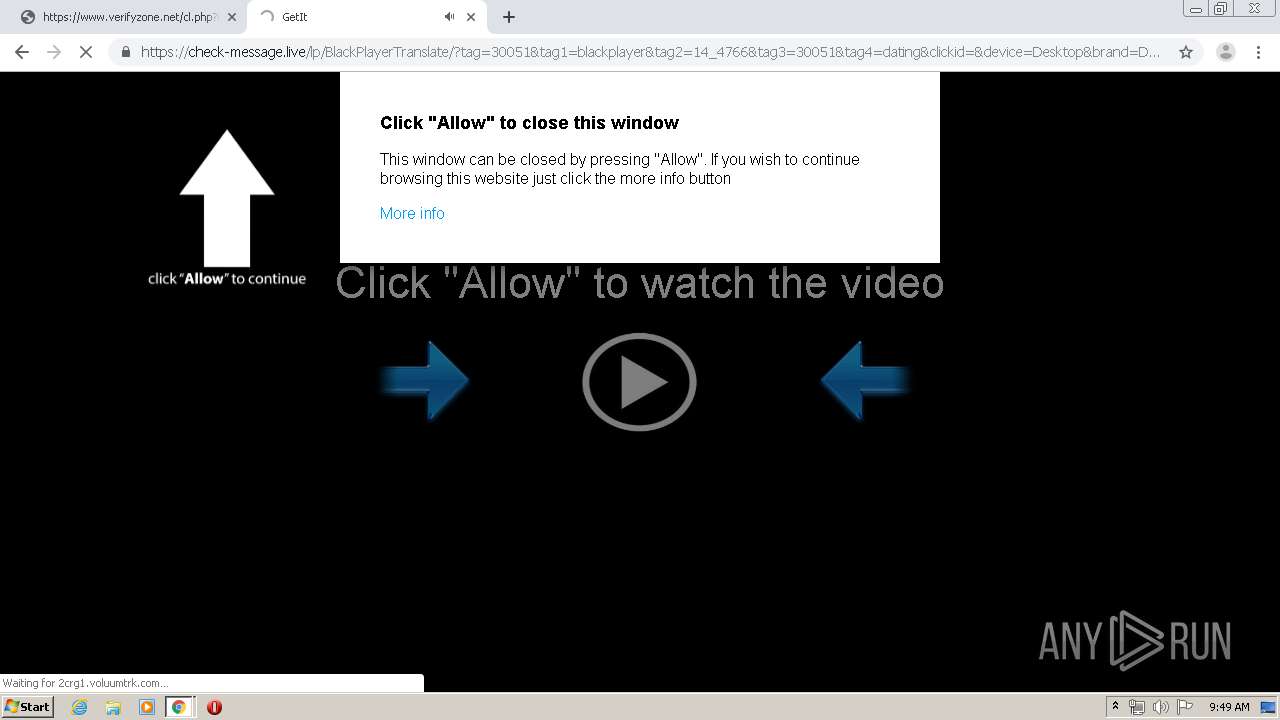
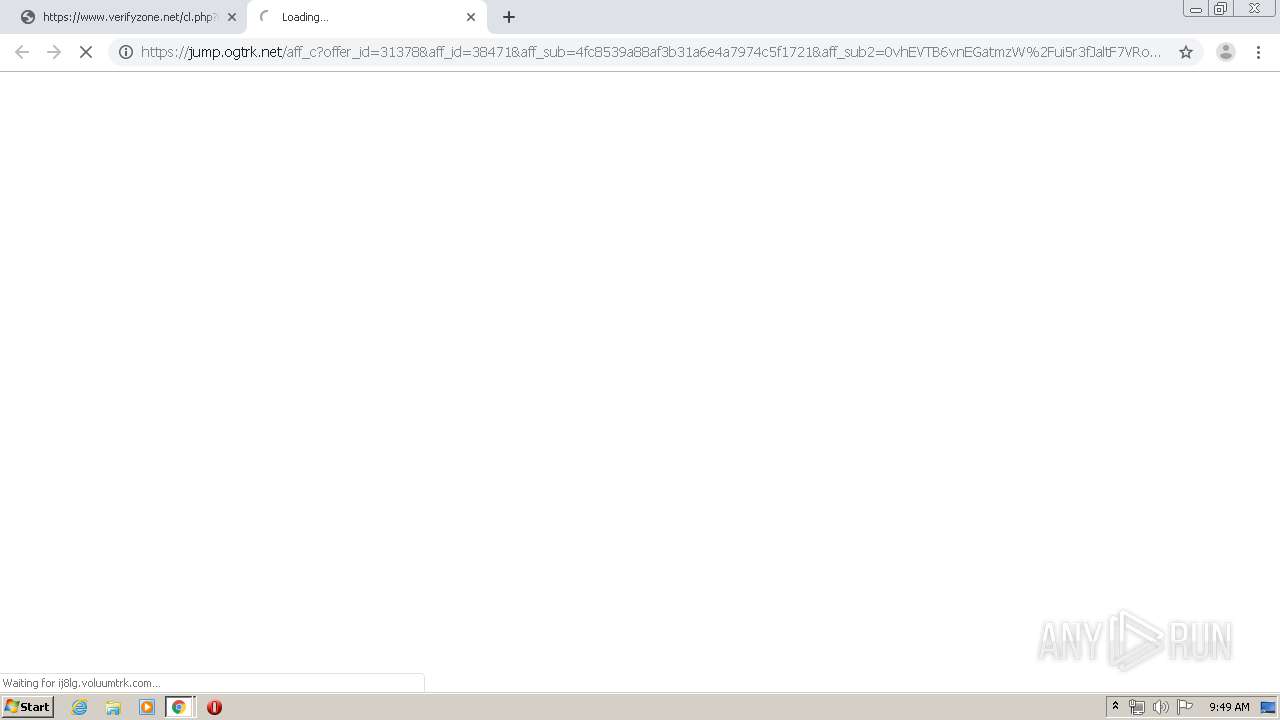
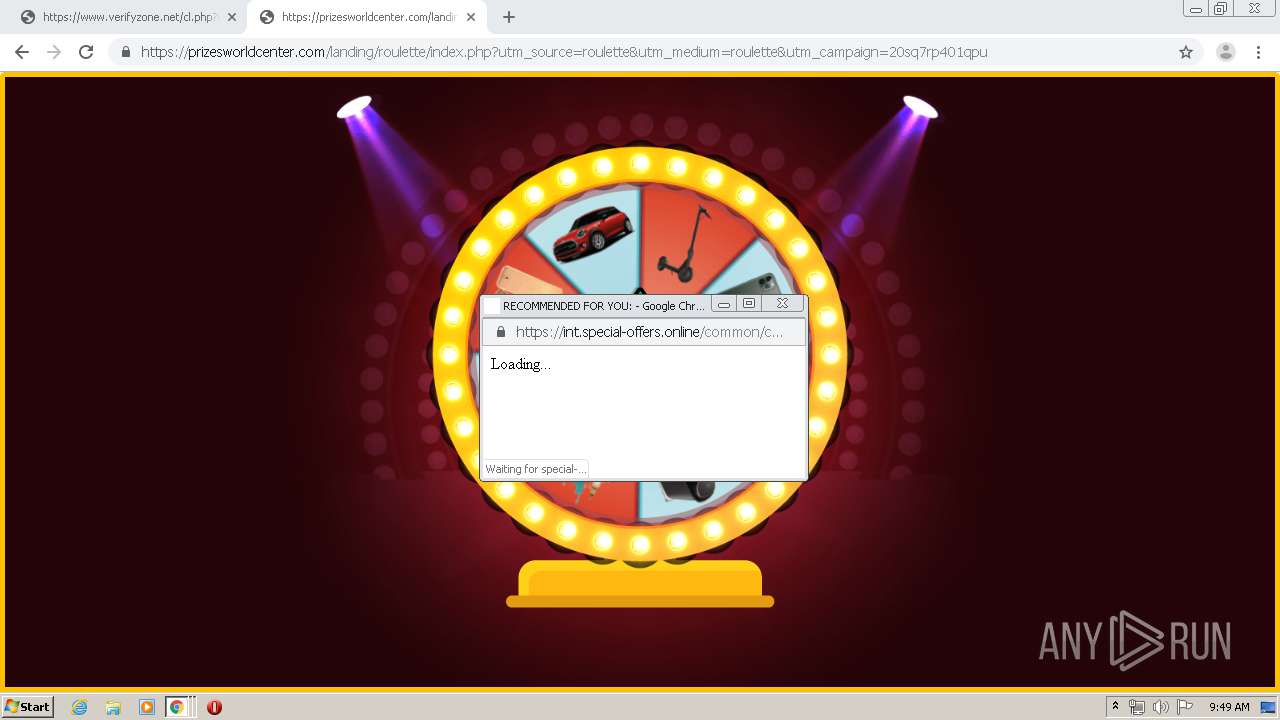
3772 | chrome.exe | GET | 302 | 52.28.111.39:80 | http://2crg1.voluumtrk.com/b228d82f-5b30-40ed-ac2e-434830bd5a51?tag=30051&tag1=blackplayer&tag2=14_4766&tag3=30051&tag4=dating&clickid=&device=Desktop&brand=Desktop&model=Desktop&country=SE&affid=30051&subid=14_4766&ln=en&cid=bae44fdadfabab4f0254e22e4b694985-4888-0406&useragent=%7Bvar:useragent%7D&ip=84.17.36.75&bv=Chrome%2075&as=pc | DE | — | — | suspicious |
3772 | chrome.exe | GET | — | 104.18.61.20:80 | http://fomaska.com/portent/netbios/acl/1-18131-70f55a7d35992e97028a4f444cbbd3c9?tvu=Mainstream&clickid=5d0a0786-77e3-11ea-a152-114ffeb08773&ext1=14460_bid_30420&ext2=144924 | US | — | — | unknown |
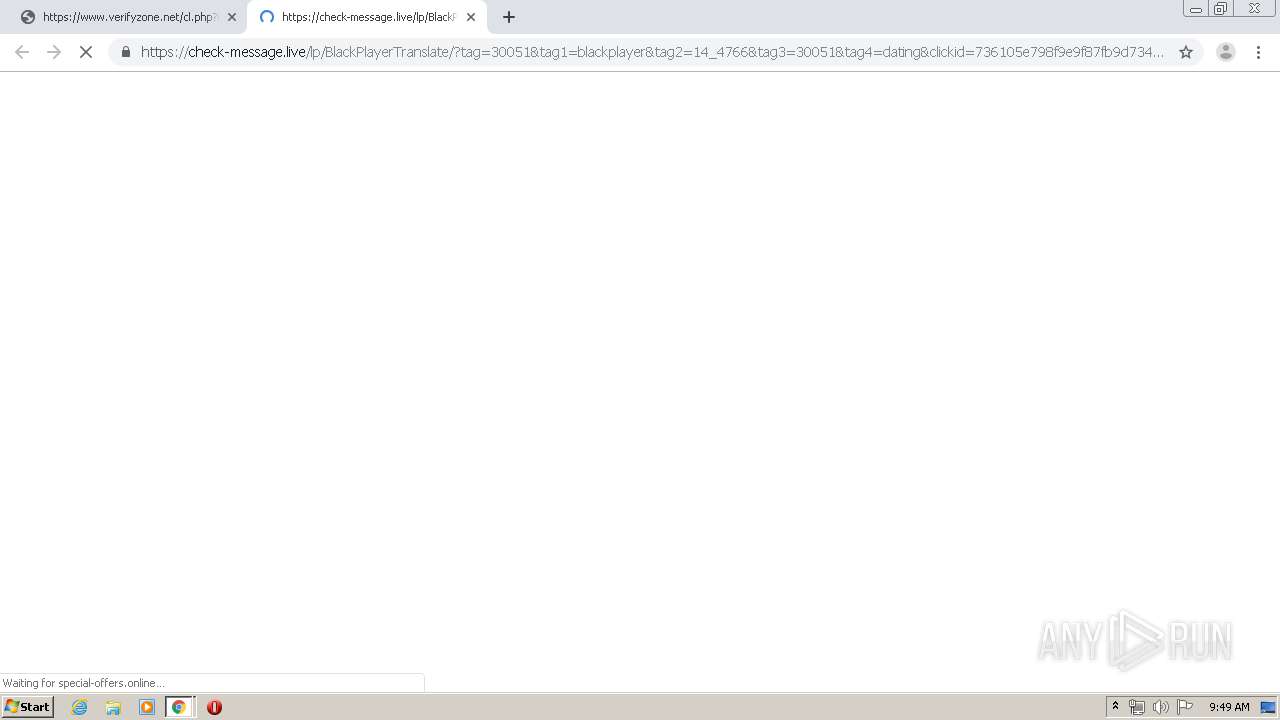
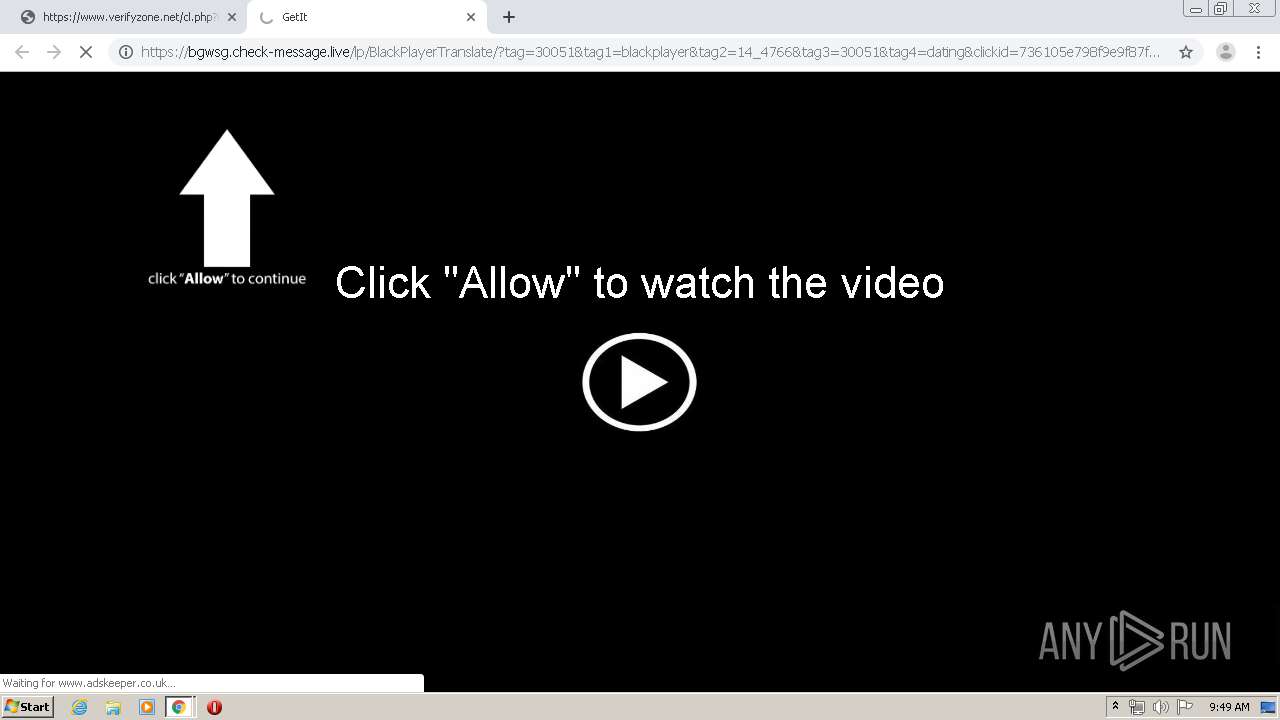
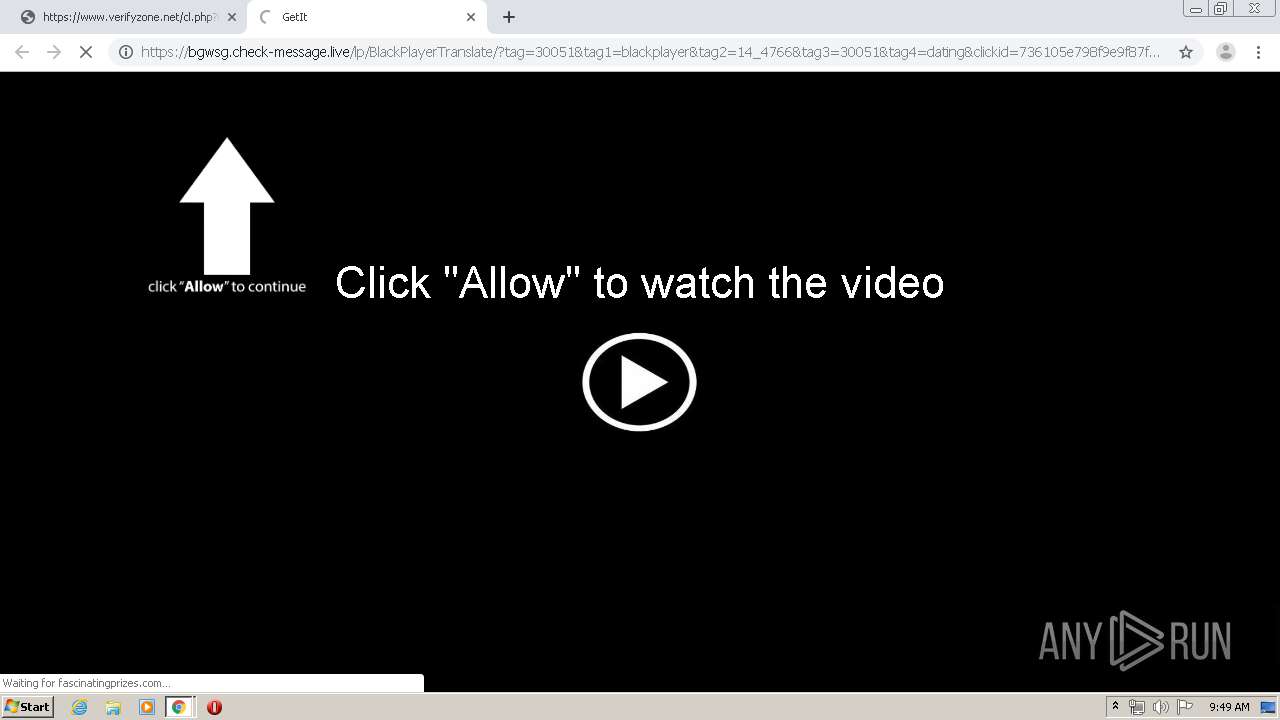
3772 | chrome.exe | GET | 302 | 52.28.111.39:80 | http://2crg1.voluumtrk.com/b228d82f-5b30-40ed-ac2e-434830bd5a51?tag=30051&tag1=blackplayer&tag2=14_4766&tag3=30051&tag4=dating&clickid=736105e798f9e9f87fb9d734623f0f7b-4888-0406&device=Desktop&brand=Desktop&model=Desktop&country=SE&affid=30051&subid=14_4766&ln=en&cid=736105e798f9e9f87fb9d734623f0f7b-4888-0406&useragent=%25257Bvar%253Auseragent%25257D&ip=84.17.36.75&bv=Chrome%25252075&as=pc&b=2&blkt=1&blk=0&onw=1&link=https%3A%2F%2Fclk.wbidder.online%2Fredirect%3Furl%3D%252F%252Fwww.adskeeper.co.uk%252Fghits%252Fd%252F600271%252Fi%252F68801%252Fsrc%252F1674573873%252Fpp%252F1%252F1%253Fh%253Dx0qb68hk4ygAdi3WW3kptH_OV7-2ZUprBQNwVUhWk7Xe2AKRtg22BFqnKHRAYRZX%2526rid%253D8f1e5d21-77e3-11ea-a01f-e4434b3ed018%2526u%253DMfS0nEqBTle574tZlBekhLJ7GbhtyEzG0u39taiy_w17IPBZILSplo1amBFNFhaJTgP433nnjQ0pqpIQKMTrew**%2526tt%253DDirect%2526cp%253D153%2526pubsrcid%253Dbid_30182%2526cpm%253D1%26s%3D1003%26a%3Dbid_onw_30051%26sub%3D14_4766%26ts%3D1586162984%26d%3D1%26c%3D213816410777 | DE | — | — | suspicious |
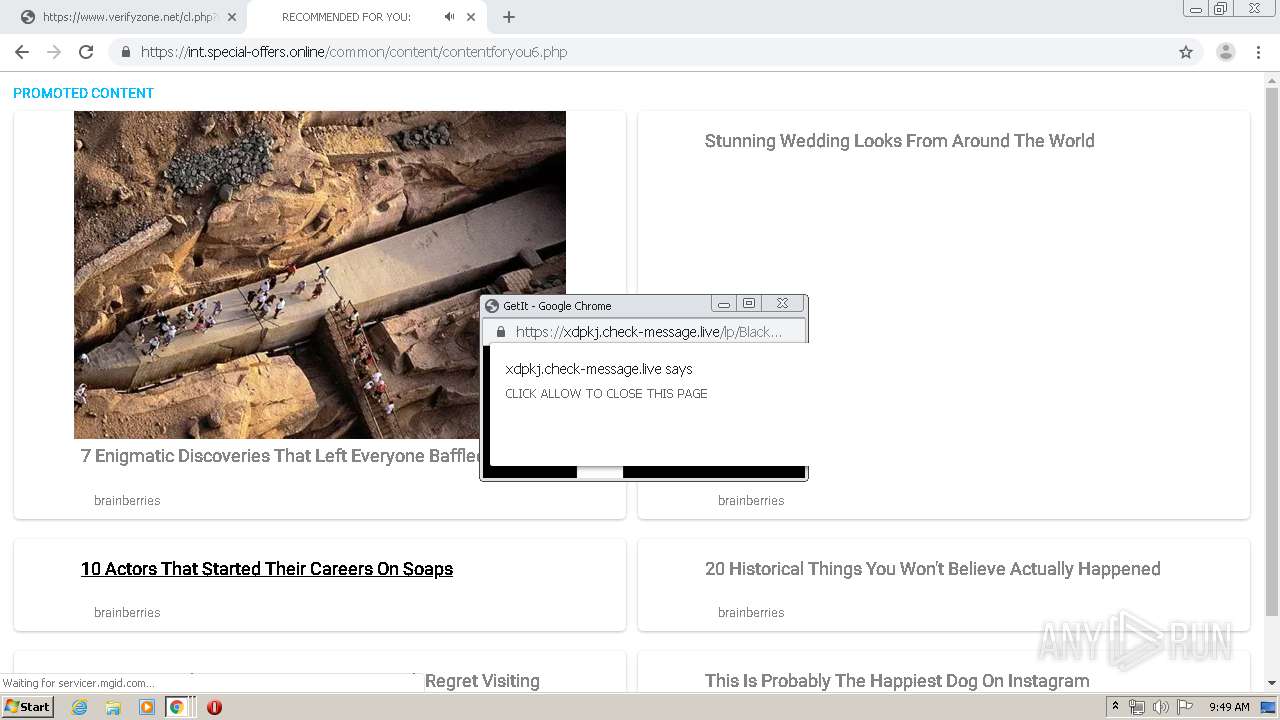
3772 | chrome.exe | GET | 302 | 52.28.111.39:80 | http://2crg1.voluumtrk.com/b228d82f-5b30-40ed-ac2e-434830bd5a51?onw=1&link=https%3A%2F%2Fclk.wbidder.online%2Fredirect%3Furl%3Dhttps%253A%252F%252Fint.special-offers.online%252Fcommon%252Fcontent%252Fcontentforyou5.php%253Faffid%253Dbid_undefined%2526subid%253Dundefined%2526isClient%253D1%2526r%253D1586162990.0.01668135848804808%26s%3DDEFAULT%26a%3Dbid_onw_undefined%26sub%3Dundefined%26ts%3D1586162990%26d%3D74%26c%3D02631784480 | DE | — | — | suspicious |
3772 | chrome.exe | GET | 200 | 104.18.61.20:80 | http://fomaska.com/portent/netbios/acl/1-18131-70f55a7d35992e97028a4f444cbbd3c9?tvu=Mainstream&clickid=5d0a0786-77e3-11ea-a152-114ffeb08773&ext1=14460_bid_30420&ext2=144924 | US | compressed | 1.46 Kb | unknown |
3772 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
3772 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
3772 | chrome.exe | GET | 200 | 173.194.150.231:80 | http://r1---sn-2gb7sn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=84.17.36.75&mm=28&mn=sn-2gb7sn7s&ms=nvh&mt=1586162776&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3772 | chrome.exe | GET | 200 | 190.93.246.34:80 | http://cdn.runative-syndicate.com/images/c/2/6152eaaed55e4ead11e214eb12a8f8118c6cb9.jpg | unknown | image | 87.3 Kb | whitelisted |
3772 | chrome.exe | GET | 502 | 104.18.60.20:80 | http://ico.fomaska.com/kt/se/74/favicon.ico | US | html | 4.00 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3772 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 162.247.242.21:443 | bam.nr-data.net | New Relic | US | whitelisted |
3772 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 104.28.29.239:443 | bootstraplugin.com | Cloudflare Inc | US | shared |
3772 | chrome.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
3772 | chrome.exe | 143.204.101.121:443 | d2wy8f7a9ursnm.cloudfront.net | — | US | unknown |
3772 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
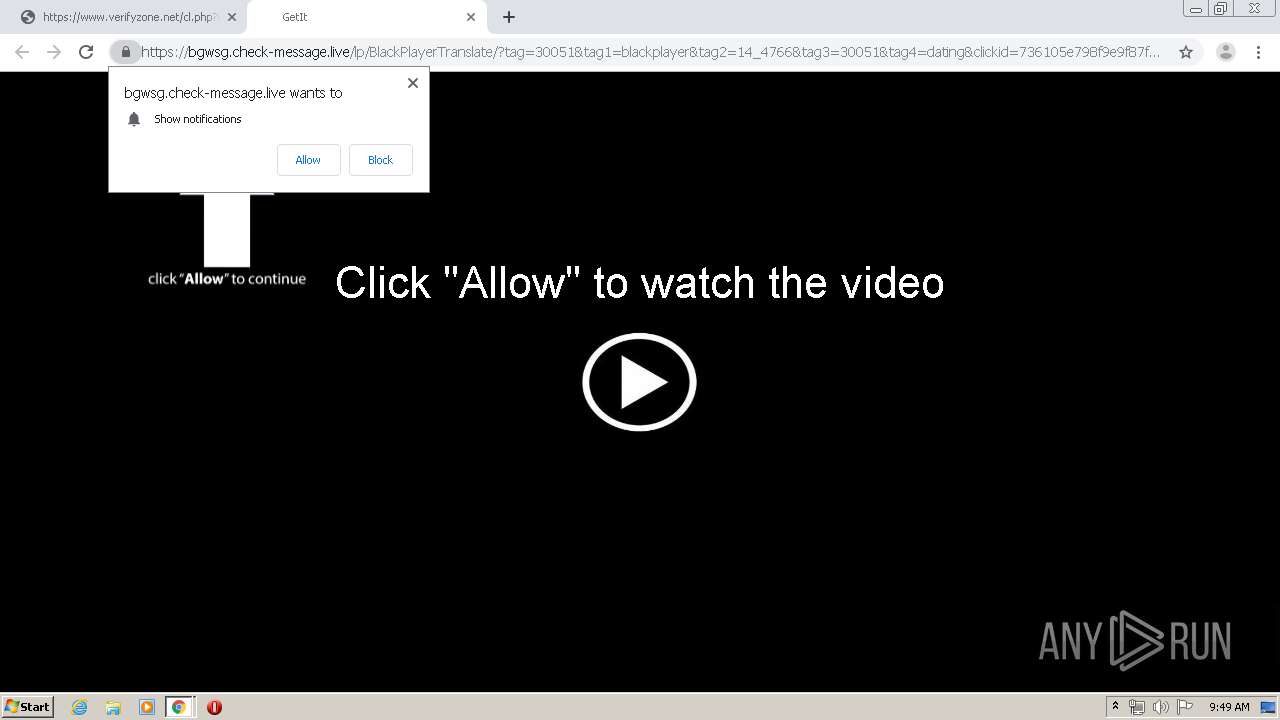
3772 | chrome.exe | 3.225.87.211:443 | www.verifyzone.net | — | US | suspicious |
3772 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3772 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.verifyzone.net |
| suspicious |
accounts.google.com |
| shared |
d2wy8f7a9ursnm.cloudfront.net |
| shared |
sessions.bugsnag.com |
| shared |
js-agent.newrelic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
s3.amazonaws.com |
| shared |
bam.nr-data.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
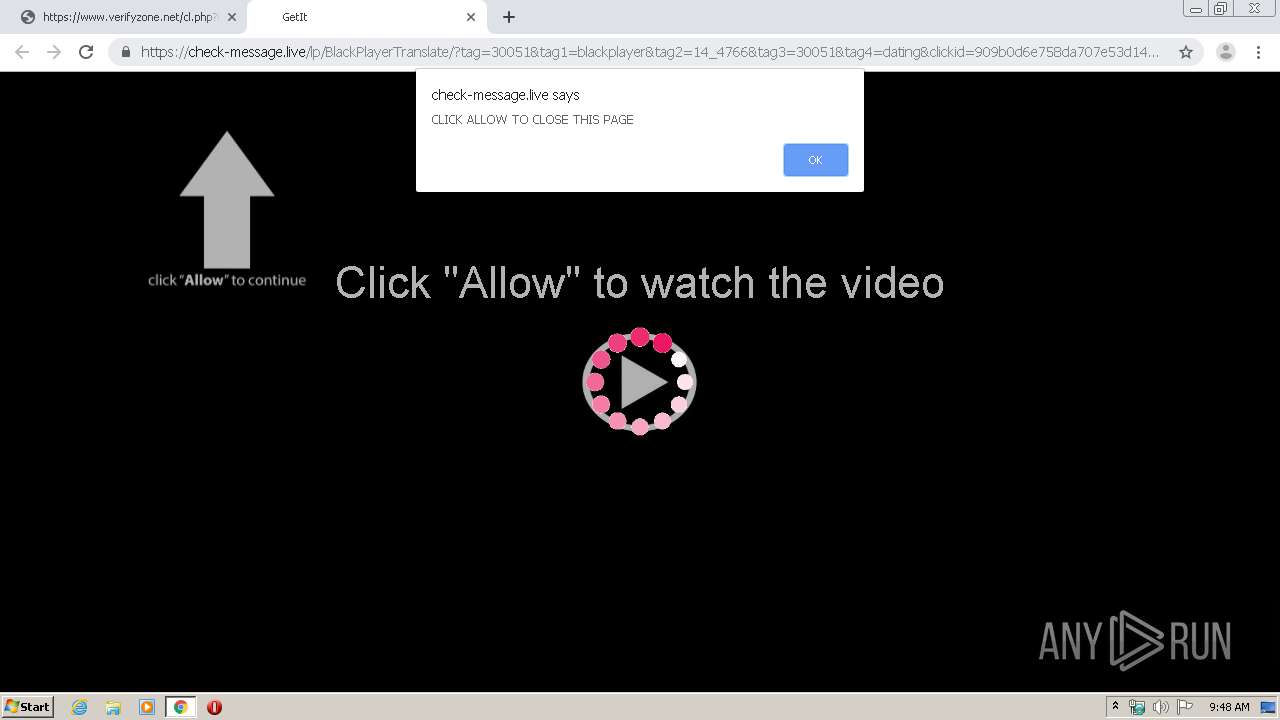
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
3772 | chrome.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 24 |
1 ETPRO signatures available at the full report